Invisible watermarking is a method of embedding hidden, machine-readable signals into digital media – like images, videos, or audio – without altering their appearance or quality. Unlike visible watermarks or metadata, which can be removed or stripped during edits or uploads, invisible watermarks stay embedded in the file’s structure, making them ideal for tracking ownership and deterring misuse.
Here’s why invisible watermarking is effective:
- Durability: Survives edits like cropping, compression, and color adjustments.
- Invisibility: Preserves the content’s quality without noticeable changes.
- Tracking Ownership: Links media to its creator, even after transformations.
- Legal Proof: Provides evidence of ownership through cryptographic logs.
Invisible watermarking uses two main techniques:
- Spatial Domain: Alters raw data (e.g., pixels) but is less resilient to edits.
- Transform Domain: Embeds data in frequency components, making it harder to remove.
Tools like InCyan’s Tectus and ScoreDetect integrate watermarking with blockchain-based timestamps, ensuring tamper-proof ownership records. By embedding watermarks and pairing them with automated detection systems, creators can protect their work, detect misuse, and enforce rights effectively.
Invisible Watermarking: Content Provenance for Videos at Scale | Wes Castro, Meta
sbb-itb-738ac1e
How Invisible Watermarking Works
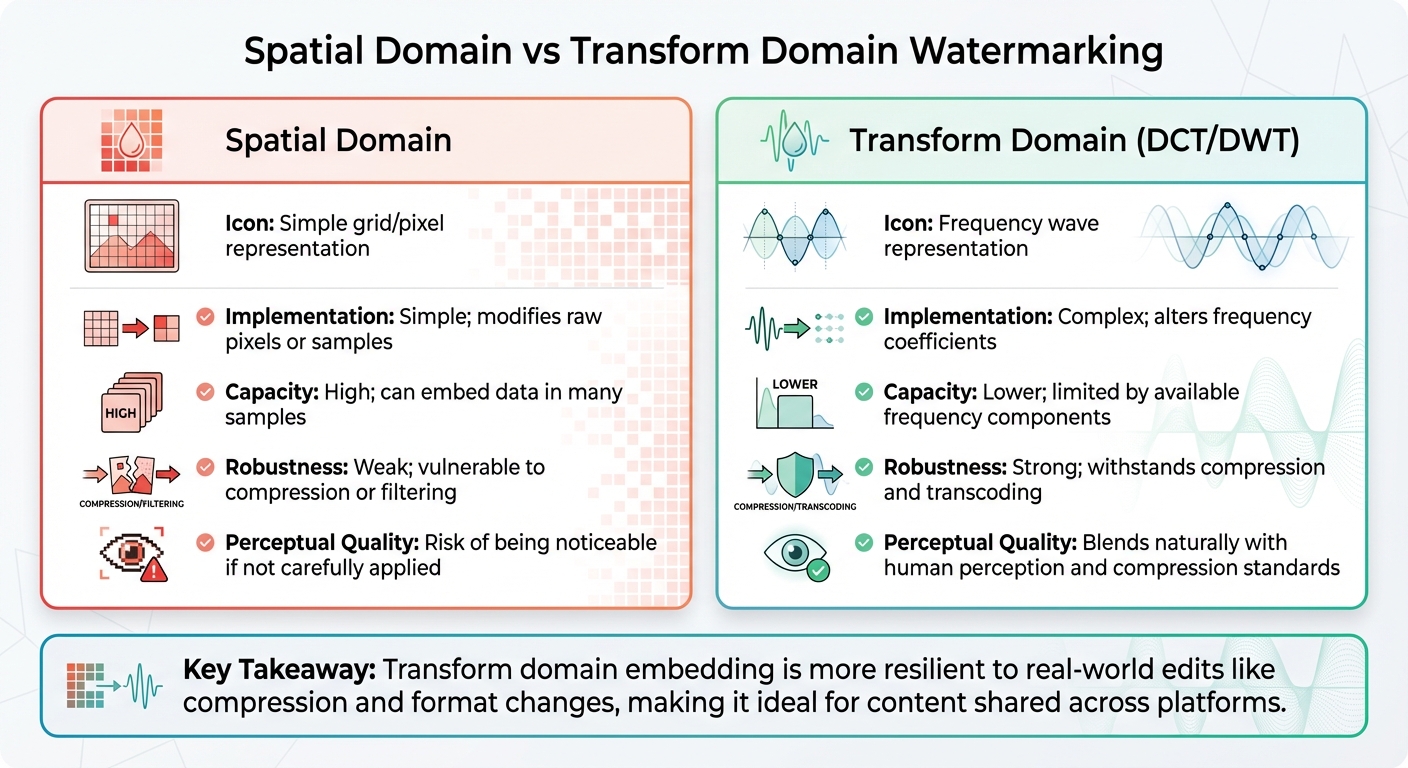
Spatial vs Transform Domain Watermarking: Key Differences
Invisible watermarking weaves data into the very fabric of a digital file – whether it’s an image, audio track, or video. This process subtly alters the file in ways that are undetectable to the human eye or ear but can be picked up by specialized tools. The key to success lies in balancing three factors: how much data the watermark can hold, its ability to survive edits, and its invisibility to users.
