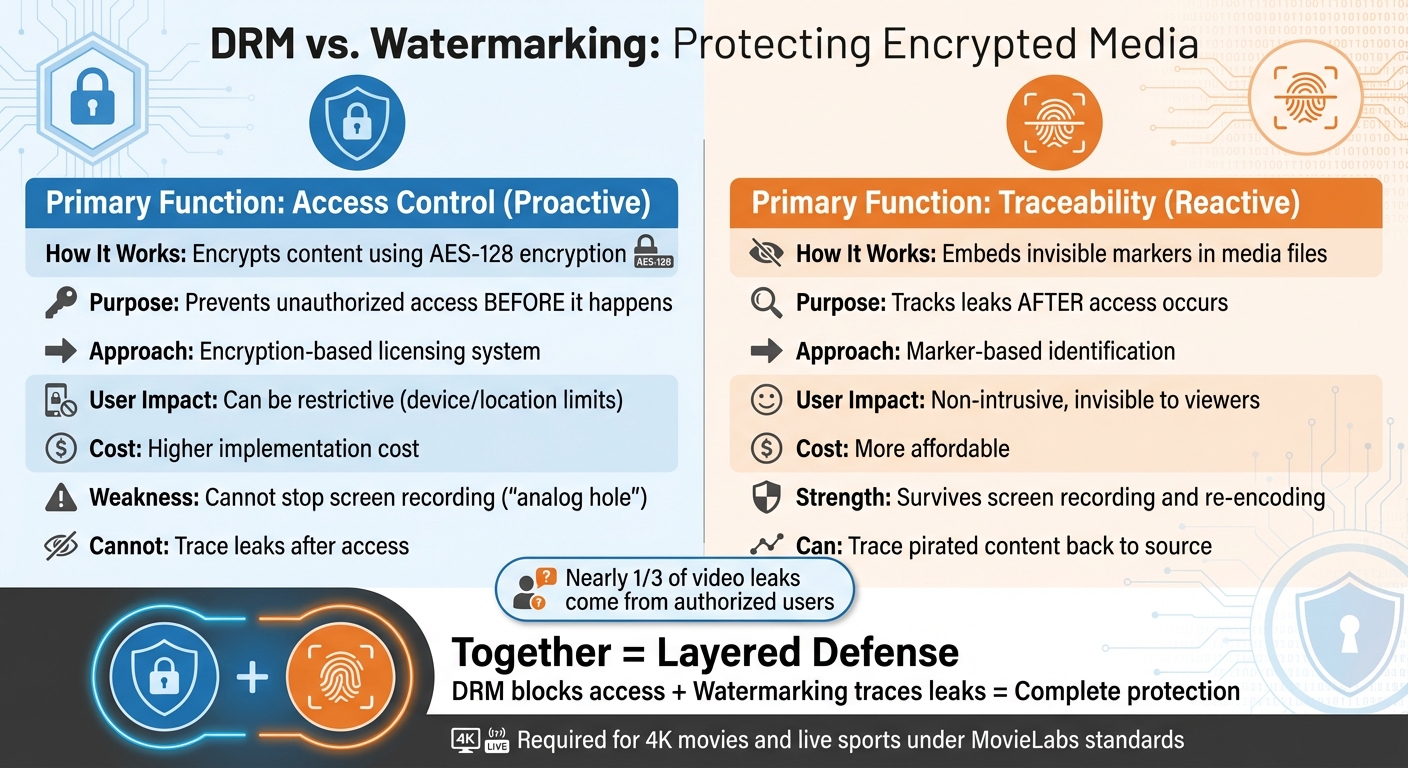
Digital piracy costs the U.S. economy billions annually, affecting creators and studios alike. Two key tools combat this: DRM (Digital Rights Management) and watermarking.
- DRM encrypts content to control access, ensuring only authorized users can view it.
- Watermarking embeds invisible identifiers into media, making it possible to trace leaks back to their source.
