Digital watermarks are essential for protecting content ownership, but attackers have developed sophisticated methods to bypass them. This article explores how adversarial attacks target watermark systems and evaluates the resilience of various watermarking methods. Key points include:
- Attack Types: Regeneration attacks, forgery techniques, diffusion-based editing, and transferable attacks are used to remove or fake watermarks.
- Resilience Testing: Standardized metrics like Attack Success Rate (ASR) and forensic detection are critical for assessing watermark durability.
- Recent Advances: Techniques like Pattern Stability Score (PSS) and SEEK improve detection accuracy and resistance to attacks.
- Enterprise Tools: Solutions like InCyan‘s Tectus and blockchain-based ScoreDetect offer advanced content protection.
Watermarking technologies are evolving to counter threats, but no single method is foolproof. Combining strategies, such as multi-layer defenses, offers stronger protection against tampering and unauthorized use.
[WACV2026] AEON Adaptive Embedding Optimized Noise by Muneer Muhammad Shahid
sbb-itb-738ac1e
Recent Research on Watermark Resilience
Ongoing research is pushing the boundaries of watermark resilience, particularly against adversarial attacks. By focusing on stability-aware detection methods and redundancy-based protection, researchers are addressing the vulnerabilities of traditional watermarking systems. Below are some of the most notable advancements in this area.
Invisible Watermarks and Generative AI Attacks
In February 2026, researchers Sina Mansouri, Mohit Marvania, and Abolfazl Safikhani introduced the Pattern Stability Score (PSS) framework at ICLR 2026. Unlike basic global threshold methods, PSS evaluates local statistical features and tracks stability across multiple paraphrasing rounds. This approach proved highly effective when tested on the PG-19 long-form benchmark, where it maintained a detection AUC above 0.95 at full text length – even after eight paraphrasing rounds using the Mistral-7B model. Under the same conditions, traditional z-score detectors failed to perform effectively [4].
Notably, PSS improved watermark detection AUC by 10–15 percentage points across varying token lengths. This represents a major step forward in combating generative AI models that attempt to erase watermarks through repeated paraphrasing. Such progress underscores the importance of resilient watermarking as a key tool in protecting digital content.
Diffusion-Based and Reconstruction Attacks
Recent research has brought attention to the scrubbing–spoofing trade-off in watermarking. Smaller watermark windows, which span fewer than four tokens, are better at resisting paraphrasing but are vulnerable to reverse engineering. Attackers can forge these watermarks for under $50. On the other hand, larger windows are harder to forge but can be stripped away with localized text edits.
"The efficacy of such adversarial attacks is not primarily due to their sophistication, but rather the inherent limitations of conventional schemes that force a direct compromise between scrubbing and spoofing robustness."
– NeurIPS 2025 Research Team [5]
To address this issue, researchers Huanming Shen, Baizhou Huang, and Xiaojun Wan proposed the SEEK (Sub-vocabulary decomposed Equivalent tExture Key) scheme at NeurIPS 2025. This method decouples watermark construction across separate sub-vocabularies, achieving significant robustness improvements. For instance:
- Spoofing resistance: Gains of +88.2% on the Dolly-CW dataset and +92.3% on MMW-BookReports compared to standard KGW-Min baselines.
- Scrubbing resistance: Gains of +10.2% on WikiText and +13.4% on C4 datasets [5].
These results highlight SEEK’s effectiveness in balancing scrubbing and spoofing defenses, offering a more reliable watermarking solution.
Watermark Forgery Techniques
Statistics-based spoofing attacks have revealed how attackers can manipulate watermark patterns to frame models or inject unauthorized signatures. These attacks exploit the predictable statistical distributions of conventional watermarking schemes, particularly those using small watermark windows. SEEK addresses this issue by introducing equivalent texture keys, which allow multiple tokens within a window to independently support detection [5].
This redundancy enables the use of larger watermark windows, significantly increasing the computational burden for attackers. Specifically, the sample complexity for spoofing scales at O(|V|^h), where V is the vocabulary size and h is the window size [5]. Additionally, SEEK has shown strong resistance against both DIPPER-based paraphrasing attacks and low-cost statistical spoofing, all while maintaining high-quality text output [5].
These advancements collectively mark a significant leap forward in watermarking technology, offering more robust defenses against increasingly sophisticated adversarial techniques.
