Piracy on peer-to-peer (P2P) networks is a growing issue, costing industries billions annually and threatening creative jobs. Combatting this requires advanced tools that can detect and remove infringing content quickly, even when altered or hidden. Here are seven tools designed to monitor and enforce copyright protection across P2P platforms:
- TorrentWatch: Tracks BitTorrent activity in real-time, identifying violations and automating enforcement actions.
- Idem: Detects altered digital assets with multimodal matching, even if heavily modified.
- Tectus: Embeds invisible watermarks for tracing ownership across P2P networks.
- ScoreDetect: Uses blockchain to verify content ownership instantly, providing legal proof.
- Indago: Removes search engine links to infringing content within an hour.
- BlockWatch: Monitors ISP-blocked sites to identify gaps in enforcement.
- Txtmatch: Protects text-based content like eBooks by scanning P2P platforms for matches.
These tools combine AI-driven detection, automation, and integration capabilities to provide a layered defense against piracy. Together, they can reduce illegal sharing by up to 85% in the first month of use.
P2P File-Sharing & Copyright Infringement :: Part 1
sbb-itb-738ac1e
1. TorrentWatch
TorrentWatch is InCyan’s platform designed to monitor and detect copyright infringement across the BitTorrent ecosystem. It provides rights holders with real-time data to act quickly, thanks to its continuous scanning of torrent sites and P2P networks for illegal content sharing [5].
P2P Monitoring Features
Using peer swarm analysis, TorrentWatch tracks active groups sharing files. This allows it to measure the scale of infringement and pinpoint specific IP addresses through constant, real-time monitoring [5].
Fast Detection
With AI-powered agents working 24/7, TorrentWatch uses perceptual fingerprinting technology to identify copyrighted content, even if it has been altered – whether re-encoded, compressed, or modified in other ways. This ensures timely updates on unauthorized content distribution [5].
Fully Automated Enforcement
TorrentWatch takes automation to the next level. Once metadata is uploaded through its simple onboarding process, it becomes part of the piracy detection network, triggering instant alerts for any violations. The system also includes pre-built DMCA enforcement templates and automated legal tools, reducing the need for time-consuming manual work in protecting copyrights [5]. Up next, learn about Idem’s advanced asset matching technology.
2. Idem
Idem is InCyan’s multimodal matching platform designed to identify digital assets across P2P networks, even when those assets have been heavily altered. Unlike basic fingerprinting tools, Idem can withstand transformations like cropping, compression, and mobile edits, still detecting ownership even if only 10% of the original content remains.
P2P Surveillance Capabilities
Idem’s strength in surveillance comes from its multi-feature perceptual hashing framework, which relies on techniques like MFCCs, chroma-based features, and spectral analysis. These methods allow it to capture harmonic and temporal patterns with precision. This makes it highly effective on P2P networks, where files are often re-encoded or modified to bypass traditional monitoring systems.
Detection Speed
To ensure both speed and accuracy, Idem employs Dynamic Time Warping (DTW), which aligns feature frames between the original and altered versions of content. This allows it to handle non-uniform edits seamlessly. The platform operates continuously, scanning torrent networks, BitTorrent trackers, magnet link indexes, and seedboxes around the clock.
Integration Options
Idem can integrate with CMS and rights management systems through its API, enabling automated DMCA takedowns and streamlining licensing and royalty workflows. Up next, explore how Tectus delivers invisible proof of ownership through advanced watermarking.
3. Tectus
Tectus, part of InCyan’s lineup, offers a cutting-edge approach to content protection through invisible watermarking. This blind watermarking solution embeds an undetectable proof of ownership directly into digital files. Unlike traditional visible watermarks that can interfere with the user experience, Tectus creates a unique digital marker that remains intact even after file modifications like resizing or re-encoding. This makes it a powerful tool for tracking content, particularly across P2P networks where files are often altered to bypass detection [4].
P2P Surveillance Capabilities
Tectus employs perceptual fingerprinting to generate spectral embeddings, essentially capturing the unique "DNA" of digital content. This advanced technology resists common tactics used by P2P distributors, such as compression, format conversion, and watermark removal [2]. The embedded watermark stays intact even when files are shared on P2P platforms, enabling rights holders to trace unauthorized distribution back to its origin.
Integration Options
The Tectus API integrates effortlessly with content and rights management systems, automating processes like DMCA takedowns [4]. Beyond that, it syncs with existing licensing and royalty collection systems, creating a streamlined and unified ecosystem for enforcement [5].
Next, take a look at ScoreDetect’s blockchain timestamping for an additional layer of content protection.