While DRM prevents unauthorized access, it can’t stop screen recording ("analog hole"). Watermarking fills this gap by staying embedded even after decryption or recording. Combining both offers a layered defense for high-value content like 4K movies or live sports streams.
Quick Comparison:
| Feature | DRM | Watermarking |
|---|---|---|
| Functionality | Access control | Traceability |
| Approach | Encryption-based | Marker-based |
| Piracy Prevention | Stops unauthorized access | Tracks leaks after access |
| User Impact | Can be restrictive | Non-intrusive |
| Legal Use | Compliance support | Evidence for enforcement |
Together, DRM and watermarking create a stronger system, balancing access control with traceability.
DRM vs Watermarking: Key Differences in Digital Content Protection
Inside Streaming’s Two-Layer Defense: DRM and Watermarking
sbb-itb-738ac1e
How DRM Works
DRM functions as a system designed to control access to content based on user, time, location, and device. At its core, it relies on encryption and licensing systems to secure media files. These two components work hand in hand to ensure only authorized users can access the content.
Let’s break down how these components operate.
Encryption and Licensing Systems
When you upload a video to a DRM-enabled platform, the system encrypts the file to make it inaccessible without proper authorization. Roman K. from BuyDRM explains it like this:
"A video is encrypted using a key that is stored securely with a DRM platform… Each time a DRM-protected video needs to be played, the video distributor triggers a DRM license key which is sent to the end-user’s device for decryption and playback" [3].
This encryption process creates a locked file that remains secure during storage and transmission. The decryption key, stored on a secure DRM platform, is only accessible when a user attempts playback. At that point, the user’s device sends a request to the DRM system’s licensing API. Once validated, the system sends back a license key containing permissions, which the media player uses to decrypt and play the content.
To accommodate different devices, most streaming platforms use a multi-DRM strategy. For example:
- Apple devices rely on FairPlay.
- Android devices use Google Widevine.
- Windows systems utilize Microsoft PlayReady.
Without supporting all three, platforms risk excluding large sections of their audience.
In addition to controlling access, DRM enforces specific business rules. For instance, it can:
- Restrict content to certain geographic regions (geo-blocking).
- Limit rentals to a 48-hour viewing period.
- Prevent casting to external screens.
- Block high-resolution playback on devices lacking hardware-level DRM, ensuring premium streams are only accessible on secure devices.
DRM Strengths and Weaknesses
DRM is highly effective at preventing unauthorized access before it happens. Its encryption makes it nearly impossible for casual users to download and share files. It’s also protected under laws like the Digital Millennium Copyright Act (DMCA) in the U.S. and international agreements such as the WIPO Copyright Treaty, making it illegal to bypass these protections [4].
That said, DRM isn’t without its flaws. Skilled attackers can bypass DRM using specialized tools, though invisible watermarks resist removal attacks more effectively [4]. Another limitation, often referred to as the "analog hole", is that DRM cannot stop users from recording their screen while content is playing. Once the content is decrypted for legitimate playback, DRM’s protection is no longer effective.
Perhaps the most significant downside is that DRM offers no way to trace leaks. If someone pirates your content, DRM alone cannot identify the source. This is why many providers pair DRM with watermarking, which adds traceable identifiers to the content, creating a more comprehensive security system [3].
How Watermarking Works
Watermarking embeds subtle, nearly invisible markers directly into media files. These markers create a forensic trail, making it possible to trace the source of leaks using digital piracy solutions with watermarking, even after the content has been decrypted for legitimate viewing [1]. Unlike DRM, which focuses on preventing unauthorized access, watermarking remains effective even if someone uses screen recording to bypass protections.
These embedded markers are detectable with specialized tools and are designed to withstand common piracy techniques like re-encoding, cropping, resizing, and screen recording [3]. By complementing DRM’s pre-access safeguards, watermarking adds an extra layer of defense for encrypted media. Let’s dive into two key types of watermarking that help ensure content traceability.
