Perceptual watermarking embeds invisible, machine-readable signals into digital content, such as images, videos, and audio, to combat piracy. These watermarks remain intact despite transformations like compression, cropping, or reformatting, making them a reliable tool for identifying ownership. Unlike metadata or visible logos, which can be easily removed, perceptual watermarks integrate directly into the media’s structure.
Key points:
- How it works: Watermarks are placed in areas less noticeable to human perception, such as textured regions in images or masked frequencies in audio.
- Resilience: Modern methods like DWT, DCT, and advanced techniques like MELB and FreqMark ensure watermarks survive edits, compression, and even AI-based attacks.
- Applications: Used across images, videos, audio, and documents, each medium requires tailored strategies to balance invisibility and durability.
- Blockchain integration: Cryptographic hashes stored on blockchain provide tamper-proof proof of ownership without exposing the original file.
Platforms like ScoreDetect combine perceptual watermarking with blockchain verification and automated tools to identify and address piracy efficiently. These systems offer scalable solutions for protecting digital content in a rapidly evolving media landscape.
Protecting Your Intellectual Property: How Forensic Watermarking Can Help
sbb-itb-738ac1e
Technical Foundation of Perceptual Watermarking
Spatial vs Transform Domain Watermarking: Key Differences
Perceptual watermarking plays a crucial role in combating digital piracy by embedding hidden yet durable identifiers into digital content. These watermarks are designed based on human sensory thresholds, ensuring they remain imperceptible to viewers or listeners. By using perceptual models, watermark signals are strategically placed in areas where human visual or auditory systems are least sensitive [1].
Perceptual Models and Hash Functions
Perceptual hash functions create a fingerprint of content by focusing on its dominant features and semantic information. Unlike cryptographic hashes, which change with even the slightest modification, perceptual hashes remain stable through content-preserving processes like compression or resizing. This stability allows for blind detection using only the suspect file and a secret key [1][4].
To measure how invisible a watermark is, engineers rely on metrics like PSNR (Peak Signal-to-Noise Ratio) and SSIM (Structural Similarity Index). These metrics help maintain a balance between imperceptibility, robustness, and capacity – commonly referred to as the "Watermarking Triangle." Most watermark payloads range from tens to a few hundred bits, and increasing capacity too much can compromise either invisibility or durability [1].
"It is also impossible to imitate or overwrite watermarks because the cryptographic hash of the image and the dominant features of the image in the form of perceptual hash are used as watermarks."
- Sudev Kumar Padhi, Archana Tiwari, and Sk. Subidh Ali [4]
Modern approaches, such as SEAL, use semantic-aware watermarking methods. These leverage locality-sensitive hashing (LSH) to derive watermark keys from an image’s semantic embedding, making the watermark deeply tied to the content’s intrinsic meaning. This makes it harder for generative AI tools or simple copy-paste methods to bypass the watermark [2].
With perceptual hashing providing a strong foundation, transform domain methods further enhance watermark resilience against common media transformations.
Transform Domain Embedding Techniques
Transform domain methods, including Discrete Wavelet Transform (DWT) and Discrete Cosine Transform (DCT), are widely used for embedding watermarks. These techniques break content into frequency components, allowing precise control over where watermark signals are placed. For instance, DWT splits content into multiple scales and orientations, with its low-frequency (LL) band being the preferred embedding region due to its resistance to compression and blurring [3][1]. Similarly, DCT aligns well with JPEG compression standards, enabling watermarks to survive the quantization and entropy coding processes typical in file sharing [1][6].
In December 2025, researchers at the University of Melbourne introduced MELB (Multidimensional Embedding via Localised Blocking), a block-wise DWT watermarking method. This technique divides DWT coefficients into "allowed" and "disallowed" regions using a secret key. While only about 50% of coefficients naturally fall into allowed regions, watermarked images are designed so nearly 100% align with these regions. MELB proved highly durable, surviving up to 50% cropping and achieving true positive rates as high as 91% [3].
