AI and perceptual hashing are two key methods used to identify and track digital content, even after edits or transformations. Here’s the main takeaway:
- Perceptual Hashing: Uses algorithms to create compact binary fingerprints of content. It’s fast, efficient, and works well for minor edits like resizing or compression. However, it’s less effective against major changes like rotations or heavy cropping.
- AI-Driven Fingerprinting: Employs neural networks to generate high-dimensional embeddings that capture deeper features of content. This method is more resilient to complex edits (e.g., heavy cropping, color grading) but requires higher computational resources.
Key Differences:
- Speed: Perceptual hashing is faster and lightweight, ideal for quick duplicate detection.
- Accuracy: AI methods are better at handling heavily modified content, with a recall rate of 67% compared to 25% for perceptual hashing.
- Cost: Perceptual hashing is cheaper to implement, while AI requires GPUs and more storage.
When to Use:
- Perceptual Hashing: For minor edits and large-scale, low-cost filtering.
- AI Fingerprinting: For detecting complex transformations or protecting high-value content.
A hybrid approach – using perceptual hashing for initial filtering and AI for deeper analysis – offers a balanced solution for digital content protection.
USENIX Security ’23 – Squint Hard Enough: Attacking Perceptual Hashing with Adversarial Machine…
sbb-itb-738ac1e
Understanding Perceptual Hashing
Perceptual hashing creates a compact digital fingerprint by analyzing the overall structure of visual or audio content [4]. Unlike cryptographic hashing – where even a tiny change in input results in a completely different hash – perceptual hashing focuses on capturing broader patterns while ignoring minor details. For instance, the perceptual hash of an image reflects its layout of light and dark regions, as well as dominant shapes [4]. As MetaGhost explains:
This technology is called perceptual hashing, and it is the foundation of how platforms detect duplicate and reposted content at scale [4].
How Perceptual Hashing Works
The process starts by simplifying the content to its core features. For images, this often involves resizing the file to a small grid – commonly 8×8 or 9×8 pixels – and then analyzing brightness patterns, pixel gradients, or frequency components [4]. The result is a compact binary string, typically 64 bits, that uniquely identifies the content [4]. This design allows for efficient indexing and comparison of large datasets [5].
Perceptual hashes use Hamming distance to measure similarity. A lower Hamming distance between two hashes indicates that the images are visually alike, even if their sizes or formats differ [1]. This sets the groundwork for comparing perceptual hashing with newer AI-driven fingerprinting techniques in content protection.
Common Perceptual Hashing Algorithms
Several algorithms dominate the field of perceptual hashing, each tailored to specific use cases:
- Average Hash (aHash): Converts an image to grayscale and compares each pixel to the average brightness [4]. It’s quick but highly sensitive to changes in brightness, making it suitable for basic duplicate detection [1].
- Difference Hash (dHash): Focuses on relative pixel differences, which makes it more robust against brightness changes [1].
- Perceptual Hash (pHash): Leverages the Discrete Cosine Transform (DCT) to isolate low-frequency components in the frequency domain [4]. It performs well against filters, JPEG compression, and resizing [1].
- BlockHash: Divides an image into blocks and calculates the mean value for each section, offering better resistance to transformations like cropping or rotation [1].
For audio, HashWave uses features like MFCC (Mel-frequency cepstral coefficients), chroma, and CQT, combined with Dynamic Time Warping, to detect unauthorized copies even after pitch shifting or time stretching [3]. Released in February 2025, HashWave achieved an impressive Area Under the Curve (AUC) of 0.957 and a True Positive Rate of 0.952 at a 1% False Positive Rate [3]. While these methods are effective against common edits, they face challenges when dealing with advanced adversarial techniques like removal attacks.
Strengths and Limitations of Perceptual Hashing
Perceptual hashing stands out for its speed and efficiency. Algorithms generate compact signatures quickly, making them well-suited for indexing and comparing massive collections of content. These hashes are resilient to common modifications like resizing, JPEG compression, color filtering, and minor cropping [4].
However, the technology has notable weaknesses. As TrufoAI highlighted in a September 2025 benchmark:
pHash is fast and simple. It’s prone to hash collisions, and only works on about 25% of type ‘A’ augmentations [2].
