Digital watermarking embeds hidden information into media files to protect intellectual property and track misuse. But real-world challenges like compression, resizing, cropping, and deliberate attacks can weaken or erase these watermarks. To address this, developers must balance three factors: invisibility, durability, and data capacity.
Key Takeaways:
- Compression Issues: JPEG and MP3 compression can remove high-frequency details, often where watermarks are embedded.
- Geometric Changes: Resizing, cropping, and rotating disrupt the watermark’s spatial alignment.
- Noise and Filtering: Gaussian noise, blur, and attacks like salt-and-pepper noise can distort or erase watermarks.
- Advanced Techniques: New methods like PWFN (Picking Watermarks From Noise) and Fourier Transform embedding improve resistance to distortions and attacks.
Solutions:
- Diffusion Models: Embed watermarks into the noise layer of images for better durability.
- Fourier Transform: Focus on low-frequency embedding to withstand compression.
- Enterprise Tools: Platforms like ScoreDetect combine watermarking with blockchain for ownership proof and automated content monitoring.
Watermarking systems are evolving to handle these challenges, but achieving a balance between quality, durability, and usability remains critical.
Tree-Ring Watermarks: Fingerprints for Diffusion Images that are Invisible and Robust (Explained)
sbb-itb-738ac1e
Main Challenges in Maintaining Watermark Integrity
Watermarks are susceptible to a variety of distortions that can weaken or even erase the embedded signals. Understanding these vulnerabilities is key to developing systems that can endure the challenges posed by content distribution.
Compression Distortions
Compression methods like JPEG for images and MP3/AAC for audio are designed to reduce file sizes by discarding data considered unnecessary or imperceptible to the human eye or ear [1]. However, this process often strips away the high-frequency components where watermarks are typically embedded to remain invisible. For example, JPEG quantization can disrupt deep learning models’ ability to extract watermarks effectively [2]. Similarly, in audio, psychoacoustic masking – where louder sounds obscure quieter ones – can unintentionally remove parts of the watermark signal [1].
"A watermark that disappears after a single round of social media transcoding or minor color correction does not help rights holders."
– Nikhil John, InCyan [1]
To balance robustness and quality, modern systems rely on metrics like Peak Signal-to-Noise Ratio (PSNR) and Structural Similarity Index (SSIM) [1][2].
Scaling and Geometric Transformations
Geometric transformations, such as cropping, rotation, scaling, and changes in aspect ratio, disrupt the spatial alignment of an image. For instance, scaling or aspect ratio changes can misalign the watermark, making it difficult for detectors to locate. Cropping can physically remove the watermark unless it’s redundantly embedded [1]. Experimental models like PWFN have achieved a Bit Accuracy Rate (BAR) of 98.45% under a 3.5% cropping attack. However, more aggressive cropping – removing up to 30% of the image – remains a significant hurdle [2].
"Visible marks can be cropped away… Properly designed invisible watermarks can survive those transformations and act as a latent serial number for the work itself."
– Nikhil John, InCyan [1]
In video content, geometric changes like frame dropping, insertion, or re-timing introduce synchronization issues, complicating the maintenance of alignment over time [1]. Blind detection methods, which work without needing a pristine reference file, are especially crucial in these scenarios [1][2].
Additive Noise Attacks
Additive noise, whether from environmental factors or deliberate attacks, can distort the watermark and hinder its extraction. While deep learning–based watermarking methods using encoder-noise-decoder (END) architectures can resist mild noise, they often fail under more severe conditions [2]. For instance, traditional models like ReDMark may show only 50.00% robustness against Gaussian Blur (2.0) [2]. In contrast, the PWFN model, equipped with a denoising module, achieved a BAR of 99.99% under Gaussian Blur and 95.85% under JPEG compression [2]. Tests on the COCO dataset revealed that PWFN maintained a PSNR of 36.34 and an SSIM of 0.98, achieving an average robustness of 98.84% across various noise conditions [2].
"Watermarked images are frequently subject to intentional or unintentional attacks during dissemination, which can result in image distortion… These distorted images may cause the failure of watermark extraction."
– Sijing Xie et al., Huazhong University of Science and Technology [2]
Adversarial attacks, such as those introducing Gaussian or salt-and-pepper noise, pose additional threats to watermark integrity [1][2]. In generative AI contexts, synthetic transformations can create "hallucinated" content, adding further noise and complicating watermark retrieval [1].