4. ScoreDetect

ScoreDetect uses blockchain-based verification to protect digital assets, offering an unchangeable record of ownership. Built by InCyan, it ensures a transparent and globally verifiable authorship record that can even stand up in legal cases when unauthorized content appears on peer-to-peer (P2P) networks.
Detection Speed
With an average transaction speed of 3.139 seconds [7], ScoreDetect allows creators to establish proof of ownership almost instantly. Compare that to traditional copyright registration services, which can take days or even weeks. This quick timestamping provides immediate, defensible evidence of ownership when your content is discovered on P2P networks. The speed and automation of this process are critical for combating the rapid spread of unauthorized content, giving creators a powerful tool for protecting their work.
Automation Level
ScoreDetect connects with over 6,000 web applications through Zapier, making it easy to integrate into existing workflows. For WordPress users, its plugin automatically timestamps every article update, creating verifiable proof of ownership without the need for manual effort. This automation not only secures your content but also boosts your site’s SEO by improving Google’s E-E-A-T (Experience, Expertise, Authoritativeness, and Trustworthiness) metrics.
"ScoreDetect is exactly what you need to protect your IP in this age of hyper-digitization. Truly an innovative product, I highly recommend it!" – Imri, CEO, Startup SaaS [7]
These features make it simple to integrate ScoreDetect into various platforms.
Integration Options
ScoreDetect supports integration across Windows, macOS, and Linux systems, with API access for custom workflows tailored to enterprise needs. Importantly, it ensures seamless integration without exposing your original assets, maintaining the security and privacy of your digital content.
5. Indago
Indago is a search enforcement platform created by InCyan to protect your digital content by tackling piracy right at its source. When your assets show up on P2P networks, Indago uses an AI-powered scanner to track torrent activity and swiftly remove unauthorized listings from search engines, effectively blocking illegal downloads.
P2P Monitoring Features
Indago uses AI file fingerprinting to recognize your content, even if it’s been altered. Its Smart Detection Engine, powered by machine learning, identifies new piracy threats early on. The platform also incorporates geo and IP tracking, giving rights holders the tools to trace piracy back to its origins and take precise action.
Rapid Detection and Response
Speed is a key focus for Indago. It quickly de-indexes unauthorized links, minimizing the time frame during which illegal downloads can occur. This fast action helps limit piracy’s impact on your content.
Fully Automated Process
Indago operates with full automation, scanning torrent sites and P2P networks 24/7. When it detects unauthorized activity, the system instantly generates DMCA-compliant notices and submits takedown requests. Once you upload your content metadata, Indago integrates it into its detection network, managing everything from discovery to delisting. Up next, check out BlockWatch for keeping tabs on ISP blocks.
6. BlockWatch

BlockWatch is a monitoring platform designed by InCyan to track ISP-blocked sites, helping rights holders pinpoint when and where their content is being restricted. Unlike tools that focus on identifying pirated files, BlockWatch specializes in verifying ISP blocks across different regions, highlighting areas where unauthorized content might still be accessible. It works as part of InCyan’s anti-piracy toolkit, focusing on discrepancies in ISP blocking to complement other monitoring tools. By integrating with InCyan’s broader P2P monitoring efforts, BlockWatch provides detailed insights through its advanced detection methods.
P2P Surveillance Capabilities
BlockWatch employs a global proxy system, using proxy pools across 188 countries to scan the web from various locations simultaneously. This setup allows it to bypass local ISP restrictions, geo-blocks, and other filters that often hide piracy. For instance, if a torrent site is blocked in the United States but remains available in other regions, BlockWatch identifies this gap, offering rights holders a clearer understanding of where their content is still at risk [1][6]. This comprehensive surveillance system ensures quick and accurate detection.
Detection Speed
The platform constantly monitors blocked sites to differentiate between legitimate ISP blocks and simple site outages. This real-time tracking allows rights holders to identify enforcement gaps without delay.
Automation Level
BlockWatch operates around the clock, with AI agents monitoring torrent sites, magnet indexes, and seedboxes. These agents automatically flag changes in accessibility, enabling immediate enforcement actions when necessary [5][2].
7. Txtmatch
Txtmatch is InCyan’s advanced tool for protecting written content – like e-books and academic papers – from being shared without permission on P2P networks. Using a specialized database built from an extensive collection of online publications, it identifies plagiarism with impressive accuracy.
P2P Surveillance Capabilities
Txtmatch keeps a close watch on P2P platforms, including torrent networks and cyberlockers. It compares files against its secure database to spot even subtle changes in text. This makes it an essential tool for publishers and academic institutions preventing plagiarism in academic writing and safeguarding their work.
Detection Speed
With the ability to process over 600 frames per second under optimal conditions, Txtmatch scans large volumes of data in real time across P2P networks [8].