Methods for Embedding Watermarks
Invisible watermarks are typically embedded using one of two main techniques, each with its own strengths and weaknesses.
Spatial domain embedding modifies the raw data of a file, such as pixel values in images or audio sample values. A common method involves tweaking the least significant bits (LSBs) of these values. While this approach can store a lot of information, it’s not very durable. Simple edits like JPEG compression or audio filtering can easily damage or erase the watermark.
Transform domain embedding takes a more sophisticated route by embedding data into the frequency components of a file. Techniques like the Discrete Cosine Transform (DCT) or Discrete Wavelet Transform (DWT) are often used. This method aligns with how modern compression formats like JPEG or H.264 work, making the watermark much harder to remove. Even when a file is compressed or transcoded, the watermark remains intact because it’s embedded in the same frequency layers that compression algorithms utilize.
Some systems combine these methods. By embedding a durable but small watermark in the transform domain and a larger, more fragile one in the spatial domain, they strike a balance: the robust watermark survives heavy editing, while the fragile one provides more detailed information when intact.
| Feature | Spatial Domain | Transform Domain (DCT/DWT) |
|---|---|---|
| Implementation | Simple; modifies raw pixels or samples. | Complex; alters frequency coefficients. |
| Capacity | High; can embed data in many samples. | Lower; limited by available frequency components. |
| Robustness | Weak; vulnerable to compression or filtering. | Strong; withstands compression and transcoding. |
| Perceptual Quality | Risk of being noticeable if not carefully applied. | Blends naturally with human perception and compression standards. |
Maintaining Invisibility
Ensuring watermarks remain hidden requires a deep understanding of human perception. This is where perceptual modeling comes into play. By studying how humans process visual and audio information, developers can place watermarks in areas where they’re least likely to be noticed. For example:
- In images, watermarks are often hidden in textured areas like foliage or fabric, where the complexity masks any slight changes. Flat areas, like clear skies, are avoided as changes are more noticeable there.
- In audio, techniques like psychoacoustic masking hide watermarks beneath louder or more complex sounds, ensuring they remain imperceptible.
Metrics like PSNR (Peak Signal-to-Noise Ratio) and SSIM (Structural Similarity Index) help verify that the watermarked content remains visually and structurally close to the original. For video, watermarks must also align with the file’s temporal structure, such as synchronizing with Groups of Pictures (GOPs), to avoid visible artifacts during playback.
"The goal is not to hide a watermark completely from dedicated forensic analysis such as forensic audio watermarking, but to ensure that the audience experiences the content as intended." – Nikhil John, InCyan [1]
This delicate balancing act is often referred to as the "Watermarking Triangle" – a trade-off between invisibility, robustness, and capacity. Most watermarks hold only a small amount of data, typically measured in bits rather than large text blocks. Adjusting one factor often means compromising another, so the choice of watermarking method depends on your specific needs and how your content will be distributed.
What Makes Invisible Watermarking Effective
Invisible watermarking works best when it maintains the quality of the content while enduring various real-world changes. Its success hinges on two key factors: preserving the original quality and surviving modifications.