Perceptual hashing struggles with major transformations such as large rotations, perspective changes, and extreme cropping [4]. It also fails to account for semantic context, focusing solely on pixel patterns [4]. This makes it vulnerable to adversaries who exploit these gaps with subtle pixel changes that alter the hash without visible differences [5]. For example, Apple discontinued its NeuralHash CSAM scanner in December 2022 after researchers demonstrated how imperceptible changes could cause hash collisions [5].
The HashWave research team also noted the limitations of these approaches:
Perceptual hashing and MFCC-based approaches provide compact representations, but remain sensitive to non-linear distortions such as tempo warps or pitch shifts [3].
These challenges have pushed many businesses to explore AI-driven solutions as a more resilient alternative. These often involve deep learning for detection to overcome the limitations of traditional hashing.
AI-Driven Content Fingerprinting Explained
AI-powered fingerprinting has moved beyond the limitations of pixel-based analysis, using deep neural networks to capture the deeper meaning of content. This process creates robust 512-dimensional embedding vectors that represent the essence of the content [4].
How AI Improves Content Fingerprinting
Instead of focusing on raw pixels, AI fingerprinting relies on neural networks – like Convolutional Neural Networks (CNNs) or ResNet50 – to analyze structural and semantic features. This results in embedding vectors that encapsulate the content’s identity. Meta‘s SSCD (Self-Supervised Copy Detection) model is a prime example of this technique [4].
Similarity detection is achieved through cosine similarity between these embedding vectors. For instance, the SSCD system flags two images as copies if their cosine similarity exceeds 0.75 [4]. This approach enables the system to detect duplicates even after significant alterations. As MetaGhost explains:
SSCD is dramatically more robust than pHash. It can detect copies that have been heavily cropped, color-graded, overlaid with text, compressed through multiple rounds of JPEG, and even screenshotted [4].
Emerging systems are now adopting hybrid provenance schemes, combining AI fingerprinting with invisible watermarking and blockchain-based authorship verification to ensure tamper-proof records [5][7]. Models like DINOHash are pushing boundaries further, using adversarially fine-tuned DINOv2 features to maintain accuracy under heavy cropping and compression [5].
Unlike traditional perceptual hashing, which relies on pixel-level patterns, AI-driven fingerprinting incorporates semantic analysis. This makes it far more effective at handling complex modifications, strengthening content verification across a wide range of transformations.
Strengths of AI in Content Protection
AI fingerprinting has shown clear improvements in detection accuracy. For example, TrufoAI’s benchmark revealed that their AI-driven fingerprint achieved a recall of 67% at 99% precision, compared to only 25% recall for the industry-standard PDQ algorithm under the same conditions [2].
One of the standout features of AI systems is their ability to perform semantic matching. Neural networks analyze high-level features, allowing them to identify near-duplicates even after heavy editing or stylization [4]. This includes transformations that traditional hashes struggle with, such as large rotations, perspective shifts, and extreme cropping.
| Feature | Traditional Perceptual Hashing | AI-Driven Fingerprinting |
|---|---|---|
| Core Technology | DCT / Gradients | Deep Neural Networks |
| Output Type | 64-bit Binary String | 512-dimensional Vector |
| Recall Rate | ~25% on heavy edits | ~67%+ on heavy edits |
| Semantic Understanding | None (pixel-based only) | High (context-aware) |
| Robustness | Fails on rotations/crops | Resilient to geometric changes |
The evolution of AI fingerprinting marks a shift from simple "is-match" tools to advanced identifiers capable of tracking content provenance and aiding information retrieval [2].
Limitations of AI-Based Fingerprinting
While AI fingerprinting offers significant benefits, it also comes with some challenges. Training these advanced models demands substantial computational resources. For instance, training a 674-million-parameter model on 512,000 samples requires around 240 GPU hours on high-performance hardware like the NVIDIA H200 [8]. This makes implementation more expensive compared to traditional methods.
Another issue is the verification bottleneck. AI systems generate hypotheses rather than definitive answers. As Lauri Korpela points out:
If each output requires meaningful effort to validate, then the usefulness of the entire system is bounded by human throughput, regardless of how fast generation becomes [10].