Filtering Attacks
Filtering operations, like smoothing or averaging pixel values, can erase the subtle variations that encode watermarks. Advanced techniques, such as those identified by the WAVES benchmark, have uncovered new vulnerabilities to diffusive and adversarial attacks [5]. These findings highlight the need for watermarking methods that can evolve alongside emerging attack strategies.
Technical Methods to Address These Challenges
To tackle vulnerabilities in watermarking, researchers and developers have crafted systems that can endure the challenges of content distribution. These solutions rely on mathematical models, machine learning techniques, and embedding strategies to ensure watermarks persist through compression, noise, and other distortions.
Diffusion Models and Initial Noise Resistance
Embedding watermarks directly into the initial noise of diffusion models weaves them into an image’s foundational structure. This approach enhances their resistance to compression and additive noise by building protection into the image from the outset.
In December 2024, Kasra Arabi and colleagues introduced a two-stage framework that combines initial noise with embedded Fourier patterns, achieving impressive resistance to forgery and removal attacks [3]. Meanwhile, the PWFN (Picking Watermarks From Noise) model, developed by Sijing Xie and colleagues in May 2024, incorporates a denoising module – often a Unet or FCN architecture – between the noise layer and the watermark decoder. This framework treats watermark recovery as an image restoration task and achieved a high average BAR of 98.84% under various attacks, including JPEG compression, 30% cropout, and Gaussian blur [2].
"The innovative introduction of the denoise module improves the robustness of the watermarking model by recovering the watermark information lost due to noise."
– Sijing Xie et al., Huazhong University of Science and Technology [2]
Another advancement, the VINE framework, developed by Shilin Lu and colleagues and accepted at ICLR 2025, uses large-scale pretrained diffusion models like SDXL-Turbo as watermark encoders. This method leverages generative priors to embed signals that are both harder to detect and more resilient to advanced editing. In testing, VINE maintained 24.5% accuracy against unguided diffusion regeneration attacks, outperforming older methods like StegaStamp (7.4% accuracy) and TrustMark (12.8% accuracy) [6][7].
"Diffusion-based image editors can produce photorealistic modifications… potentially obliterating the low-level details that encode a watermark while preserving high-level semantics."
– Fan Guo et al., Xidian University [7]
While diffusion models improve resistance to noise during image generation, transform domain methods offer additional protection against compression and editing.
Fourier Transform Patterns for Better Resilience
Transform domain techniques embed watermark data into frequency coefficients rather than raw pixels, making them less vulnerable to compression and filtering. By focusing on low-frequency regions, these methods take advantage of how compression codecs work, ensuring watermarks remain both invisible and durable during quantization [1][2].
"Watermarked signals in the low-frequency part possess greater robustness."
– Sijing Xie et al., Huazhong University of Science and Technology [2]
One two-stage approach uses Fourier patterns to identify the group of initial noises used during generation and then matches the specific noise pattern within that group [3]. Transform domain methods also allow for blind detection, meaning watermarks can be recovered using only the suspect asset and reference parameters, without needing the original unmarked file [1].
These technical advancements are complemented by enterprise solutions like ScoreDetect, which integrate these robust methods to deliver practical, scalable content protection.
Invisible Watermarking with ScoreDetect

ScoreDetect offers a seamless solution for safeguarding digital assets with invisible watermarking technology. Its system embeds undetectable watermarks into images, videos, audio, and documents, ensuring protection against unauthorized use. These watermarks are designed to endure compression, geometric transformations, noise, and filtering attacks, making them resilient across social media platforms, streaming services, and file-sharing networks.
Beyond watermarking, ScoreDetect provides a full suite of content protection tools. The Discover feature uses intelligent web scraping to identify unauthorized content with a 95% success rate, while the Analyse function matches discovered content to its original source with quantitative proof. When infringement is detected, the Take Down feature automates delisting notices, achieving a 96% success rate in removing unauthorized content [ScoreDetect Enterprise].
The platform also incorporates blockchain technology to enhance digital watermarking and generate verifiable proof of ownership through cryptographic checksums, eliminating the need to store digital assets directly. ScoreDetect integrates with over 6,000 web apps via Zapier, enabling automated workflows to protect content at scale.