Preserving Content Quality
If a watermark compromises the quality of the content, it can do more harm than good. Visible issues like artifacts, banding, or distortion can make the watermark a liability instead of a safeguard. That’s why invisibility is a cornerstone of effective watermarking.
Metrics like PSNR (Peak Signal-to-Noise Ratio) and SSIM (Structural Similarity Index) are used to ensure watermarked content remains almost identical to the original. Additionally, blind tests with diverse audiences confirm that the watermark does not affect how the content is perceived – whether it’s a high-res photograph, a streaming video, or professional-grade audio.
But quality isn’t the only factor. A watermark also needs to stand up to inevitable changes in the content.
Surviving Content Modifications
A watermark loses its purpose if it can’t withstand real-world changes. The ability to endure transformations – known as robustness – is key. As Nikhil John explains:
"A watermark that disappears after a single round of social media transcoding or minor color correction does not help rights holders."
Effective watermarks are designed to handle a variety of changes, from unintentional processing like transcoding to deliberate edits such as cropping, filtering, or color grading. Techniques like transform domain embedding ensure the watermark remains intact through format shifts. Additionally, redundancy and energy spreading distribute the watermark across the content, so even if parts are altered or removed, enough remains to detect ownership, often utilizing deep learning for watermark detection.
This resilience is especially critical when platforms strip metadata or when individuals attempt to erase ownership signals. Unlike metadata, which can vanish with a simple re-export, or visible watermarks that can be cropped out, an invisible watermark stays embedded. As Nikhil John points out:
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state."
Protecting Content Ownership and Preventing Piracy
Invisible watermarks that survive alterations become a game-changer for safeguarding ownership and tackling piracy. Their resilience allows creators to prove ownership and track misuse across the web, forming the backbone of automated detection systems.
Finding Misused Content
Detecting piracy on a large scale demands automation. Blind watermarking makes it possible to scan billions of assets across social media, peer-to-peer networks, and other platforms without needing the original, unmarked file for comparison. This is particularly useful in scenarios where storing and managing source files for every scan isn’t feasible.
Here’s how it works: suspect assets are ingested, the watermark is extracted, and the system matches it to a rights database, generating a confidence score. This streamlined process enables organizations to quickly pinpoint unauthorized uses. A standout example is InCyan’s Idem platform, which leverages AI-powered multimodal matching to detect ownership, even if only 10% of the original content remains. It can withstand edits like cropping, compression, memes, or mobile modifications, which often defeat traditional detection methods.
Establishing Legal Proof of Ownership
Detecting misuse is just the first step – proving ownership in legal settings is equally critical. For invisible watermarks to hold up in court, they must come with an unbroken chain of custody. This involves immutable logs, cryptographic hashes, and audit trails to demonstrate that the watermarking process hasn’t been tampered with.
Watermark payloads are compact but powerful, carrying tens to hundreds of bits. They encode information like unique identifiers, version details, and cryptographic data that link the content to verified ownership records. International copyright laws recognize watermarking as a legitimate tool for rights protection, making it a reliable method for establishing ownership. To further bolster their case, organizations can use blockchain-based ledgers to store time-stamped records of detection events, ensuring tamper-proof documentation for legal proceedings.