AI fingerprints are also vulnerable to adversarial attacks, where subtle, invisible pixel changes can alter an image’s embedding vector just enough to evade detection [4]. These attacks exploit the opaque nature of neural networks, making it hard to explain how matches are identified. This lack of transparency can pose challenges in legal contexts, where clear evidence is often required [6][9].
Despite these challenges, the superior detection capabilities of AI fingerprinting – especially for complex transformations – make it a compelling choice. Platforms like InCyan‘s Idem are addressing many of these limitations. Idem’s AI system can identify content ownership even when only 10% of the original remains, offering a robust solution for organizations seeking reliable content protection.
AI vs. Perceptual Hashing: Direct Comparison
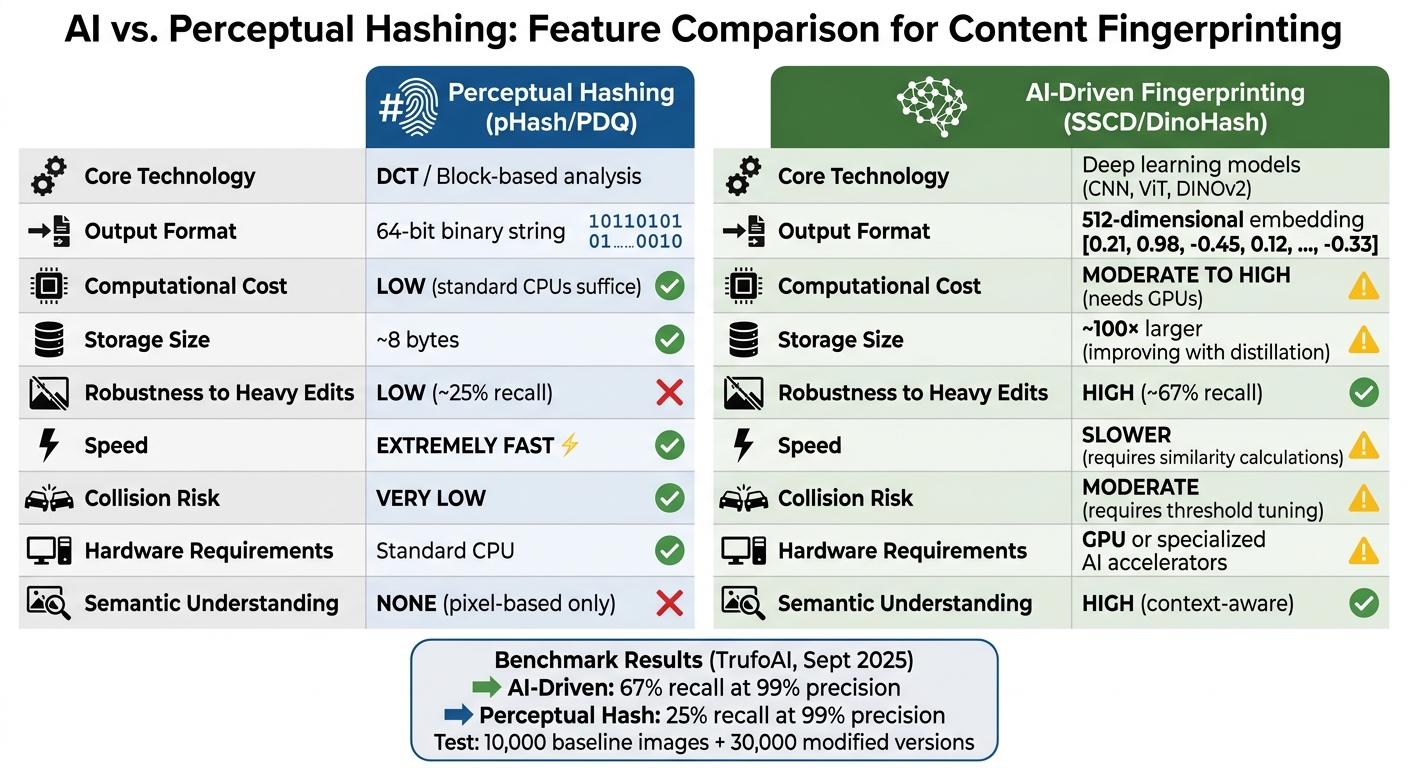
AI vs Perceptual Hashing: Feature Comparison for Content Fingerprinting
This comparison showcases how both methods uniquely contribute to protecting digital rights through a digital fingerprint for content verification. A September 2025 TrufoAI benchmark analyzed 10,000 baseline images alongside 30,000 modified versions. The AI-driven fingerprint achieved 67% recall at 99% precision, whereas traditional algorithms like PDQ and pHash only identified 25% of the modified images [2].
