Want to protect your digital content no matter how it’s altered or shared? Cross-media watermarking ensures your ownership remains intact even after resizing, cropping, re-encoding, or format changes. From embedding in transform domains to leveraging AI, this guide covers five key strategies to safeguard your media assets effectively:
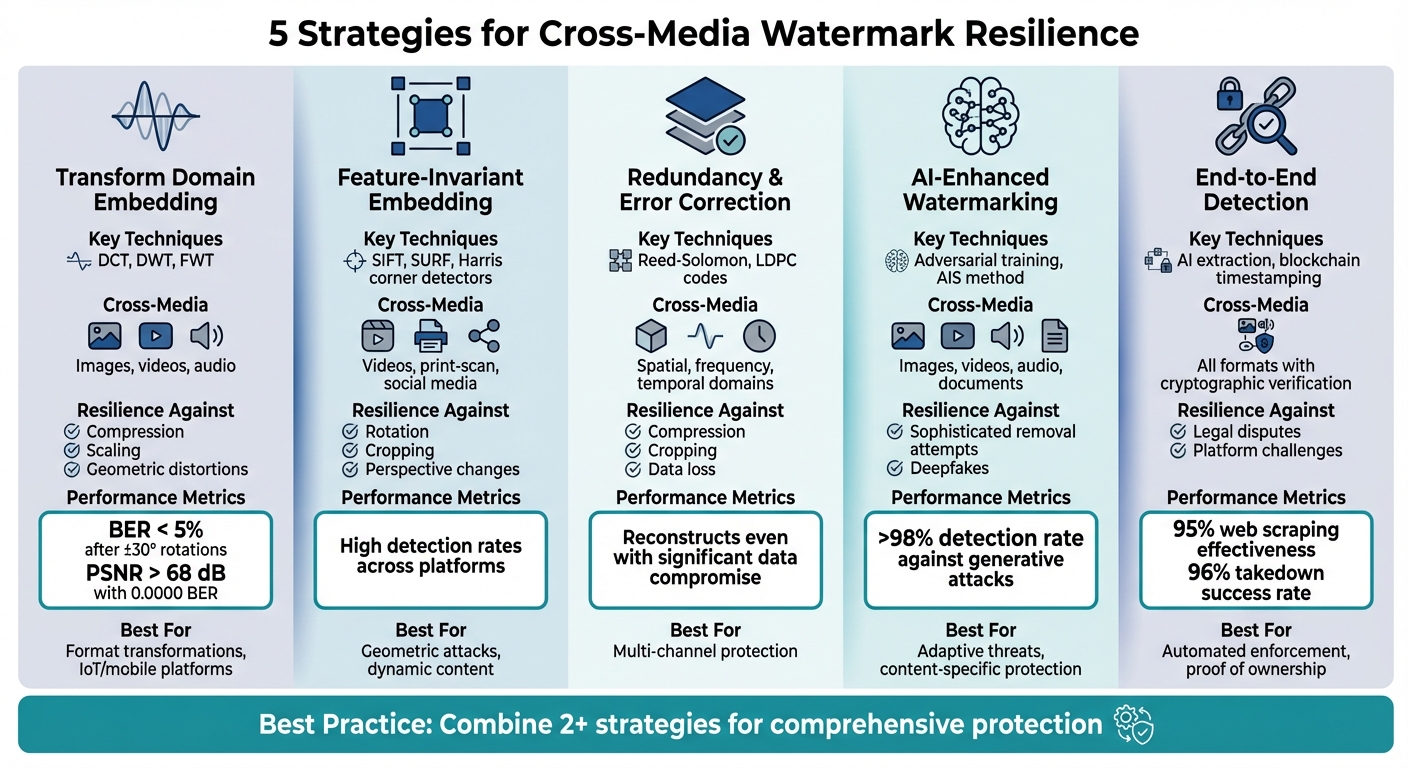
- Transform Domain Embedding: Uses frequency coefficients to ensure invisible watermarks resist removal during compression, scaling, and geometric distortions.
- Feature-Invariant Embedding: Anchors watermarks to stable visual features like edges or corners for resilience against rotation, cropping, and perspective changes.
- Redundancy and Error Correction: Embeds multiple watermarks across spatial, frequency, and temporal domains to ensure detection even after heavy alterations.
- AI-Enhanced Watermarking: Employs adversarial training to make watermarks resistant to sophisticated removal techniques.
- End-to-End Detection: Automates watermark detection and proof of ownership using blockchain for tamper-proof evidence.
5 Cross-Media Watermarking Strategies: Features and Benefits Comparison
DIP Lecture 21: Digital watermarking
sbb-itb-738ac1e
1. Transform Domain Embedding
Transform domain embedding is a key technique that ensures watermarks survive various types of media alterations.