Automation Level
Txtmatch operates 24/7, continuously monitoring torrent sites and file-sharing platforms. When it identifies a potential match, it automatically issues DMCA notices and takedown requests. This automation not only simplifies enforcement but also reduces the need for manual intervention. Plus, Txtmatch integrates effortlessly into existing workflows, enhancing InCyan’s already comprehensive P2P monitoring tools.
Feature Comparison
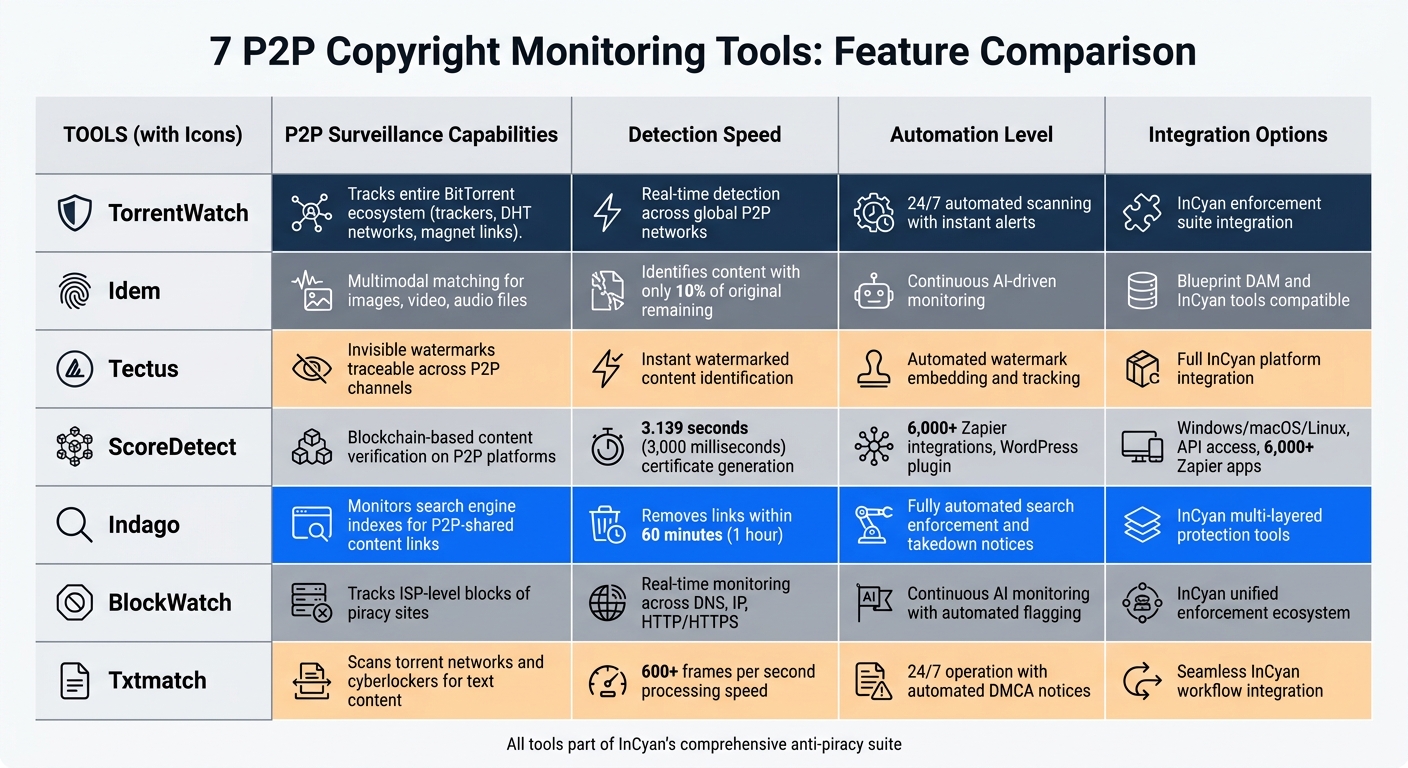
P2P Copyright Monitoring Tools Feature Comparison Chart
The table below highlights the core capabilities of each InCyan tool, showcasing how they tackle piracy challenges from different angles.