Feature Comparison Table
| Feature | Perceptual Hashing (pHash/PDQ) | AI-Driven Fingerprinting (SSCD/DinoHash) |
|---|---|---|
| Core Technology | DCT / Block-based analysis | Deep learning models such as CNN, ViT, and DINOv2 |
| Output Format | 64-bit binary string | 512-dimensional embedding vector |
| Computational Cost | Low (standard CPUs suffice) | Moderate to high (needs GPUs or dedicated AI hardware) |
| Storage Size | ~8 bytes | Approximately 100× larger (improving with distillation) |
| Robustness to Heavy Edits | Low (~25% recall) | High (~67% recall) |
| Speed | Extremely fast | Slower (requires similarity calculations) |
| Collision Risk | Very low | Moderate (requires threshold tuning) |
| Hardware Requirements | Standard CPU | GPU or specialized AI accelerators |
Traditional perceptual hashing shines in speed and compactness, while AI models like DinoHash – optimized by reducing parameters from 400M to under 30M – strike a balance between efficiency and scalability. Each method has its strengths, depending on the application.
When to Use Perceptual Hashing
Perceptual hashing is ideal for scenarios where speed and low resource usage are priorities, and content undergoes only minor changes. For instance, it’s a great choice for internal duplicate detection in photo libraries where users are not intentionally bypassing filters. This method excels at identifying exact or nearly exact matches, such as resized or compressed images, with few false positives [2] [4].
However, it struggles with heavily modified content, making it less effective for environments where adversarial edits are common.
When to Use AI-Driven Fingerprinting
AI-driven methods shine in detecting content that has undergone significant edits or transformations. Platforms that face adversarial modifications – like public social networks – benefit greatly from AI’s ability to match content semantically, even when only fragments remain [4].
For example, InCyan’s Idem platform can identify ownership even when just 10% of the original asset is present. AI methods are also versatile, as modern neural networks can process multimodal assets such as video, audio, and text using similar embedding techniques. While computational requirements are higher – TrufoAI’s 2025 benchmark utilized an AMD Ryzen 9950X3D CPU and an NVIDIA RTX 5090 GPU – the improved detection rates justify the investment [2].
For organizations managing large-scale digital assets, a hybrid approach is often the most effective. Perceptual hashing can act as a fast first-pass filter to catch exact matches, while AI embeddings provide deeper analysis for flagged content. This combination balances speed and accuracy, ensuring comprehensive content protection.
