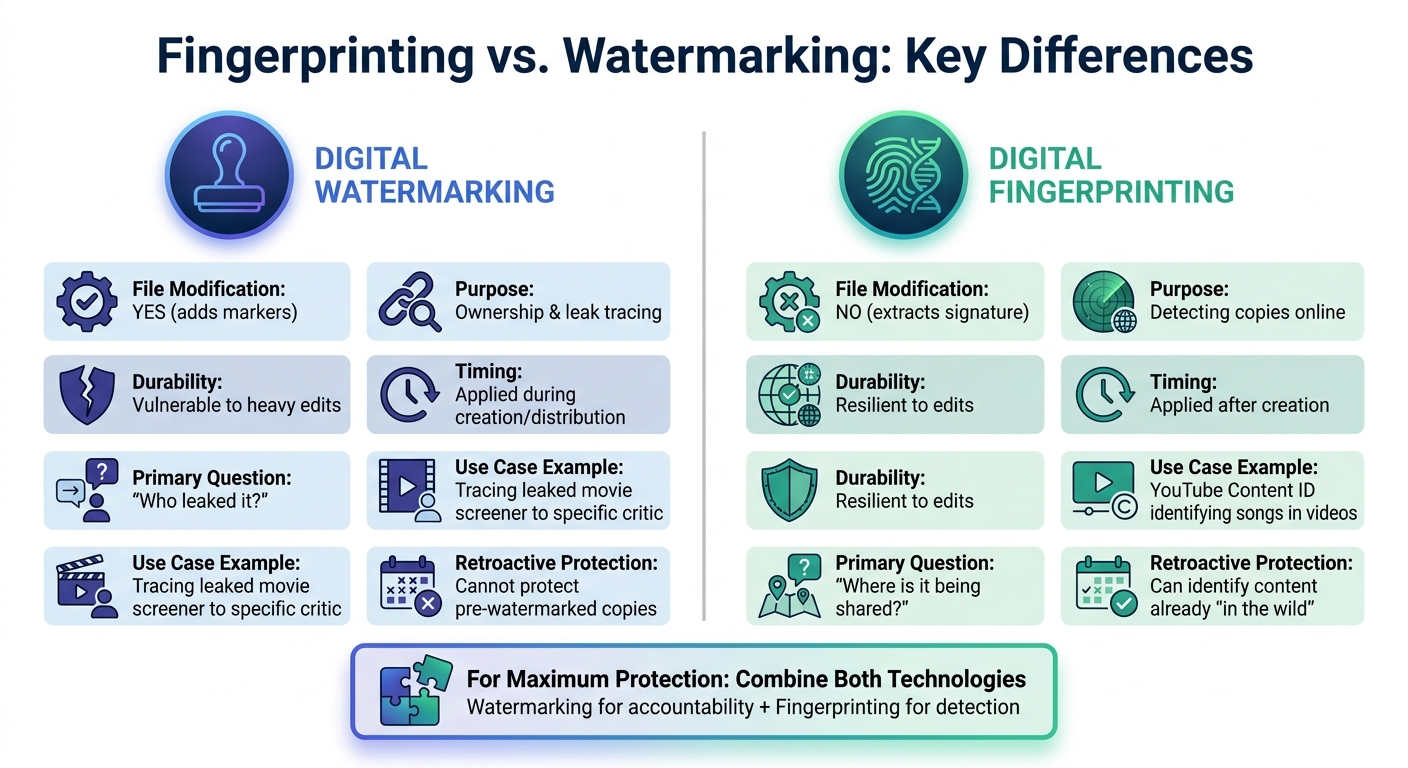
Fingerprinting and watermarking are two distinct technologies for protecting digital content, each serving different purposes:
- Fingerprinting creates a unique signature from a file’s features (like audio patterns or visual frames) without altering it. It helps detect where your content is being shared, even after edits like cropping or compression.
- Watermarking embeds visible or invisible markers into the file to establish ownership or trace leaks. Invisible watermarks can link leaked content to specific users or sessions.
Key Points:
- Fingerprinting is ideal for identifying modified content across platforms.
- Watermarking is best for tracing leaks to specific sources.
- Both methods work together to strengthen content protection.