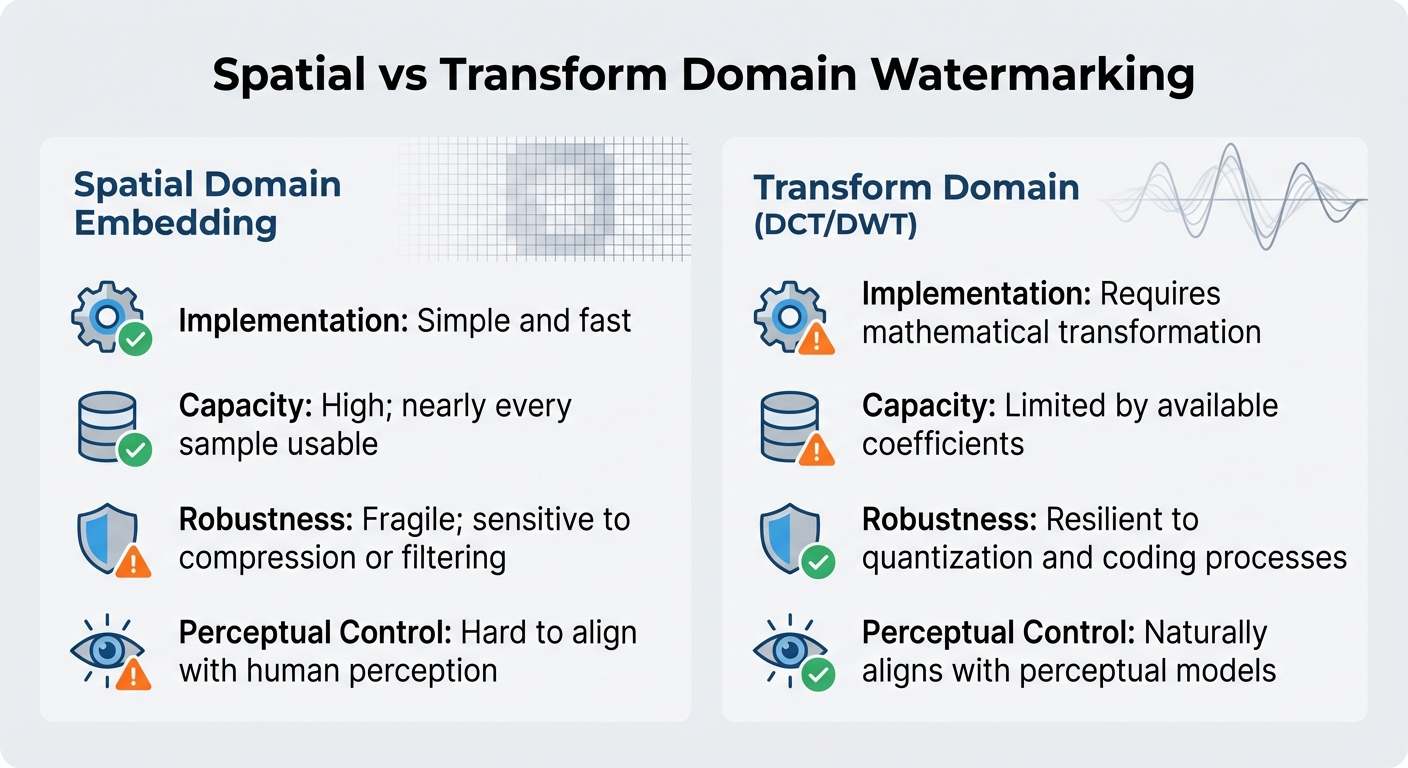
| Feature | Spatial Domain Embedding | Transform Domain (DCT/DWT) |
|---|---|---|
| Implementation | Simple and fast | Requires mathematical transformation |
| Capacity | High; nearly every sample usable | Limited by available coefficients |
| Robustness | Fragile; sensitive to compression or filtering | Resilient to quantization and coding processes |
| Perceptual Control | Hard to align with human perception | Naturally aligns with perceptual models |
In October 2024, researchers from the University of Science and Technology of China and Tencent proposed FreqMark, a method that enhances watermarking in latent frequency spaces using Variational Autoencoders (VAE) and Fast Fourier Transform (FFT). This technique specifically counters AI-driven attacks, such as denoising models designed to remove watermarks. FreqMark demonstrated impressive durability, achieving over 90% bit accuracy when encoding a 48-bit hidden message under various attack scenarios [5].
Perceptual Watermarking Across Different Media Types
Watermarking techniques need to adapt to the unique characteristics of various media types – images, video, audio, documents, and even emerging 3D formats. Each medium requires a specific approach that aligns with how humans perceive and process information.
Image Watermarking Methods
In images, watermarking can occur in two main ways: the spatial domain, where individual pixels are altered, or transform domains like the Discrete Cosine Transform (DCT) and Discrete Wavelet Transform (DWT). A common method is embedding watermark data in textured areas – like foliage or fabric – where changes are less noticeable to the human eye [1][6].