Applying Invisible Watermarking with InCyan Solutions
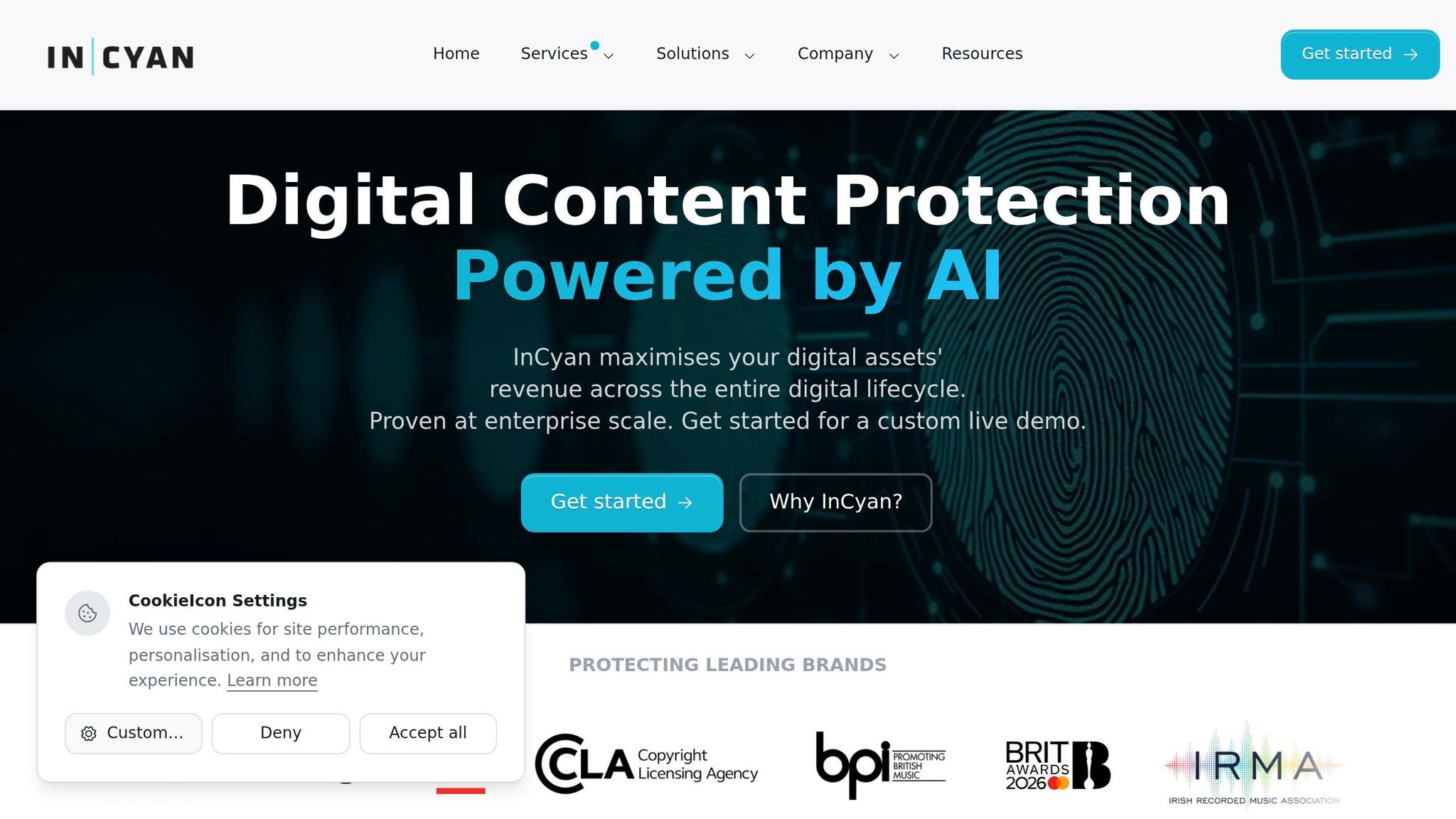
InCyan offers two powerful tools for safeguarding digital assets: Tectus, designed for enterprise-grade invisible watermarking of images, video, and audio, and ScoreDetect, which uses blockchain timestamps to provide verifiable proof of ownership. Together, these tools create a robust system that embeds ownership signals while maintaining tamper-proof records.
How to Embed Invisible Watermarks
Tectus is built around a balance of three key elements: imperceptibility, robustness, and capacity. This balance ensures that watermarks remain invisible to viewers, survive edits and compression, and carry important metadata like unique identifiers or version information.
The system uses perceptual modeling to embed watermarks in areas where human perception is less sensitive, preserving the original viewing experience while keeping ownership signals intact. It employs blind watermarking, meaning the embedded data can be verified without needing the original file – a critical feature for large-scale platforms that can’t store master files for every asset.
Tectus embeds watermarks in the transform domain, modifying coefficients like DCT or DWT instead of altering the spatial domain. This makes the watermarks more resilient to lossy compression and format changes, which are common when content is shared on social media or streaming platforms.
For organizations managing massive libraries of assets, efficiency is key. The embedding process must integrate seamlessly into existing transcoding workflows without causing delays. Before deployment, it’s crucial to understand how your content might be altered – whether through social media compression, broadcast standards, or AI-driven edits – and adjust the watermark’s strength accordingly.