Plans start at $11.31 per month (yearly billing) for blockchain timestamping and basic protection features. The Enterprise plan offers advanced invisible watermarking, 24/7 monitoring, automated takedown notices, and dedicated support. A 7-day free trial is available for all plans, allowing users to test the platform’s capabilities against their specific needs.
From cutting-edge diffusion models and Fourier transforms to robust enterprise solutions, these methods strengthen watermark durability in the face of the challenges outlined earlier.
Comparison of Watermarking Robustness
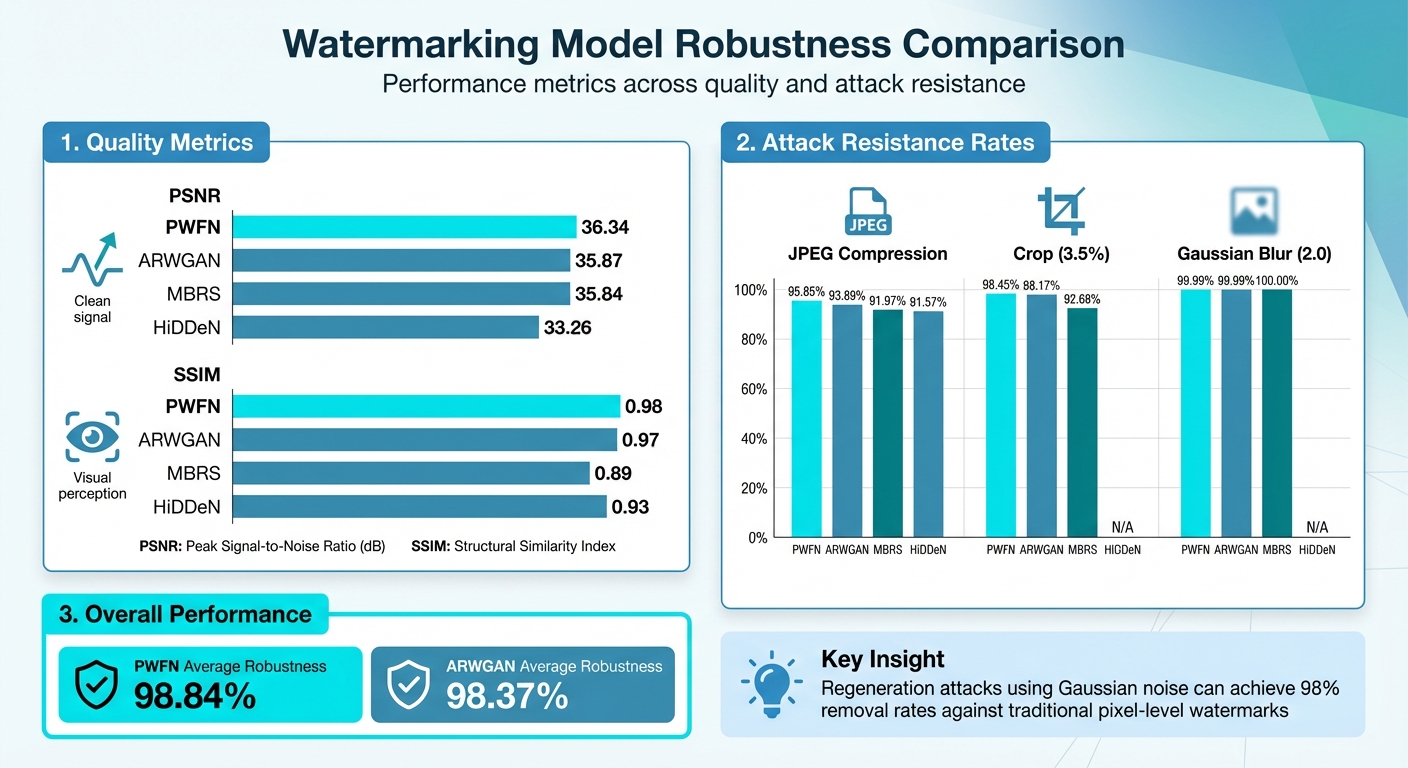
Watermarking Model Performance Comparison: PSNR, SSIM, and Robustness Metrics
Noise Resilience Metrics
When it comes to testing watermark performance under different noise conditions, the results show clear differences between various techniques. For instance, researchers tested the PWFN model on the COCO dataset with 30-bit messages and 128×128 images. The results were impressive: the model achieved 95.85% accuracy against JPEG compression and 98.45% accuracy against 3.5% random cropping. These high accuracy rates were made possible by incorporating denoising techniques [2].