Quick Comparison:
| Aspect | Digital Watermarking | Digital Fingerprinting |
|---|---|---|
| File Modification | Yes (adds markers) | No |
| Purpose | Ownership & leak tracing | Detecting copies online |
| Durability | Vulnerable to heavy edits | Resilient to edits |
| Timing | Applied during creation/distribution | Applied after creation |
| Primary Question | "Who leaked it?" | "Where is it being shared?" |
For maximum protection, combine both: watermarking for accountability and fingerprinting for detection.
Digital Fingerprinting vs Watermarking: Side-by-Side Comparison
How Digital Fingerprinting Works
The Fingerprinting Process
Digital fingerprinting works by analyzing a file’s inherent characteristics instead of altering it in any way. It examines elements like audio waveforms, visual frame sequences, or motion vectors and translates these into a compact digital signature – or hash – that acts as a unique identifier. This identifier is then stored in a reference database for future comparisons [2][4].
"Fingerprinting is an automated process that takes an existing image file, hashes it and converts it to a unique fingerprint." – Jonathan Bailey, Plagiarism Today [3]
When searching for unauthorized use, the system compares the fingerprints of online content to those in the database. The technology is designed to recognize content even after modifications, such as cropping, compression, color adjustments, re-encoding, frame rate changes, subtitle overlays, or slight speed shifts [2][4].
Because fingerprinting doesn’t alter the original file, the content stays untouched, and the fingerprint is impossible to remove – it’s derived from the content’s unique structure [4]. This means fingerprinting can be applied retroactively to already-distributed content without requiring any pre-processing [3]. Its ability to withstand alterations makes it highly effective for detecting unauthorized use in various scenarios. This is particularly critical for detecting unauthorized distribution of digital textbooks and other educational materials.
Common Uses of Fingerprinting
Major streaming platforms like Netflix, Disney+, and Amazon Prime Video use fingerprinting to search for pirated clips online, even when those clips have been re-encoded or modified with overlays [4]. YouTube’s Content ID system employs this technology to identify copyrighted audio and video in user uploads, even if the content has been trimmed or altered [4].
Music services utilize fingerprinting to recognize songs based on their unique sound patterns – such as frequency, pitch, and rhythm. Stock media companies like Shutterstock and Getty Images use it to track down reused images across the web, even when watermarks have been removed or the images have been filtered or resized [4]. Sports organizations like the NBA and FIFA rely on fingerprinting to detect and remove unauthorized clips shared on social media platforms during live events [4].
"Fingerprinting is what you rely on when content gets out and there’s no watermark to trace." – FastPix [4]
In short, fingerprinting plays a key role in protecting digital content by reliably identifying and addressing unauthorized use.
sbb-itb-738ac1e
Forensic Watermarking for Video Protection | How It Works & Why It’s Essential
How Watermarking Works
Watermarking serves as a complementary approach to digital fingerprinting by embedding ownership information directly into the content itself.
This technique works by inserting signals into a media file – whether in its pixels, waveforms, or layers. Unlike metadata stored in file headers, these embedded marks remain intact even after re-encoding, format changes, or compression.
"Invisible digital watermarking answers this question by embedding machine readable signals directly into the media signal in a way that typical viewers or listeners cannot perceive, yet specialised detectors can recover and verify later." – Nikhil John, InCyan [1]
Watermarking aims to strike a balance between three key factors: imperceptibility (ensuring content quality remains unaffected), robustness (resisting edits or transformations), and capacity (carrying sufficient data) [1]. Modern techniques use perceptual modeling to hide data in areas less noticeable to human senses, such as textured parts of images or audio frequencies masked by louder sounds [1].
Types of Watermarks
- Visible Watermarks
These are the most recognizable type – logos or text overlays placed directly on content. They serve as branding tools and a deterrent against casual piracy [4]. However, they are vulnerable to removal through cropping, blurring, or AI-based editing tools, which limits their effectiveness for serious copyright enforcement [4]. - Invisible Watermarks (Forensic Watermarks)
These marks are embedded within the media signal itself and remain undetectable to viewers [1]. Acting like a hidden serial number, they can survive various transformations, including cropping, compression, and rotation [1]. Using "blind detection", these watermarks can be retrieved without needing access to the original, unmarked file – only the suspect content and a secret key are required [1]. - Fragile Watermarks
Designed to break or disappear if the content is altered, fragile watermarks are ideal for ensuring the integrity of sensitive materials like documents or medical images [4].
| Watermark Type | Primary Purpose | Visibility | Robustness |
|---|---|---|---|
| Visible | Branding & Deterrence | High | Low (Easy to crop/blur) |
| Invisible (Forensic) | Traceability & Ownership | None | High (Survives compression) |
| Fragile | Tamper Detection | None | Very Low (Designed to break) |
Each type serves specific needs, from deterring piracy to establishing ownership or ensuring content integrity.