Resilience to Format Transformations
Instead of modifying individual pixels, transform domain embedding works by altering frequency coefficients. Techniques like Discrete Cosine Transform (DCT), Discrete Wavelet Transform (DWT), and Fast Wavelet Transform (FWT) spread the watermark across the data structure. This makes it much harder to remove using standard editing methods [4][5].
Embedding watermarks in low-frequency sub-bands is particularly effective because these areas are preserved even during heavy compression, such as with JPEG algorithms. For practical use, embedding in low-frequency approximation sub-bands strikes a balance: it ensures resilience against lossy compression while keeping the watermark nearly invisible. Hybrid systems, like FWT-AQIM, can even handle content on low-power devices like the Raspberry Pi 5, enabling real-time protection across IoT and mobile platforms [4].
These frequency-based techniques also provide natural defense against spatial distortions, as explored below.
Protection Against Geometric Attacks
Geometric alterations, such as rotation, cropping, scaling, and perspective distortion, can pose significant challenges for watermark detection. Transform domain methods counter these attacks using specific mathematical properties. For instance, the Redundant Discrete Wavelet Transform (RDWT) offers shift invariance, ensuring that watermarks remain detectable even when content is cropped or shifted [6].
For more complex manipulations like rotation and perspective distortion, Möbius Transformations can enhance the robustness of watermarks [6]. Additionally, the Discrete Fourier Transform (DFT) is highly effective because its magnitude spectrum remains stable despite spatial shifts [7]. Tests show that QR-code watermarks can keep a Bit Error Rate (BER) under 5% even after ±30° rotations. Meanwhile, RDWT systems have achieved a Peak Signal-to-Noise Ratio (PSNR) of over 68 dB with a BER of 0.0000, demonstrating nearly perfect invisibility and recovery [4][6].
Cross-Media Adaptability
Beyond compression and geometric challenges, transform domain embedding is versatile enough to protect various types of media, including images, videos, and audio. Implementations based on FWT make it possible to apply robust watermarking even on low-power devices. This allows creators to embed watermarks in real time during content capture or upload – a crucial advantage for managing diverse media across multiple platforms to prevent digital piracy [4].
2. Feature-Invariant and Keypoint-Based Embedding
Keypoint-based embedding strengthens watermark resilience by leveraging the structural features of media. Instead of relying on pixel-based coordinates, this technique anchors watermarks to consistent visual landmarks like corners, edges, or textured regions. These landmarks are identified using tools such as SIFT, SURF, or Harris corner detectors [2].
Protection Against Geometric Attacks
This method excels at withstanding geometric distortions like rotation, cropping, and perspective changes. For instance, if a watermark is embedded around three corner points of a logo, those points maintain their spatial relationship even after transformations. This allows detectors to recognize the keypoints and reconstruct the watermark. Unlike traditional pixel-based methods, this approach adapts naturally to changes in geometry by focusing on structural features. According to a survey on cross-media document watermarking, local structure–based and keypoint-based techniques outperform older methods when dealing with challenges like blur, uneven lighting, and distortions caused by camera capture, especially under screen-shooting conditions [2].
Cross-Media Adaptability
A standout feature of this method is its ability to ensure reliable watermark detection across various media formats, including videos, print-scan workflows, and social media captures. In video content, for example, the watermark is linked to visual objects that persist across frames, rather than fixed screen positions. This makes it resistant to issues like temporal cropping, frame dropping, or re-encoding. Such object-based anchoring proves especially effective where frequency-based techniques falter, particularly with dynamic or fast-changing content.
Ease of Detection and Proof of Ownership
Keypoint-based watermarks remain detectable even after alterations like compression or downsampling, enabling automated detection across diverse media. When combined with cryptographic tools like digital signatures or blockchain-based checksums, they provide robust proof of ownership for legal purposes. Tools such as ScoreDetect take advantage of this resilience, achieving high detection rates across platforms. This reliability strengthens the enforcement of DMCA notices and legal claims across jurisdictions, laying the groundwork for secure, end-to-end watermarking systems that protect cross-media content effectively.
3. Redundancy, Error Correction, and Multi-Channel Embedding
Embedding multiple watermarks offers a safety net: if one is tampered with, others remain intact. Redundancy involves placing repeated watermarks in different areas – whether in spatial regions, frequency bands, or time segments. This ensures that even if compression or cropping damages one copy, others remain detectable. Pairing this with error-correcting codes (ECCs) like Reed-Solomon or LDPC enhances protection. These codes allow the detector to reconstruct the original message, even when a significant chunk of data is compromised [2]. This layered approach enables the distribution of watermark bits across multiple dimensions of the signal.