Comparing Watermarking Methods
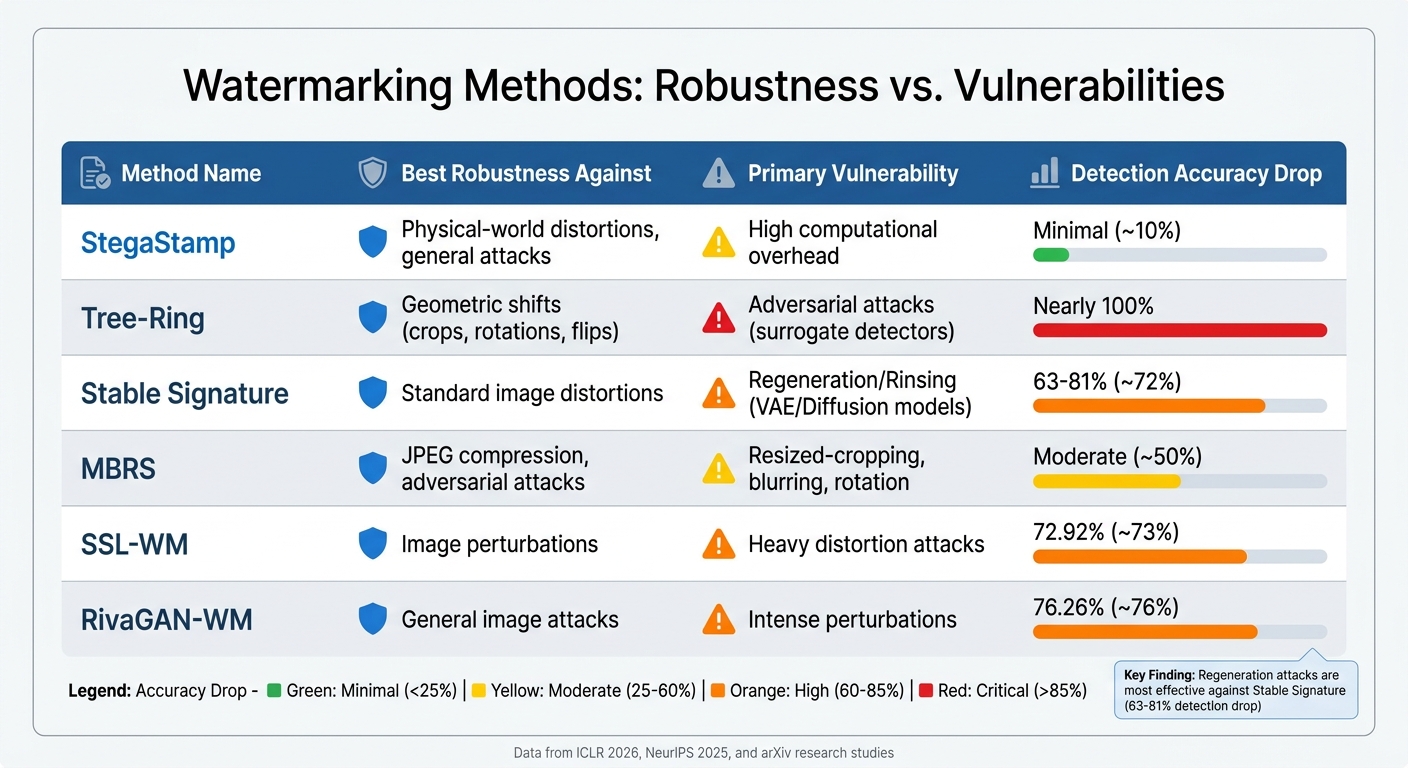
Watermarking Methods Performance Comparison: Robustness and Vulnerabilities
Recent studies have taken a comprehensive approach to measuring how well watermarking methods hold up under various conditions, using standardized metrics to evaluate their resilience and performance.
Measurement Criteria
Assessing watermark resilience involves more than just checking if the watermark survives an attack. Researchers now focus on three main factors: Attack Success Rate (ASR), perceptual quality, and forensic stealthiness [3].
- ASR measures how often a watermark is successfully removed.
- Perceptual quality determines whether the attack noticeably degrades the image or text.
- Forensic stealthiness evaluates whether the removal process leaves behind detectable traces or statistical anomalies.