Common Uses of Watermarking
Streaming platforms like Netflix, Disney+, and Amazon Prime Video rely on forensic watermarking to safeguard pre-release content and trace leaks back to specific user accounts [4]. By embedding unique identifiers – such as user IDs or session timestamps – these platforms can identify the source of a leak.
Stock photo agencies often use visible watermarks on preview images to prevent unauthorized downloads while still allowing potential buyers to evaluate the content. Once purchased, the watermark-free version is provided. News outlets and content creators often combine visible watermarks with invisible forensic marks for added security on premium or embargoed material [4].
One standout solution is InCyan’s Tectus, which specializes in blind watermarking. This technology embeds invisible, legally defensible ownership data into images, video, and audio. It’s particularly useful in high-stakes scenarios where pinpointing the source of a leak is critical, all without degrading the user experience.
Main Differences Between Fingerprinting and Watermarking
Watermarking involves embedding a visible or invisible signal into content during its creation or distribution, while fingerprinting works by extracting a unique signature from the content’s inherent features – without altering it [5][6]. Essentially, watermarking is a proactive measure applied during content production to enable future tracking, whereas fingerprinting is a reactive method that identifies content by comparing it to a database of original files [5]. Watermarking requires integration into the content creation process, while fingerprinting relies on maintaining a robust library of master files for comparison.
"Watermarking modifies content to enable tracking; fingerprinting recognizes content without modifying it." – Sider.ai [5]
Watermarking is particularly effective for tracing unauthorized sharing by linking content to specific users or sessions. On the other hand, fingerprinting is more focused on spotting unauthorized distribution across various platforms [6].
Watermarks are designed to withstand light edits, but aggressive transformations – like heavy cropping or reformatting – can sometimes remove them. Fingerprinting, however, remains resilient against structural changes such as cropping, color adjustments, or format conversions [6]. That said, fingerprinting can occasionally result in false positives when two entirely different files share similar structural features [3]. These differences in how the two methods handle modification, timing, purpose, and durability are outlined in the table below.
Comparison Table: Fingerprinting vs. Watermarking
| Aspect | Digital Watermarking | Digital Fingerprinting |
|---|---|---|
| Content Modification | Modifies the file (adds a signal/pattern) | No modification (extracts a signature) |
| Timing | Applied at creation or distribution | Applied post-creation (enrollment) |
| Primary Goal | Provenance, ownership, and leak tracing | Detection of duplicates and copyright enforcement |
| Question Answered | "Who leaked it?" | "Where is my content showing up?" |
| Robustness | Can be scrubbed by heavy editing/screenshotting | Robust against cropping, compression, and filters |
| Requirement | Requires generator/platform cooperation | Requires a database of "master" signatures |
| Precision | High (can identify specific users/sessions) | High (can identify "near-duplicates") |
| Cost/Complexity | Low to moderate (integrated into workflow) | High (requires database maintenance and scanning) |
| Retroactive Protection | Cannot protect pre-watermarked copies | Can identify content already "in the wild" |
| Use Case Example | Tracing a leaked movie screener to a specific critic | YouTube Content ID identifying a song in a video |
Benefits and Use Cases for Each Technology
Benefits of Fingerprinting
Fingerprinting identifies unauthorized content after distribution by analyzing its inherent features and creating a unique signature – all without altering the file. This approach is crucial in scenarios where file integrity must remain untouched, such as legal evidence or archival content.
One standout feature of fingerprinting is its resilience. Even after significant edits like cropping, compression, or applying filters, the technology can still recognize content by examining its deeper structural patterns.
"Fingerprinting is what you rely on when content gets out and there’s no watermark to trace."
- FastPix [6]
Advanced systems can even detect collusion, identifying content when multiple altered versions are combined [7]. This makes fingerprinting especially effective for protecting high-value assets like live sports broadcasts or premium media. It also enables piracy tracing, arming content owners with technical proof to take legal action. This proof ensures that violators can’t deny responsibility by claiming someone else created the redistributed copy [7].