Forensic and Dynamic Watermarking
Forensic watermarking works by embedding unique identifiers into media files, allowing leaks to be traced back to specific users or devices. A popular method, A/B watermarking, involves creating two versions of each video segment (labeled A and B). The content delivery network then assembles these segments into a unique pattern – such as ABAABBAAA – for each subscriber based on their ID [3].
Roman K. from BuyDRM explains the process like this:
"Forensic investigators can examine the pattern of the segments and determine which subscriber ID was used to leak the movie." [3]
This method is highly scalable, as it avoids the need to create entirely unique files for every viewer. On the other hand, dynamic watermarking embeds personalized data – like email addresses, IP addresses, or timestamps – into the media. These identifiers can be visible or invisible, acting as a proactive deterrent. While forensic watermarking focuses on tracing leaks after they occur, dynamic watermarking discourages piracy upfront, making it especially useful for pre-release content like screeners [6].
Watermarking Strengths and Weaknesses
Watermarking offers a critical advantage: it remains effective even after content is decrypted or recorded, providing traceability that DRM alone cannot [1]. For premium content like 4K movies or live sports, forensic watermarking is often mandatory under the MovieLabs Specification for Enhanced Content Protection [1].
Beyond traceability, watermarking also serves as legal evidence. When a leak is identified, the embedded markers provide clear proof of who accessed the content and when. This is particularly important because authorized users, not external hackers, are responsible for nearly one-third of video leaks [6].
However, watermarking has its limitations. It’s reactive, not preventive – it doesn’t stop piracy but helps identify the source afterward. Sophisticated attackers may attempt to remove or damage watermarks through aggressive re-encoding or other tampering techniques. That said, robust watermarking systems are specifically designed to resist these efforts [3]. Another limitation is that some solutions require a minimum video length – typically around five minutes – for the watermarks to be effectively embedded and extracted [5].
DRM vs. Watermarking: Key Differences
DRM relies on AES-128 encryption to block unauthorized access, while watermarking embeds traceable markers that remain intact even if the content is copied or recorded. These two technologies serve different purposes, addressing vulnerabilities at distinct stages of content protection. The table below highlights their main differences.
Comparison Table: DRM vs. Watermarking
| Feature | DRM | Watermarking |
|---|---|---|
| Functionality | Proactive (access control) | Reactive (traceability) |
| Security Approach | Encryption-based | Marker-based |
| User Experience Impact | Can be restrictive | Non-intrusive |
| Cost Considerations | Higher implementation cost | More affordable |
| Legal Protection | Supports compliance | Provides evidence for enforcement |
| Implementation Complexity | High | Moderate |
Using DRM and Watermarking Together
To achieve the best content protection, combining DRM and watermarking in a layered approach is highly effective. DRM controls access during the delivery and consumption phases, specifying who can view the content, when, and on which devices. Watermarking, on the other hand, creates a traceable link between pirated copies and individual users, offering a way to track leaks back to their source.
DRM alone has limitations, such as the analog hole, which watermarking helps address. Roman K. from BuyDRM explains the synergy between the two:
"With a combination of DRM, business and license rules, and session-based watermarking, your streaming service stands a great chance at preventing piracy."
For premium content like 4K movies or live sports, this dual approach is often a requirement under industry standards. While DRM prevents unauthorized access, watermarking acts as both a deterrent and a tool for enforcement when breaches occur. Together, they provide the robust protection needed for today’s high-value content.
Implementing Watermarking for Encrypted Media
By combining the strengths of DRM with watermarking, content owners can enhance post-access traceability for encrypted media. However, deploying these technologies together requires careful planning to ensure seamless integration.
Server-Side vs. Client-Side Watermarking
Server-side watermarking involves embedding invisible markers during the encoding process or when delivering sessions. This approach creates two visually identical video chunks, often labeled A and B. Each subscriber receives a unique sequence of these chunks (e.g., ABAABBAAA), based on their subscriber ID. This sequence acts as a distinct, traceable fingerprint.