A notable advancement came in 2014 when Matthieu Urvoy and his team at Université de Nantes introduced a Discrete Fourier Transform (DFT) watermarking method. This approach used the Contrast Sensitivity Function (CSF) to adjust watermark strength based on visibility thresholds. It demonstrated resilience against distortions like rotation, scaling, and translation, while remaining undetectable to trained observers. For example, binary watermarks of 4,096 bits have been successfully embedded into 256×256 images [6][7].
However, image watermarking faces significant challenges, particularly when dealing with geometric transformations like cropping, rotation, or scaling, as well as signal processing techniques such as JPEG compression. Transform domain methods often perform better in these scenarios because embedding data into frequency coefficients makes the watermark more resistant to quantization and entropy coding [1][7].
These techniques form the foundation for tackling the added complexity of synchronizing watermarks in moving images.
Video Watermarking Developments
Video watermarking builds upon image techniques but adds a time-based dimension, requiring synchronization across frames. This temporal aspect introduces unique challenges, as watermarks must remain intact during compression processes like Groups of Pictures (GOP) encoding, while also avoiding visual artifacts. The watermark must also withstand common alterations such as transcoding, frame dropping, and re-timing, which frequently occur when content is shared on different platforms [1].
"The success of a watermarking algorithm not only depends on its embedding strategy, but also on its detection strategy."
- Matthieu Urvoy, Université de Nantes [7]
Audio and 3D Content Watermarking
In audio, watermarking leverages psychoacoustic masking, embedding signals into frequency ranges that are naturally obscured by louder or more complex sounds [1]. These watermarks must blend seamlessly with the audio while enduring processes like normalization, equalization, and compression (e.g., MP3 or AAC). As with images and video, the goal is to balance invisibility with robustness against typical processing methods.
For documents and 3D formats, watermarking requires tailored strategies. Documents might use adjustments to text layout, font styles, or even full-page rasterization to embed watermarks. Meanwhile, 3D content demands adaptive methods capable of withstanding changes in localization or accessibility [1].
| Media Type | Primary Perceptual Mechanism | Key Technical Challenge |
|---|---|---|
| Images | Texture and luminance masking | Surviving geometric changes (cropping, rotation) |
| Video | Temporal masking and GOP awareness | Preventing flicker and maintaining synchronization |
| Audio | Psychoacoustic frequency masking | Enduring lossy compression (MP3/AAC) and re-sampling |
| Documents | Layout and font-based embedding | Handling rasterization and text reflow |
Blockchain Technology in Watermarking Systems
Blockchain technology tackles a key issue in digital rights management: how to prove ownership without exposing the original content. Traditional systems often rely on storing large media files or maintaining centralized databases, which can be vulnerable to breaches. Blockchain offers an alternative by creating an unchangeable, timestamped record of ownership that exists independently of the content itself.
Blockchain-Based Ownership Verification
Instead of uploading entire media files like images, videos, or audio to the blockchain – which would be expensive and inefficient – modern systems store compact cryptographic hashes. These hashes act as digital fingerprints, capturing the unique features of an asset in a way that’s nearly impossible to duplicate or falsify [4].
"Many organizations now complement traditional evidence management systems with cryptographically verifiable ledgers inspired by blockchain designs."
This method enables the creation of a "verified chain of custody," a technique often used for safeguarding educational content and other high-value intellectual property.** Every action – whether embedding, verifying, or detecting a watermark – is logged with a permanent timestamp. This provides rights holders with a way to prove when their content was registered, offering critical evidence in legal disputes [1].
Moreover, blockchain facilitates privacy-preserving verification. Ownership or licensing status can be confirmed through the blockchain record without requiring access to the original high-resolution file or proprietary watermarking tools [1]. This means third parties like regulators or automated systems can independently verify rights without exposing sensitive content.
However, storing these immutable records efficiently requires innovative storage solutions, which has led to the development of hybrid models.
Off-Chain Storage Solutions
Directly storing billions of media files on a blockchain isn’t feasible due to performance limitations. To address this, hybrid storage models have emerged, balancing security and scalability. In these systems, the blockchain stores only cryptographic checksums and metadata, while the actual media files are kept in high-performance off-chain storage systems [1][8].
"Rather than storing media content on chain, these ledgers store compact records of detection events and key evidence hashes. The result is a time stamped, tamper evident log that can be shared with partners and regulators while keeping underlying media and proprietary algorithms under strict control."