Resilience to Format Transformations
Multi-channel embedding spreads watermark data across spatial, frequency, and temporal domains, making it resistant to common alterations. For images, this involves embedding in both low- and mid-frequency Discrete Cosine Transform (DCT) or wavelet coefficients, while also distributing the payload across multiple spatial blocks. In video, the same ECC-encoded watermark repeats across consecutive frames and is embedded in both luminance and chrominance channels. For audio, embedding data in time-frequency tiles across stereo channels ensures that techniques like lossy compression or equalization can’t completely erase the watermark. This multi-dimensional strategy strengthens resilience against format-specific attacks [3].
Cross-Media Adaptability
Building on multi-channel embedding, ECC encoding ensures watermark durability across various transformations. This means the same logical watermark can withstand changes in format, whether it’s a screenshot, re-upload, or file conversion [3]. For brands distributing content across platforms, this adaptability is crucial. Regardless of how the media is altered, the redundant watermark remains detectable, providing consistent protection.
Ease of Detection and Proof of Ownership
The combination of redundancy and multi-channel embedding boosts detection reliability by aggregating evidence from multiple channels before decoding. By summing signals from different frequency bands or frames, detectors can produce a stronger statistical output, even when individual channels are degraded [3]. This is especially useful for automated systems scanning large volumes of user-generated content. Tools like ScoreDetect utilize these robust embeddings to maintain high detection rates across platforms. Whether the content has been recompressed, cropped, or re-recorded, the ECC-protected watermark still decodes to the same ownership ID. This ID can then be linked to blockchain-anchored checksums, providing verifiable proof of ownership. These advancements not only improve detection accuracy but also strengthen legal claims, offering comprehensive protection for digital assets.
4. AI-Enhanced and Adversarially Trained Watermarking
Deep neural networks are now being used to optimize both the embedding and detection of watermarks, allowing these marks to adapt to content and withstand attempts to remove them in the real world [3][2]. This approach takes watermarking to the next level by dynamically adjusting to transformation tactics as they occur.
Resilience to Format Transformations
Adversarial training plays a key role in preparing watermarks for the challenges they’ll face. The Adversarial Interference Simulation (AIS) method embeds a watermark, introduces distortions like compression artifacts, and then re-embeds another mark. This process helps the system learn how to recover the original watermark, even after multiple layers of distortion [3]. By mimicking common distortions during training, the system ensures that watermarks remain detectable even after users apply these same transformations to stolen content [3][2]. Essentially, this method treats watermarking as a min-max game, where the system continually adapts to counter simulated removal attempts.
Protection Against Geometric Attacks
Content-specific watermarking tailors itself to the unique features of each media file, focusing on stable geometric structures that can endure transformations like rotation, scaling, and perspective shifts [3]. For example, in deepfake detection, hybrid systems like CMark embed watermarks tied to facial contour invariants – geometric features that stay consistent even after face swaps or heavy editing [3]. Instead of embedding marks at the pixel level, these systems anchor protections to structural elements such as edges, feature points, and facial landmarks. These elements are more resilient to geometric changes and can even withstand partial captures or cropping.
Cross-Media Adaptability
Thanks to joint optimization, a single watermarking system can now protect images, videos, and forensic audio watermarking, while ensuring reliable detection across all formats [3]. Modern forensic watermarking combines training with simulated attacks, content-adaptive embedding, and multi-layer payloads to create a unified solution for multiple media types [3]. For example, in document protection, systems designed to resist screen captures can recover watermarks even after challenges like perspective distortion, Moiré patterns, or camera noise from photographing a screen [2]. This flexibility allows organizations to deploy one cohesive system rather than juggling separate tools for different media.
Ease of Detection and Proof of Ownership
AI-based watermark detectors streamline the process by extracting watermarks in a single forward pass through a neural network, making large-scale, real-time scanning possible [3]. When paired with cryptographic commitments – like storing checksums of the original content on a blockchain – these systems turn detection results into verifiable proof of ownership without exposing the original media [3]. For instance, ScoreDetect integrates adversarially-trained watermarks with blockchain-stored checksums, creating tamper-proof chains of custody. This setup not only supports automated takedown requests but also strengthens legal claims, transforming watermarking from a passive safeguard into an active defense mechanism.
5. End-to-End Detection and Proof of Ownership
The final element of creating resilient cross-media watermarks is ensuring they can be detected quickly and at scale, while also serving as legally valid proof of ownership. A watermark that withstands sophisticated attacks but requires hours of manual verification isn’t practical when monitoring thousands of websites or processing millions of files. The entire system – from embedding to enforcement – needs to work automatically.