On the other hand, client-side watermarking embeds markers during playback on the user’s device. While this method offers flexibility, it demands robust security to protect the embedded keys. Without strong safeguards, users might bypass the watermarking system [3].
For high-value content such as 4K movies or live sports, server-side watermarking is often preferred. Its embedded markers are resilient to common transformations, making it highly effective for tracing leaks.
With these methods outlined, let’s explore how ScoreDetect leverages them for comprehensive protection.
ScoreDetect for Content Protection

ScoreDetect combines DRM with advanced watermarking techniques to deliver strong content security. By integrating with existing DRM systems, it embeds invisible watermarks across multimedia content, protecting it against unauthorized use while maintaining its quality.
Beyond watermarking, ScoreDetect uses AI-driven web scraping with a 95% success rate in spotting unauthorized content online. Once flagged, the system verifies findings with quantitative proof and generates delisting notices and takedowns, achieving a success rate of over 96%.
Additionally, ScoreDetect employs blockchain timestamping to capture content checksums without storing actual files. This provides verifiable proof of ownership, bolstering copyright protection and aiding legal enforcement. The platform also connects with over 6,000 web apps via Zapier, enabling automated workflows that integrate directly into content management systems. For WordPress users, a dedicated plugin creates blockchain-verified ownership proof for every article update, enhancing SEO efforts.
ScoreDetect serves industries like media, entertainment, legal, and marketing. It offers self-service plans for individual creators and enterprise solutions, complete with dedicated success managers and 24/7 support.
Conclusion
Securing encrypted media demands a multi-layered strategy. DRM serves as the gatekeeper, employing 128-bit AES encryption to block unauthorized access. At the same time, watermarking plays the role of the detective, embedding invisible markers that persist through screen recording and re-encoding, enabling content owners to trace leaks back to their source [1] [2]. While DRM is effective at locking down access, it isn’t foolproof – screen capture tools can bypass it. This is where watermarking steps in, ensuring traceability even after content has been decrypted and redistributed.
Individually, these technologies have limitations. But together, they create what experts call "glass-to-glass" protection [1]. This combined approach not only strengthens security but also makes enforcement more manageable for content owners. It’s especially vital for high-value assets like live sports and 4K streaming, where piracy directly cuts into revenue.
To address these challenges, many businesses managing premium content turn to solutions that simplify implementation. ScoreDetect offers an integrated approach, combining invisible watermarking with AI-driven monitoring and automated takedown processes. With a 95% success rate in identifying unauthorized content and a 96% takedown rate, it allows businesses to focus on creating content rather than combating piracy.
FAQs
When should I use DRM, watermarking, or both?
When deciding how to protect your content, consider DRM, watermarking, or a combination of both, depending on your needs.
- DRM (Digital Rights Management): This is perfect for controlling access and preventing unauthorized use. It’s commonly used for streaming platforms or digital sales, where restricting who can view or use the content is essential.
- Watermarking: This method embeds invisible markers into your content, making it possible to trace leaks or unauthorized sharing. It’s especially useful for identifying the source of a breach.
For maximum protection, you can combine DRM and watermarking. DRM ensures access is tightly controlled, while watermarking adds traceability to track any leaks. This dual approach is ideal for high-value or sensitive content where both access control and leak identification are crucial.
How does watermarking still work after screen recording?
Watermarking continues to function effectively even after screen recording by embedding subtle, undetectable markers directly into the content. These markers stay embedded and can be identified, even if the content is recorded, enabling verification and tracking of any misuse.
What’s the easiest way to add watermarking to a DRM workflow?
The simplest way to include watermarking in a DRM workflow is by embedding invisible markers directly into the content. This approach boosts security by enabling forensic tracking of unauthorized distribution. Most watermarking tools work well with DRM systems, making it easy to integrate them without interfering with access controls. This added layer of protection helps trace leaks and pinpoint the sources of unauthorized sharing.