Once watermarks are embedded, the next step is to incorporate them into a broader protection strategy.
Building a Complete Protection Workflow
Embedding watermarks is just the starting point. To maximize their effectiveness, they should be part of a layered workflow. InCyan’s protection system is based on four pillars: Prevention (watermark embedding), Discovery (tracking usage), Identification (fingerprinting content), and Insights (actionable reporting).
The process begins with embedding watermarks on high-value assets using Tectus. Then, ScoreDetect can timestamp the content on the blockchain, creating a cryptographic record of ownership without storing the actual files. For instance, ScoreDetect’s WordPress plugin automatically timestamps published or updated articles, creating an unalterable proof of ownership that strengthens legal claims.
When unauthorized content is detected, the verification process unfolds in four steps: ingest (capturing metadata and timestamps), extraction (recovering the embedded watermark), reference matching (comparing it to a database of rights), and decision scoring (determining the confidence level of ownership). InCyan’s Idem platform streamlines this process with AI-powered detection, capable of identifying ownership even if only 10% of the original content remains.
For large-scale enforcement, Indago can quickly remove unauthorized content from search engines, de-indexing links in under an hour to cut off piracy at its source. Maintaining an unbroken chain of custody with cryptographic hashes and immutable logs ensures that evidence is admissible in court. As Nikhil John explains:
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." [1]
To begin, organize a workshop with your product, legal, security, and operations teams to map out content workflows and identify the assets most at risk. Tailor your watermarking strategy to the types of transformations your content is likely to encounter. Finally, deploy API-based verification tools that enable partners or regulators to confirm ownership independently, without exposing proprietary methods. By combining robust watermarking with automated verification, you can effectively protect your content from piracy and misuse.
Conclusion
Invisible watermarking provides a solid way to guard against digital piracy by embedding ownership signals directly into your content. These signals are designed to survive common alterations like cropping, compression, and platform-specific changes. Unlike visible logos or metadata that can be easily removed, invisible watermarks act as a permanent marker. As Nikhil John from InCyan puts it:
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." [1]
The success of this method hinges on balancing three key factors: ensuring watermarks remain invisible to preserve content quality, making them durable enough to withstand alterations, and embedding sufficient data to prove ownership. InCyan’s Tectus achieves this balance through perceptual modeling and transform domain embedding, allowing watermarks to remain hidden while enduring challenges like social media compression, AI-driven edits, and file format conversions.
To strengthen protection, verification tools play a vital role. InCyan’s ScoreDetect complements Tectus by creating blockchain-based timestamps, which establish tamper-proof ownership records without the need to store the actual files. When paired with Idem for content identification and Indago for rapid takedown actions, the result is a comprehensive system that prevents misuse, detects unauthorized use, and enforces rights across all platforms.
With the growth of generative AI and synthetic media, invisible watermarking has shifted from being a helpful tool to an essential safeguard. Organizations managing high-value digital assets – whether in media, healthcare, or other industries – require solutions that can confirm authenticity and ownership. By adopting a layered approach that integrates prevention, detection, and enforcement, you can protect your content at scale while delivering the quality and experience your audience expects.
Take the time to analyze your content workflows and test watermarking solutions against the transformations they’ll face. With the right approach, invisible watermarking becomes a reliable, built-in safeguard for your digital assets.
FAQs
Can invisible watermarks survive social media compression?
Invisible watermarks are designed to endure social media compression. They are embedded within the frequency components of the media, making them resilient against compression and typical edits. This ensures their longevity and effectiveness.
How can an invisible watermark prove ownership in court?
To establish ownership in court, an invisible watermark must be embedded using a secure and tamper-resistant method. It should be both detectable and verifiable through specialized tools, creating a clear connection between the content and its rightful owner. This ensures the watermark can act as dependable evidence of ownership when required.
What should I watermark and when in my workflow?
You should add watermarks to your digital assets – whether they’re images, videos, audio files, or documents – when you want to claim ownership, confirm their authenticity, or track their distribution. Use invisible watermarks once your content is fully prepared for release. This approach ensures the watermark remains intact, even after edits, compression, or resizing, offering long-term protection and reducing the risk of misuse.