A robust image watermarking algorithm ensures that the embedded watermark can withstand various changes – like compression, cropping, resizing, and even deliberate removal – while remaining invisible and verifiable. Unlike metadata or visible logos, which can be easily stripped or altered, these watermarks stay embedded within the image itself. This makes them essential for copyright protection and ownership verification.
Key points to know:
- Definition of Robustness: The watermark should survive both unintentional distortions (e.g., compression) and deliberate attacks (e.g., geometric transformations) while remaining detectable.
- Challenges: Watermarks face threats like lossy compression, noise addition, cropping, scaling, and even AI-based edits.
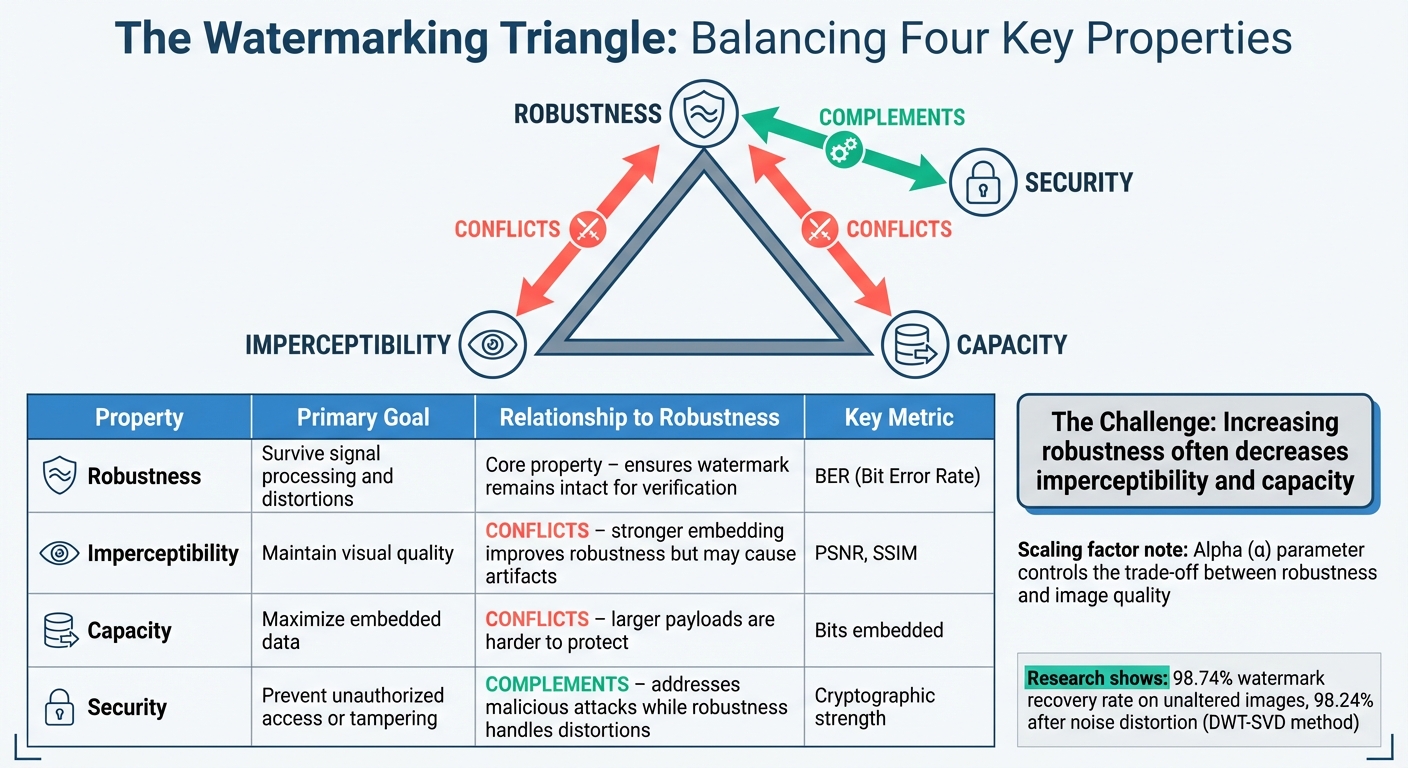
- Balancing Factors: Robustness often competes with imperceptibility (image quality) and capacity (amount of embedded data).
- Techniques: Common methods include transform-domain techniques (DCT, DWT, SVD), perceptual modeling, and deep learning in watermark detection.
- Testing: Robustness is measured using metrics like PSNR, SSIM, and BER, alongside simulations of real-world distortions.
Watermarking solutions must strike a balance between durability, invisibility, and data capacity to effectively protect digital content across platforms and use cases.