To ensure reliable detection, researchers use metrics like True Positive Rate at a fixed False Positive Rate (TPR@0.1% FPR), which provides high statistical confidence [2][3]. For images, evaluations extend beyond traditional pixel-level metrics like PSNR to include LPIPS (perceptual similarity) and FID (how closely the image resembles natural ones) [3]. A successful detection typically requires a p-value below $10^{-6}$ [3].
"Any complete assessment of watermark removal must jointly consider three criteria: (i) attack success rate, (ii) perceptual quality, and (iii) forensic stealthiness."
– Gautier Evennou and Ewa Kijak [3]
Modern forensic tools are highly effective, with some achieving a True Positive Rate of over 80% at a $10^{-3}$ False Positive Rate for methods like WMForger [3]. This means that even if a watermark is removed, traces of tampering can often still be detected, a critical feature for enterprise-level content protection. These metrics provide a foundation for comparing different watermarking techniques.
Performance Comparison Table
Watermarking methods vary significantly in their ability to resist adversarial attacks. For instance, StegaStamp is known for its strong resilience across different scenarios, thanks to its training on distortions common in the physical world [2]. On the other hand, Tree-Ring watermarking is highly vulnerable to adversarial attacks, which can nearly eliminate its detection capability with minimal image manipulation [2].
In text-based watermarking, KGW-WM (which employs green-list/red-list logic) generally performs better than Unigram-WM, which can suffer detection accuracy drops of over 95% when subjected to text perturbations [6]. Among image watermarks, SSL-WM showed a relatively stable performance, with a 72.92% drop in detection accuracy under stress tests, while DctDwtSvd-WM experienced a significantly higher drop of 87.32% [6].
| Watermarking Method | Best Robustness Against | Primary Vulnerability | Detection Accuracy Drop |
|---|---|---|---|
| StegaStamp | Physical-world distortions, general attacks | High computational overhead | Minimal across tests [2][6] |
| Tree-Ring | Geometric shifts (crops, rotations, flips) | Adversarial attacks (surrogate detectors) | Nearly 100% under adversarial attacks [2] |
| Stable Signature | Standard image distortions | Regeneration/Rinsing (VAE/Diffusion models) | 63–81% depending on model [6] |
| MBRS | JPEG compression, adversarial attacks | Resized-cropping, blurring, rotation | Moderate [2] |
| SSL-WM | Image perturbations | Heavy distortion attacks | 72.92% [6] |
| RivaGAN-WM | General image attacks | Intense perturbations | 76.26% [6] |
The findings highlight that regeneration attacks – which process images through alternative VAEs or diffusion models – are especially effective against methods like Stable Signature [2]. Among image-based attacks, Zoom Blur consistently has the most significant impact on watermark removal, while Glass Blur tends to cause the least damage [6].
For businesses that need invisible watermarking with strong resistance to adversarial attacks, solutions like Tectus from InCyan stand out. These methods deliver reliable proof of ownership without compromising the user experience, making them ideal for enterprise applications.
Applications for Content Protection
Multi-Layer Defense Strategies
Enterprises are now stepping up their content protection game by using multi-layered defense systems. These strategies combine watermarking with forensic analysis to make it harder for attackers to remove watermarks successfully. One effective method involves a two-step verification: first, a detector checks for the watermark’s presence. If it’s missing, a forensic detector steps in to analyze the content for any statistical anomalies. Back in April 2026, researchers Gautier Evennou (IMATAG) and Ewa Kijak (IRISA/Université de Rennes) showcased this approach. They used a ConvNextTiny-v2 backbone on 5,000 COCO images watermarked with VideoSeal and TrustMark. Even though advanced attacks like WMForger and DiffPure managed to strip visible watermarks, the forensic layer still identified these removal attempts with an impressive true positive rate of up to 99.8% [3].
"Until an attack can pass both the watermark detector and the forensic detector, watermark removal remains an incomplete threat." – Gautier Evennou and Ewa Kijak, IMATAG and IRISA [3]
The forensic layer works by leveraging the trade-off between removing watermarks and the resulting quality degradation that becomes detectable. This layer can identify removal attempts with up to 99.8% accuracy [3], while maintaining an 80% success rate at a very low false positive rate of 0.1%. This makes it an excellent tool for monitoring high-profile accounts. Another advantage? These forensic layers can integrate with existing or even closed-source watermarking systems. By keeping model weights private and limiting API access, organizations can reduce the risk of adaptive attacks [3]. Together, these layers create a scalable and efficient solution for enterprise-level content protection.