| Tool | P2P Surveillance Capabilities | Detection Speed | Automation Level | Integration Options |
|---|---|---|---|---|
| TorrentWatch | Tracks the entire BitTorrent ecosystem, including trackers, DHT networks, and magnet links | Real-time detection across global P2P networks | 24/7 automated scanning with instant alerts | Works seamlessly with InCyan’s enforcement suite |
| Idem | Matches shared images, video, and audio files using multimodal methods | Identifies modified content even if only 10% of the original remains | Continuous AI-driven monitoring | Compatible with Blueprint DAM and other InCyan tools |
| Tectus | Embeds invisible watermarks traceable across P2P channels | Instantly identifies watermarked content | Automates watermark embedding and tracking | Integrates with InCyan’s full protection platform |
| ScoreDetect | Verifies content on P2P platforms using blockchain technology | Takes approximately 3,000 milliseconds to generate a certificate | Streamlines workflows through 6,000+ Zapier integrations | Offers a WordPress plugin, developer API, and custom integration options |
| Indago | Monitors search engine indexes for links to P2P-shared content | Removes unauthorized links within 60 minutes | Fully automates search enforcement and takedown notices | Connects with InCyan’s multi-layered protection tools |
| BlockWatch | Tracks ISP-level blocks of piracy sites | Detects across DNS, IP, and HTTP/HTTPS protocols | Continuously monitors and provides detailed block reports | Part of InCyan’s unified enforcement ecosystem |
| Txtmatch | Scans torrent networks and cyberlockers for text-based content | Delivers rapid text matching with forensic precision | Operates 24/7 with automated monitoring | Easily integrates into existing InCyan workflows |
Each tool brings a distinct strength to the table. TorrentWatch excels in real-time P2P alerts, while Indago ensures unauthorized links are addressed swiftly – often within an hour. ScoreDetect stands out for its blockchain-based content verification and extensive integration options, including over 6,000 Zapier connections and a WordPress plugin. Meanwhile, tools like Tectus and Idem focus on specialized tasks like watermark tracking and multimodal content matching. Together, these tools create a layered defense system, reinforcing InCyan’s commitment to protecting digital content with precision and efficiency.
Conclusion
Piracy remains a massive challenge for the film and TV industry, costing an estimated $30 billion annually. Alarmingly, about 76% of infringing content resurfaces within just 48 hours of being removed [5]. Addressing this issue requires advanced tools capable of real-time detection and swift enforcement.
Modern tools offer AI-driven detection, automated workflows, and real-time enforcement that manual methods simply can’t match. For example, platforms using perceptual fingerprinting can identify your content – even if it’s renamed, re-encoded, or altered – with an impressive accuracy rate of 99.2% [2]. Beyond torrents, these tools monitor cyberlockers, Telegram channels, Discord servers, and even dark web platforms where pirated content often originates.
Selecting the right tool depends on your specific needs:
- TorrentWatch: Ideal for real-time BitTorrent surveillance across the ecosystem.
- Idem: Excels at multimodal content matching, even identifying assets with only 10% of the original intact.
- Tectus: Embeds invisible watermarks for traceable ownership.
- ScoreDetect: Offers blockchain-certified file ownership and integrates with over 6,000 Zapier workflows.
- Indago: Removes unauthorized search engine links in under an hour.
- BlockWatch: Tracks ISP-level blocks across multiple technical layers.
- Txtmatch: Delivers forensic-level text matching at enterprise scale.
InCyan’s suite of tools provides a multi-layered defense against piracy. When used together, they tackle various piracy avenues – from content leaks to search engine visibility to torrent activity. This combined approach can reduce torrent-based piracy by up to 85% within the first month of deployment [3].
Speed is crucial in combating piracy. Prolonged exposure of infringing content leads to greater revenue losses, so tools with automated DMCA notices, real-time alerts, and takedown speeds under four hours are essential [2]. In a world where piracy evolves rapidly, your content protection strategy must operate just as fast.
FAQs
Which tool should I start with for my type of content?
For keeping your content safe and under control, it’s smart to use a tool that covers detection, monitoring, and enforcement seamlessly. EzlaScan is a solid pick, offering nonstop scanning across platforms, torrent networks, and streaming services, plus automated takedowns to handle infringements. Another option is Rightscan, which focuses on copyright enforcement driven by data insights. If you’re tackling large-scale web monitoring, Oxylabs provides customized solutions for web scraping and spotting infringements.
How do these tools still find my content after it’s been modified?
These tools rely on advanced AI technologies, including fingerprinting and multimodal matching, to identify your content even after it’s been altered. For instance, they can spot changes like cropping, compression, or other edits by comparing unique digital fingerprints or checksums securely stored – sometimes even on a blockchain. Some tools also use methods like watermarking or forensic analysis to trace your original work, ensuring it can still be recognized despite modifications.
What evidence can I use if I need to take legal action?
When dealing with copyright infringement, documented evidence can be a game-changer. Tools like digital monitoring reports, automated takedown notices, and forensic analysis of infringing content serve as powerful resources. These materials not only help identify violations but also provide solid backing for legal action when necessary.