Combining AI and Perceptual Hashing for Content Protection
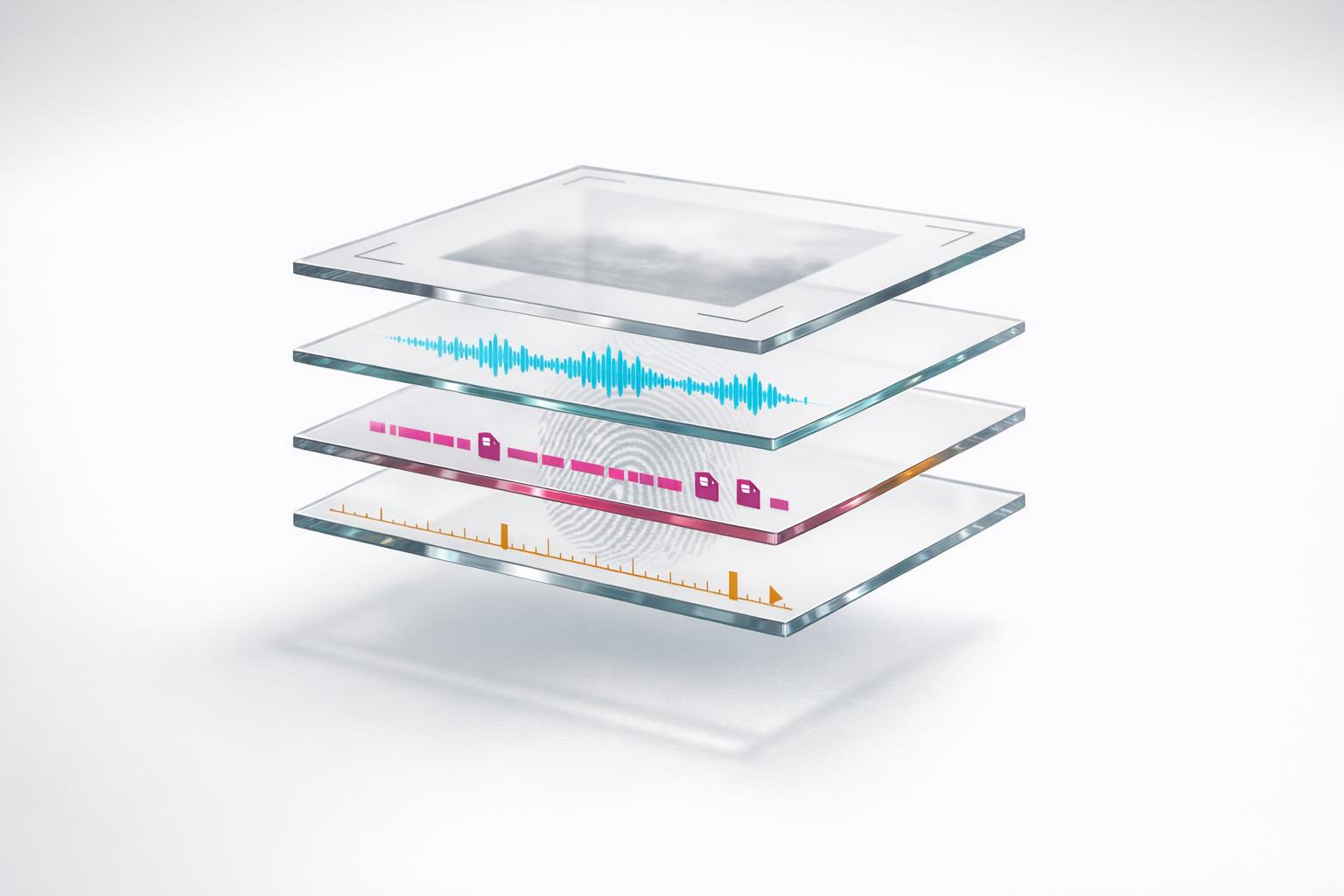
How These Technologies Work Together
When it comes to protecting digital content, a layered approach works best. Perceptual hashing serves as a quick, initial filter, identifying exact or near-exact duplicates with minimal computing power. But if content slips through that filter and still seems suspicious, AI-driven fingerprinting steps in. This method digs deeper, analyzing the content on a semantic level. Together, these technologies strike a balance: perceptual hashing handles large volumes quickly, while AI tackles more complex transformations.
The technical requirements for these methods vary. Perceptual hashing can run efficiently on standard CPUs, making it perfect for indexing vast amounts of data. On the other hand, AI-driven fingerprinting demands more processing power, but advancements have made it more practical. AI models can now be slimmed down to under 30 million parameters, enabling efficient deployment on edge devices while outperforming traditional methods in cases involving significant content alterations [2].
This hybrid method is particularly useful for content provenance systems, where the focus shifts from simple duplicate detection to pinpointing specific content within massive databases. As TrufoAI puts it:
The role of fingerprinting is to act as an identifier, so the technical demands on precision and recall are much higher [2].