- InCyan Research [1]
This setup enables "blind watermarking" on a large scale. Detection systems can scan platforms for copyright violations using only the suspect asset and reference data stored on the blockchain – eliminating the need to access the original, unmarked file [1]. For platforms handling millions of assets daily, this approach makes automated enforcement practical and scalable.
Another technique, zero-watermarking, extracts intrinsic features from an image to generate a watermark sequence without altering any pixels [8]. The resulting data is stored securely off-chain, with its cryptographic hash placed on the blockchain. This ensures the asset’s integrity remains untouched, which is vital for applications like medical imaging or legal documents. Platforms like ScoreDetect rely on this process to maintain content integrity in sensitive scenarios.
ScoreDetect‘s Digital Piracy Prevention Solutions

ScoreDetect uses well-established research methods to create a robust platform for tackling digital piracy. By combining invisible watermarking, blockchain timestamping, and automated enforcement, the system offers tools to combat piracy across various media formats, including images, videos, audio, and documents. Developed by InCyan, this solution directly addresses modern piracy challenges, such as unauthorized transformations and widespread distribution.
Invisible Watermarking and Content Discovery
At the core of ScoreDetect’s system is its ability to embed invisible digital signals into media files. These watermarks act as permanent identifiers, surviving alterations like cropping, compression, or metadata removal. This ensures ownership details remain intact and recoverable. The platform’s discovery engine, which scans the web for unauthorized content, boasts an impressive 95% success rate. This allows rights holders to stay vigilant, continuously monitor online platforms, and quickly identify potential infringements [1].
Takedown and Analysis Tools
Once piracy is detected, ScoreDetect springs into action by issuing automated delisting notices. With a takedown success rate of over 96%, it ensures swift removal of unauthorized content. The system also generates detailed evidence by matching the discovered content with original reference files. Its verification pipeline meticulously documents every step – tracking how evidence is gathered, accessed, and handled. This creates a reliable chain of custody, which is vital for legal or regulatory purposes [1].
Blockchain Timestamping and Workflow Integration
ScoreDetect also leverages blockchain technology to strengthen ownership claims. By generating cryptographic checksums of content and recording them on a blockchain, the system provides time-stamped, tamper-proof proof of ownership. Importantly, this method secures ownership without exposing the actual digital assets [1].
To streamline operations, ScoreDetect integrates with over 6,000 web apps via Zapier, helping organizations automate their protection processes. Additionally, a dedicated WordPress plugin allows publishers to create blockchain-backed ownership records for every article they publish or update. This not only safeguards content but also enhances SEO by signaling its authenticity to search engines.
Conclusion
Perceptual watermarking has become a powerful tool in the fight against digital piracy. By embedding signals directly into digital assets, these watermarks remain intact even after social media compression or AI-based edits. Unlike metadata, which can vanish with a simple re-export, these watermarks serve as a lasting identifier. As Nikhil John from InCyan describes it, they function as a "latent serial number for the work itself" [1]. The technology strikes a delicate balance between being invisible to users, resilient to tampering, and capable of holding essential data.
Modern solutions leverage blind detection and deep learning to counter forgery attempts, combining cryptographic and perceptual hashes [4]. This approach is essential when managing vast libraries of digital assets across global platforms.
These advancements lay the groundwork for effective piracy prevention tools. For example, ScoreDetect integrates these principles to safeguard digital content. Its invisible watermarking withstands challenges like cropping, compression, and metadata stripping. Meanwhile, its discovery engine boasts an impressive 95% success rate in locating unauthorized content. Additionally, the platform automates content takedowns with a 96% removal rate, supported by blockchain-based timestamping that ensures tamper-proof ownership records without exposing sensitive assets.
FAQs
How is perceptual watermarking different from metadata?
Perceptual watermarking involves embedding information directly into digital content, ensuring that it’s invisible to viewers while remaining resistant to changes like cropping or compression. On the other hand, metadata stores information externally, such as in file headers, which makes it more vulnerable to removal or modification. This difference gives perceptual watermarking an edge as a more durable and tamper-resistant way to safeguard digital content.
Can a watermark survive cropping and social media compression?
A well-crafted watermark can endure significant cropping – up to half the image – while still holding up against the compression applied by social media platforms. Recent studies emphasize the success of invisible digital watermarking methods, which balance durability with being undetectable to the human eye in these challenging conditions.
How does blockchain prove ownership without storing the file?
Blockchain confirms ownership by creating a checksum of the content, which serves as a unique digital fingerprint. This method verifies ownership without storing the actual digital file, maintaining both security and privacy.