Here’s a breakdown of the key quality and robustness metrics for different watermarking models:
| Model | PSNR | SSIM | JPEG Compression | Crop (3.5%) | Gaussian Blur (2.0) |
|---|---|---|---|---|---|
| PWFN | 36.34 | 0.98 | 95.85% | 98.45% | 99.99% |
| ARWGAN | 35.87 | 0.97 | 93.89% | 98.17% | 99.99% |
| MBRS | 35.84 | 0.89 | 91.97% | 92.68% | 100.00% |
| HiDDeN | 33.26 | 0.93 | 91.57% | N/A | N/A |
Looking at the table, it’s clear that PWFN consistently outshines other models. It achieves an average robustness of 98.84% across all tested attacks, compared to 98.37% for ARWGAN [2]. These results highlight the importance of advanced techniques in resisting various noise scenarios.
Attack Success Rates
Beyond noise resilience, it’s crucial to understand how watermarking methods hold up against deliberate removal attempts.
Regeneration attacks, which target pixel-level watermarks, pose a significant challenge. For example, regeneration attacks using Gaussian noise can achieve removal rates as high as 98% [4].
However, newer approaches, such as diffusion-based and Fourier-augmented methods, show greater resistance to such attacks. A two-stage retrieval framework, which embeds information into initial noise and augments it with Fourier patterns, has proven highly effective. Tools like ScoreDetect leverage these techniques, achieving a 96% success rate for automated takedown notices [3].
This brings us to a critical trade-off: robustness versus security. As one study puts it:
"Current ‘robust’ watermarks sacrifice security for distortion resistance, providing insights for future watermark design" [8].
For enterprise-level solutions, striking the right balance between invisibility, attack resistance, and payload capacity is essential. These findings emphasize the need for embedding techniques that can withstand real-world challenges while maintaining the integrity of digital content protection.
Conclusion
Safeguarding digital content in a world full of noise and distortion is no small feat. Watermarks need to withstand compression, geometric tweaks, and deliberate removal attempts, all while staying invisible and carrying enough data to prove ownership. Invisible watermarking offers a crucial safety net, ensuring assets remain traceable even when platforms strip metadata or heavily transcode content [1].
These advancements carry real-world weight for various industries. Media, finance, healthcare, and legal sectors, in particular, face high stakes when it comes to digital asset protection. Advanced frameworks have shown they can hold up against common distortions, maintaining a reliable chain of custody. For example, solutions like ScoreDetect don’t just use invisible watermarking – they pair it with blockchain timestamping, and their automated takedown notices boast a success rate exceeding 96% [2].
The key to effective content protection lies in mastering the "watermarking triangle": balancing invisibility, durability, and capacity. To get it right, businesses need to map the journey of their high-value assets, rigorously test watermark strength under real-world conditions, and integrate these systems with tools to detect and address unauthorized use [1].
As traditional protection methods face increasing threats from sophisticated attacks, AI-driven tools for embedding and denoising have become essential. These advanced strategies are critical in defending digital assets against the ever-evolving challenges of piracy and misuse.
FAQs
Which attacks most often break invisible watermarks?
Regeneration attacks are a popular approach to compromise invisible watermarks. These methods often involve adding random noise to an image and then reconstructing it. The goal? To erase pixel-level watermarks while keeping the image itself intact and visually appealing.
How do you balance invisibility, durability, and payload size?
Balancing invisibility, durability, and payload size in digital watermarking is all about finding the sweet spot where content stays protected without losing its quality.
- Invisibility means the watermark blends seamlessly into the content, so it’s undetectable to the naked eye.
- Durability ensures the watermark can withstand challenges like compression, noise, or other distortions.
- Payload size refers to how much data the watermark can carry, which is optimized by embedding information in less noticeable areas to preserve both visual quality and resilience.
The real challenge lies in striking the right balance. Advanced algorithms play a crucial role, tailoring the watermarking process to suit the specific media type and the environment in which it will be used.
How does ScoreDetect prove ownership after heavy editing?
ScoreDetect provides a way to prove ownership of content even after substantial edits. It does this by creating a blockchain-based checksum of the material. This checksum serves as a verifiable marker of ownership, eliminating the need to store the actual digital files.