While fingerprinting excels at detecting unauthorized content, watermarking offers direct traceability and user-specific accountability.
Benefits of Watermarking
Watermarking embeds unique identifiers – like user IDs or session timestamps – into each distributed copy, making it possible to trace leaks back to the exact individual or session responsible. This is particularly useful for pre-release materials, such as films or corporate videos, where identifying the source of a leak is critical.
The technology also provides strong legal backing for copyright claims , often bolstered by how blockchain enhances digital watermarking by linking infringing copies to their specific distribution points. This is especially relevant since insiders and authorized users are responsible for nearly one in three video leaks [6]. Streaming giants like Netflix, Disney+, and Amazon Prime Video rely on invisible forensic watermarking to hold individuals accountable and prevent leaks throughout the distribution process [6].
"Watermarking helps you prove who had access. Fingerprinting tells you where the content is now."
- Sourabh Gururaj Deshpande, Software Engineer, FastPix [6]
Visible watermarks, on the other hand, serve as a deterrent for casual piracy while doubling as branding tools for stock photo previews and content reviews.
When to Use Fingerprinting vs. Watermarking
Fingerprinting and watermarking shine in different scenarios. Fingerprinting is ideal for monitoring web-distributed, modified content at scale, while watermarking is the go-to solution for high-value, pre-release material where tracing leaks to specific individuals is crucial.
Fingerprinting is particularly effective for platforms with user-generated content, as it can automatically flag and block copyrighted material uploaded by users. It’s also the right choice for scanning social media, piracy websites, and torrent networks for unauthorized copies of content that may have been heavily edited.
Watermarking, on the other hand, is indispensable for pre-release film screeners, internal corporate videos, and premium streaming content. For instance, organizations like the NBA and FIFA use watermarking during live broadcasts to trace the source of leaked feeds. They often pair it with fingerprinting to locate and remove clips reposted on social media in real time [6].
For large-scale asset management, tools like InCyan’s Tectus and Idem combine the strengths of both technologies. Tectus provides invisible watermarking for images, videos, and audio, while Idem offers fingerprinting capable of detecting content ownership even when only 10% of the original asset remains. Together, these tools create a robust security system that deters unauthorized use and ensures rapid detection.
Using Fingerprinting and Watermarking Together
Hybrid Approaches in Digital Protection
Fingerprinting and watermarking work hand in hand to safeguard digital content effectively [6]. Together, they tackle two major challenges: detection and attribution. Watermarking embeds unique identifiers into each distributed file, making it possible to trace leaks back to specific users or sessions. Meanwhile, fingerprinting scans the web for content, even when it has been heavily edited or altered to remove watermarks. This combination ensures a more comprehensive protection strategy for digital assets.
This dual approach is especially effective against watermark stripping. Pirates often rely on AI tools to erase watermarks [6]. When that happens, fingerprinting comes into play by analyzing intrinsic structural patterns – like motion vectors in videos or audio waveforms – that remain intact despite modifications.
"Watermarking helps you prove who had access. Fingerprinting tells you where the content is now."
- FastPix [6]
Major streaming platforms rely on this combination to protect their content. Forensic watermarking traces leaks of pre-release material, while fingerprinting identifies unauthorized clips online [6]. Together, they provide stronger legal evidence: watermarks establish ownership and pinpoint contract violations, while fingerprinting demonstrates the extent and location of unauthorized distribution [6].
InCyan‘s Solutions for Fingerprinting and Watermarking
InCyan has developed a suite of tools that integrates watermarking, fingerprinting, and blockchain-based verification into one cohesive protection strategy. Their Tectus tool embeds invisible watermarks that withstand re-encoding and compression, while Idem uses fingerprinting to detect ownership even if only 10% of the original content remains. This makes it effective against alterations like mobile edits, cropping, memes, and other transformations.
These tools address key vulnerabilities in digital content security. Tectus embeds forensic marks to trace leaks back to their source, solving the attribution issue. Idem, on the other hand, scans multimodal databases to locate unauthorized copies, even heavily modified ones, tackling the detection problem when watermarks are stripped. For organizations managing large content libraries, Blueprint integrates these tools into a digital asset management platform, streamlining both storage and security.