Ease of Detection and Proof of Ownership
Speed is crucial. Advanced detection systems now use AI to extract watermarks in a single pass, enabling real-time scanning across massive content libraries. However, detection alone isn’t enough. To establish ownership in legal or platform disputes, cryptographic verification is essential. As the Notabene Team explains, "Digital signatures are the gold standard for wallet ownership proof when security, versatility, and compliance are critical" [10]. The same logic applies to digital content: combining watermark detection with blockchain-stored checksums creates tamper-proof evidence without exposing your original files.
ScoreDetect, developed by InCyan, exemplifies this approach by pairing invisible watermarking with blockchain timestamping. When content is protected, ScoreDetect generates a cryptographic checksum and records it on the blockchain to establish an unalterable record of ownership. During detection, the platform’s AI scans the content, matches it against your digital assets, and provides quantitative proof. It even automates delisting notices, achieving takedown success rates exceeding 96%. This end-to-end process transforms watermarking from a passive safeguard into an active enforcement tool. Automated detection ensures scalable enforcement with evidence that stands up to scrutiny.
As platforms and regulators increasingly prioritize evidence-based oversight, verifiable proof has become a necessity. Automated systems that integrate biometric verification, anomaly detection, and cryptographic commitments meet these demands while scaling to accommodate the 22 connected devices the average U.S. household owns [9]. For organizations managing digital content – whether media companies or legal firms – this automation eliminates the need for manual verification [8]. It ensures that every detection can withstand legal challenges or satisfy platform requirements.
Conclusion
Protecting digital content – whether it’s images, videos, or audio – requires a multi-layered approach. The five strategies discussed – transform domain embedding, feature-invariant and keypoint-based embedding, redundancy and error correction, AI-enhanced adversarial training, and end-to-end detection with proof of ownership – work together to build a system that’s both resilient and adaptable. These methods address challenges like format changes and geometric distortions, while AI-enhanced systems, especially those leveraging adversarial training, have shown detection rates exceeding 98% against sophisticated generative model attacks [1][3]. But even the most advanced watermarking technique is only as effective as its ability to be quickly and reliably detected.
To fully safeguard your digital content, embedding techniques must be paired with automated, agile detection systems. Without reliable detection and verification, even the strongest watermarks lose their effectiveness. Modern threats demand a comprehensive approach that combines multiple embedding methods with automated discovery, analysis, and enforcement tools. ScoreDetect plays a crucial role here, offering automated detection backed by blockchain-based verification for tamper-proof ownership records. It also achieves 95% effectiveness in web scraping for content discovery and boasts a 96% success rate in automated takedown notices. This end-to-end system transforms watermarking from a passive defense into an active, scalable enforcement solution.
This layered, attack-aware strategy represents a shift from outdated single-layer methods to a unified, robust defense. Combining two or more approaches – such as transform domain embedding with AI-enhanced training – provides depth, ensuring that if one layer falters, others can compensate. For industries like media, legal, and ecommerce, integrating these methods with tools like ScoreDetect offers automated, scalable protection without the need for manual intervention.
As generative AI continues to advance, the gap between basic watermarking and comprehensive protection will only grow. Regularly benchmarking your systems and integrating advanced detection workflows is critical to staying ahead of evolving threats. Start with ScoreDetect’s free tier for foundational protection, and scale up with advanced features as needed. Combining resilient embedding with verifiable detection is the key to safeguarding your digital assets today and preparing for the challenges of tomorrow.
FAQs
Which watermark strategy should I start with for images, video, and audio?
Invisible watermarking is a smart way to protect images, videos, and audio. This technique embeds hidden watermarks directly into the content, making it tough to remove while staying out of sight for viewers. It’s a seamless way to maintain content integrity without interfering with the user experience, and it works well across different types of media.
How do watermarks survive screenshots, cropping, and re-encoding?
Watermarks are designed to withstand removal attempts such as screenshots, cropping, or re-encoding by employing advanced techniques. Invisible watermarks, for instance, are embedded in ways that are difficult to detect or erase. Methods like frequency domain embedding or spread spectrum techniques ensure these watermarks stay intact, even after alterations. This makes them a dependable tool for protecting and verifying digital assets.
How can I prove ownership legally after a watermark is detected?
To prove ownership legally after identifying a watermark, you can rely on blockchain technology for verifiable proof. By generating a cryptographic hash (checksum), you create a tamper-proof record with a timestamp, which can back your legal claims.
For stronger evidence, combine invisible watermarks – designed to resist removal – with digital signatures or certificates. When paired with forensic analysis and detailed usage reports from advanced content protection tools, these measures establish a clear and reliable chain of ownership, which can be critical in legal disputes.