Organizations managing vast digital libraries can use perceptual hashing to quickly eliminate obvious mismatches. Then, AI embeddings can step in to analyze flagged content that has been extensively edited, color-graded, or altered through screenshots. This two-step strategy also lays the groundwork for additional security measures.
Adding Blockchain and Watermarking
To strengthen this layered detection system, blockchain and invisible watermarking add extra layers of protection. While fingerprinting is excellent for detection, combining it with blockchain timestamping** and **invisible watermarking enhances content security and ownership tracking. InCyan’s ScoreDetect, for instance, uses blockchain to create an immutable record of content ownership without storing the actual files. This provides a reliable "first-seen" timestamp, which is invaluable for copyright infringement counterclaims, especially for creators, legal teams, and media organizations.
For cases requiring absolute precision, invisible watermarking becomes critical. InCyan’s Tectus platform embeds unnoticeable watermarks into images, videos, and audio files. These watermarks remain intact even after heavy modifications, offering undeniable proof of ownership. As TrufoAI explains:
When 100% precision is important, watermarks are far more powerful than fingerprints. Fundamentally, watermarks allow you to modify the content, but fingerprints do not, so they must be stronger [2].
Together, these tools form a comprehensive content protection system. Fingerprinting detects unauthorized copies online, blockchain secures ownership records, and watermarking provides solid evidence for legal enforcement. By combining these technologies, companies like InCyan help organizations maintain control over their digital assets from creation to enforcement.
Real-World Applications and Use Cases
Real-world applications highlight how advanced technologies safeguard digital assets against piracy and ensure the authenticity of content.
Preventing Digital Piracy
Platforms like Instagram, Facebook, and TikTok use unique digital fingerprints for each upload, enabling them to identify duplicate and unauthorized reposts on a large scale [4]. In 2022, Meta rolled out its SSCD (Self-Supervised Copy Detection) system across Facebook and Instagram. This system, powered by a ResNet50 neural network, generates 512-dimensional embedding vectors for every image. If the cosine similarity between these vectors exceeds 0.75, the system flags the upload as a duplicate [4].
What sets SSCD apart is its ability to detect heavily modified copies. Whether an image has been cropped, color-graded, overlaid with text, or subjected to multiple rounds of JPEG compression or screenshots, SSCD can still identify it. This makes it a powerful tool for combating piracy, enabling platforms to intercept unauthorized content uploads in real time.
For larger-scale digital libraries, InCyan’s Idem platform offers enterprise-level protection. Its AI-driven multimodal matching technology can identify ownership even when only 10% of the original content remains intact. This means it can handle alterations like memes, mobile edits, cropping, and compression. Paired with InCyan’s Indago, which can de-index unauthorized links in less than an hour, rights holders can effectively disrupt piracy by addressing it at the source of traffic.
Verifying AI-Generated Content
As piracy methods evolve, verifying the authenticity of AI-generated content has become equally important. Fingerprinting technologies now play a pivotal role in tracking the origins of digital files. In February 2026, researchers Apoorv Mohit and colleagues proposed a system for verifying AI-generated images using a perceptual hash registry stored on a public blockchain. This framework uses a Merkle Patricia Trie for on-chain storage and a Burkhard–Keller tree for off-chain similarity searches. Social media platforms can use this system to identify registered AI-generated content as it is uploaded [7].
Ensuring content authenticity requires precision, especially when distinguishing between original and manipulated versions. Combining multiple technologies enhances this process. For instance, blockchain timestamping and invisible watermarking work together to improve verification. InCyan’s ScoreDetect leverages blockchain to create an immutable record of content ownership without storing the actual files. This "first-seen" timestamp is particularly useful for copyright claims. Meanwhile, Tectus embeds invisible watermarks into images, videos, and audio files that remain intact even after significant modifications, offering clear proof of ownership.
In October 2023, Meta introduced "Stable Signature", a watermarking method based on latent-diffusion generators. This innovation represents a significant step forward in tracking the provenance of AI-generated content [5]. By combining these approaches, content creators, legal teams, and media organizations gain essential tools to protect and manage their digital assets in a complex and ever-changing digital environment.