To further enhance protection, ScoreDetect adds blockchain-based timestamping. While Tectus and Idem handle watermarking and fingerprinting, ScoreDetect creates a permanent, verifiable record of ownership by recording a checksum of your content on the blockchain – without storing the actual files. This is particularly useful for copyright claims and counterclaims, as it establishes proof of creation and authorship. ScoreDetect also integrates with over 6,000 web apps via Zapier and includes a WordPress plugin that automatically timestamps published or updated content, boosting copyright protection and improving SEO by aligning with Google’s E-E-A-T signals.
For large-scale enforcement, InCyan offers Indago, which removes unauthorized content from search engines in under 60 minutes [6]. Additionally, TorrentWatch monitors peer-to-peer networks like BitTorrent for copyright violations, providing real-time enforcement data to protect your assets across multiple platforms.
Conclusion
Key Takeaways
Digital fingerprinting and watermarking work hand-in-hand to protect content, each serving a distinct purpose. Fingerprinting analyzes and identifies unique elements of a file – like audio waveforms or video motion patterns – without altering the original. This makes it perfect for spotting unauthorized usage. On the other hand, watermarking embeds identifiable data directly into the file, either visibly or invisibly, to establish ownership and track leaks to specific users or sessions.
When used together, these technologies offer robust protection. Streaming giants like Netflix, Disney+, and Amazon Prime Video rely on invisible watermarking to trace pre-release leaks while leveraging advanced fingerprinting to locate unauthorized content online. This combination is especially effective since nearly 1 in 3 video leaks come from authorized users [6]. By pairing these tools, you can detect and trace leaks back to their source, helping to protect your content more effectively.
Recommendations
Start by assessing your primary risk. If proving ownership or tracing leaks from authorized users is your priority, invisible watermarking is your go-to solution. It allows you to embed unique session identifiers directly into files. On the other hand, for automated monitoring of platforms like social media or user-generated content sites, fingerprinting is invaluable. It can detect unauthorized copies even after modifications like cropping or compression. YouTube’s Content ID system, for example, uses fingerprinting to identify copyrighted material in user uploads at scale.
For high-value assets such as pre-release films or live sports, combining session-based watermarking with fingerprinting is essential. This dual approach allows for rapid identification and removal of leaks. Tools like InCyan’s Tectus and Idem work together to embed invisible marks and recognize content even from small fragments, while their Blueprint platform integrates these capabilities into a single digital asset management system. Additionally, ScoreDetect leverages blockchain-based timestamping to create permanent proof of ownership without storing the actual files.
To ensure legal enforcement, establish a clear chain of custody. Use immutable logs and cryptographic hashes to verify when your content was created and distributed. Tools like InCyan’s Indago can quickly remove unauthorized content from search engines, while TorrentWatch monitors peer-to-peer networks for real-time enforcement. The ideal strategy includes a feedback loop: fingerprinting identifies where your content appears, watermarking confirms the source of the leak, and blockchain timestamping verifies the creation date. Together, these steps form a comprehensive content protection plan.
FAQs
Can fingerprinting match my content if only a short clip is used?
Yes, fingerprinting can identify your content even if only a short clip is used. Its accuracy depends on how advanced the fingerprinting technology is. These systems analyze the unique "digital DNA" of a file, allowing them to recognize even small fragments of content. More advanced methods can detect content from minimal portions, while simpler systems might need a larger piece for reliable results. This capability makes fingerprinting especially helpful for organizing and managing extensive content libraries.
How do invisible watermarks identify the exact person who leaked a file?
Invisible watermarks embed hidden, unique information into digital content, connecting it to a specific user or device. If the content is leaked, forensic tools can extract this embedded data to identify the source. Unlike fingerprinting, which examines content characteristics, invisible watermarking acts as a direct marker. It stays detectable even after edits, allowing accurate tracking of the leaker.
Do I need both fingerprinting and watermarking, or just one?
Whether you need fingerprinting, watermarking, or both depends on what you’re trying to achieve.
Watermarking involves embedding visible or invisible marks into a file. These marks help assert ownership and trace any leaks back to the source. On the other hand, fingerprinting works differently – it identifies copies by analyzing a file’s unique characteristics without modifying it.
If you’re looking for comprehensive protection, combining both methods might be the way to go. Watermarking can embed traceable identifiers, while fingerprinting helps detect unauthorized use. However, if your needs are more specific, you may find that focusing on just one of these methods is enough, depending on your priorities.