Enterprise Protection Tools
Expanding on these defense strategies, enterprises are now using specialized tools to ensure comprehensive content protection. For example, InCyan’s Tectus offers invisible watermarking that embeds ownership proofs into media without affecting the user experience. Unlike visible watermarks – which can be cropped or removed – Tectus provides a hidden, durable ownership trail that simplifies copyright enforcement.
If visible watermarks fail, InCyan’s Idem steps in as a robust second line of defense. This AI-powered platform is designed to handle extreme transformations, including cropping, compression, memes, and mobile edits. It can identify ownership even if only 10% of the original content remains intact. To complement these tools, Blueprint integrates seamlessly with InCyan’s suite, offering precise control over rights and royalties while centralizing asset security.
For enterprises looking to solidify ownership claims, ScoreDetect adds another layer of protection through blockchain timestamping. By recording a checksum of the content on the blockchain, ScoreDetect creates an unchangeable record of ownership. This feature is particularly valuable for content creators, legal professionals, and media companies that need clear and verifiable provenance.
Conclusion
No watermarking method is immune to every type of attack. Each approach has its own weaknesses. For instance, StegaStamp performs well against physical-world distortions but falters under adversarial conditions. On the other hand, Tree-Ring struggles when faced with adversarial attacks. Meanwhile, Stable Signature works seamlessly within generative processes but fails against regeneration attacks that exploit alternative VAEs [2]. These results highlight the importance of adopting multi-layered defenses.
"Watermark-based AI-generated image detector based on existing watermarking methods is not robust to evasion attacks even if the attacker does not have access to the watermarking model nor the detection API." – Yuepeng Hu, Researcher, arXiv [1]
New AI watermarking technologies are emerging to address these challenges. For example, methods like ZoDiac are achieving detection rates above 98% while keeping false positives under 6.4% [9]. These advanced techniques embed watermarks directly into the latent space of diffusion models, rather than applying them in post-processing. This approach uses the same generative AI technology leveraged by attackers, effectively turning it into a defensive tool.
Based on the benchmarking results, organizations need to choose solutions tailored to their specific threat scenarios. If your content is likely to face heavy distortion or physical reproduction, StegaStamp is a strong choice. For environments prone to adversarial attacks, Tree-Ring may not suffice – combining multiple methods could be more effective [2]. Options like InCyan’s Tectus provide invisible watermarking that withstands extreme transformations, while ScoreDetect’s blockchain timestamping ensures ownership verification.
As attacks become increasingly advanced – ranging from basic cropping to sophisticated multi-diffusion and surrogate model techniques – the industry is stepping up with standardized benchmarking tools like WAVES. These frameworks test watermarks against 26 different attack scenarios [7][8], giving organizations the insight they need to select defenses that can endure real-world challenges.
FAQs
Which attacks are most likely to break my watermark?
When it comes to compromising watermarks, advanced adversarial and diffusive techniques pose the greatest challenge. These methods include high-level attacks that target weaknesses in detection algorithms, alongside more traditional forms of image manipulation.
Adversarial attacks are especially alarming. They work by making subtle changes to content that are nearly impossible to notice visually but are designed to evade detection systems. This makes them a sneaky and effective tool for bypassing watermark protections.
To stay ahead of these evolving threats, it’s crucial to prioritize regular benchmarking and updates. By consistently testing and improving your systems, you can build stronger defenses against these sophisticated attacks.
What metrics best measure watermark resilience in practice?
The best way to measure watermark resilience is by testing how well it holds up under distortions and attacks while still being detectable. Two key elements to focus on are:
- Image Quality Degradation: How much the watermark impacts the overall quality of the image.
- Detection Success Rate: Whether the watermark can still be identified after undergoing stress tests like adversarial attacks or diffusive changes.
Protocols such as WAVES provide a reliable way to assess this. They evaluate resilience by balancing the strength of the attack against the accuracy of detection, giving a clear picture of how the watermark performs in challenging, real-world scenarios.
How can I combine watermarking with forensics and blockchain proof?
Combining watermarking with forensics and blockchain proof involves embedding an invisible and non-intrusive watermark into digital media – whether it’s an image, video, or audio file. This watermark acts as a unique fingerprint, enabling forensic tools to trace unauthorized usage or detect tampering. When paired with blockchain, the watermark is linked to an immutable ledger, creating a secure and verifiable record of ownership and content history. This approach strengthens authentication and helps guard against piracy or alterations.