Choosing the Right Approach for Your Needs
Selecting between AI fingerprinting and perceptual hashing depends on factors like how much the content is altered, your computational resources, and whether you need legally defensible evidence. Perceptual hashing is great for detecting minor changes like resizing or slight brightness tweaks. However, it struggles with heavily altered content, such as significant cropping, pitch shifts, or time stretching. On the other hand, AI-driven models excel at identifying content even after extensive modifications, making them invaluable for combating sophisticated manipulations [2].
Budget and infrastructure are key considerations. Perceptual hashing is cost-effective, operating efficiently on standard CPUs, which makes it a solid choice for organizations handling billions of uploads with limited budgets. In contrast, AI-driven fingerprinting requires more powerful GPU-class hardware and generates larger embedding vectors. For instance, Meta’s SSCD produces 512-dimensional vectors, while classical perceptual hashing relies on compact 64-bit strings [4]. If you’re working with tight budgets and need fast filtering, perceptual hashing on standard CPUs is the way to go. However, for protecting high-value assets against advanced attacks, AI-based models offer stronger safeguards, albeit at a higher cost. For environments with limited computational power, like edge devices or on-premise setups, perceptual hashing remains practical. But for scenarios where legal scrutiny is critical, additional measures are necessary.
Legal and compliance requirements also play a significant role. Perceptual hashing provides a clear and deterministic process that courts and regulators can easily verify. In contrast, AI models often function as "black boxes", which can raise concerns about their reliability as legal evidence [6]. To address this, combining fingerprinting with blockchain timestamping and invisible watermarking can create verifiable proof. Platforms like ScoreDetect and InCyan’s Tectus specialize in these capabilities, ensuring robust legal protection.
For most organizations, a hybrid approach works best. Perceptual hashing can handle quick, low-cost filtering of exact or near-exact duplicates, helping to reduce computational demands. Meanwhile, AI-driven fingerprinting is ideal for safeguarding high-value assets that are vulnerable to advanced piracy methods, such as heavy editing or "re-filming." For large-scale operations managing millions of assets, InCyan’s Idem platform offers AI-powered multimodal matching that can identify ownership even if only 10% of the original content remains [2]. These tools integrate seamlessly into advanced content protection systems, enabling a tailored strategy that meets diverse needs.
Ultimately, your protection strategy should reflect the specific threats you face. Media companies dealing with professional piracy will benefit from the robustness of AI-driven systems. Content creators worried about casual redistribution might start with perceptual hashing combined with establishing ownership with timestamps through platforms like ScoreDetect. If legal teams need evidence that stands up in court, invisible watermarking paired with blockchain verification becomes essential. By weighing these trade-offs, you can create a content protection system that balances cost, performance, and legal reliability to meet your specific challenges.
FAQs
How do I set similarity thresholds to avoid false matches?
To fine-tune similarity thresholds in perceptual hashing, start by examining the Hamming distance distribution between both related and unrelated images. This step helps you understand how similar or dissimilar your images are based on the hash values.
Next, test your hashing algorithm with a mix of known duplicates and unrelated image samples. This allows you to pinpoint a cutoff value that effectively identifies true matches while keeping false positives to a minimum.
It’s also important to regularly adjust these thresholds as your dataset evolves. Use your existing data and validate the thresholds against known samples to ensure the balance between sensitivity (catching true matches) and specificity (avoiding false positives) is preserved.
Can AI fingerprinting run without GPUs at scale?
AI fingerprinting can operate on CPUs, but the process is far more efficient with GPU acceleration, especially for large-scale tasks. While CPUs can technically manage the workload, they lack the speed and practicality needed for handling extensive operations. GPUs, with their ability to perform parallel processing, significantly boost the performance of AI algorithms. This makes them the preferred choice for faster and more scalable AI fingerprinting.
When do I need watermarking or blockchain proof, not just fingerprinting?
Watermarking and blockchain proof play a key role in ensuring ownership, provenance, and authenticity of digital content. While perceptual hashing can detect similar or altered content, it often falls short when faced with deliberate tampering. On the other hand, watermarking embeds durable markers directly into the content, and blockchain proof establishes an unchangeable record of ownership. Together, these methods go beyond simple identification, offering robust tools for legal and copyright protection.