DIP Lecture 21: Digital watermarking
sbb-itb-738ac1e
What Robustness Means in Image Watermarking
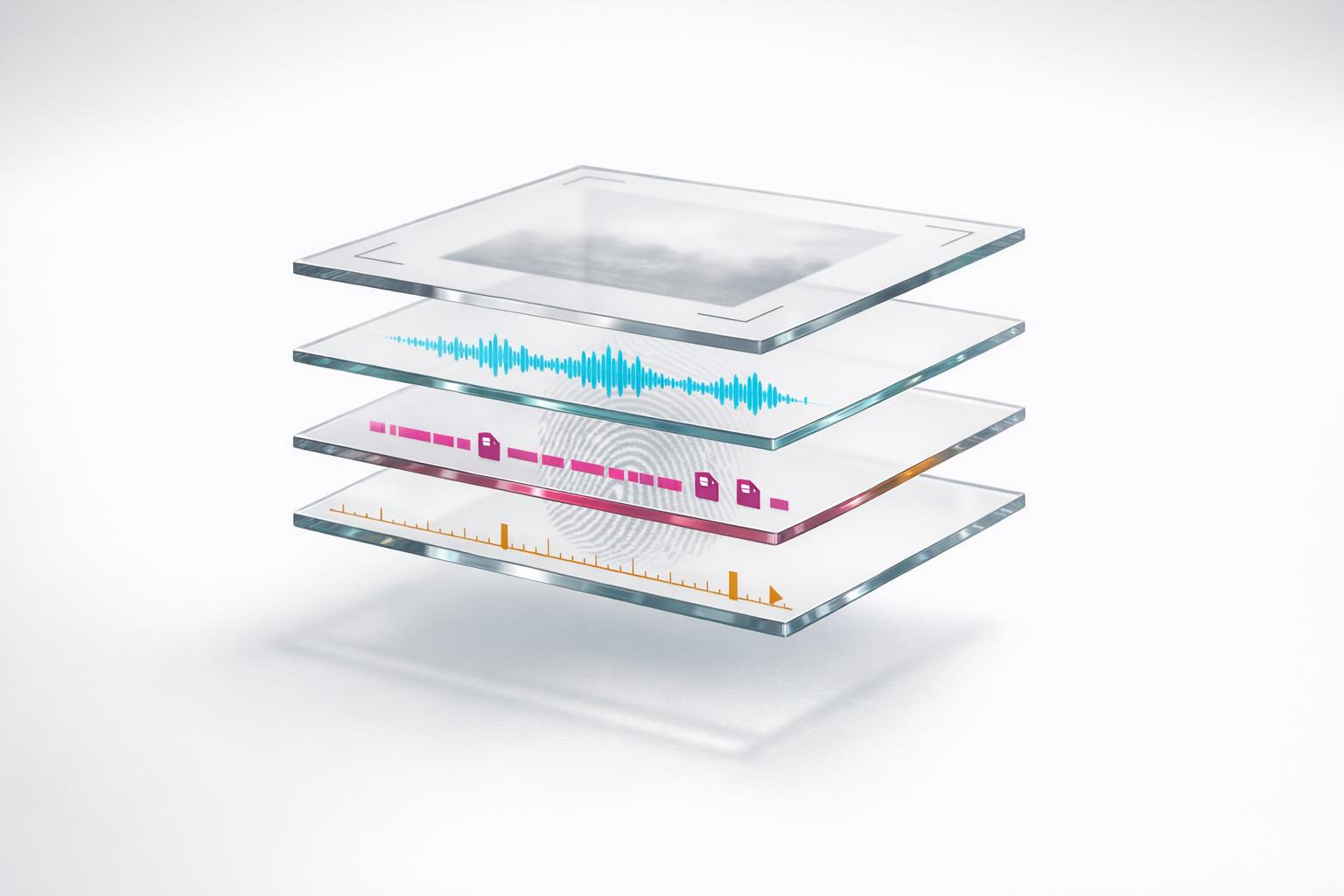
Watermarking Properties Comparison: Robustness vs Imperceptibility, Capacity, and Security
Definition of Robustness
Robustness refers to a watermark’s ability to withstand both intentional attacks and unintentional distortions while remaining detectable and verifiable [3][6]. Essentially, even if the image is subjected to signal distortions, the watermark should either stay intact or be easily recoverable [6].
Think of it as a hidden serial number embedded directly into the image. Unlike metadata, which can easily be stripped away during file conversions, a robust watermark stays embedded within the content itself. Harsh K Verma, Abhishek Narain Singh, and Raman Kumar describe it this way:
"the watermark must either remain intact or be easily modified in the face of signal distortions such as filtering, compression, cropping and re-sampling performed on the watermarked data" [6].
In real-world uses like copyright protection or verifying ownership, robustness is critical. The watermark must remain recoverable even if the image undergoes moderate alterations [6][8]. For instance, experiments with DWT-SVD watermarking demonstrated robust performance, achieving a 98.74% success rate for unaltered images and maintaining 98.24% accuracy after salt-and-pepper noise distortions [7]. Some methods can even achieve perfect recovery (Normalized Correlation of 1.0) when dealing with low-variance speckle noise [8].
Next, let’s see how robustness interacts with other important watermarking properties.
Robustness vs. Other Watermarking Properties
Robustness works alongside three key attributes: imperceptibility (invisibility), capacity (amount of data embedded), and security (protection against unauthorized tampering) [3]. However, these properties often compete with one another.
- Imperceptibility ensures the watermark doesn’t interfere with the image’s visual quality, keeping it aesthetically pleasing and commercially viable. But boosting robustness often reduces imperceptibility, as stronger embedding can introduce visible distortions [7][8]. This balance is managed using a "scaling factor" (alpha) – higher values improve robustness but can make the watermark noticeable.
- Capacity refers to how much data can be embedded, like ownership details or timestamps. Larger payloads tend to weaken robustness, as they make the watermark more susceptible to damage [4]. Most systems limit payload sizes to a few hundred bits to maintain a balance.
- Security focuses on preventing attackers from extracting or altering the watermark, even if they know the algorithm but lack the secret key [3]. While robustness deals with surviving signal distortions, security addresses cryptographic threats. For example, a watermark might resist JPEG compression but still be vulnerable to deliberate removal if its security measures are inadequate.
Here’s a quick comparison of these attributes and their relationship to robustness:
| Property | Primary Goal | Relationship to Robustness |
|---|---|---|
| Robustness | Survive signal processing and distortions | Ensures the watermark remains intact for verification |
| Imperceptibility | Maintain visual quality | Conflicts – stronger embedding improves robustness but may cause artifacts |
| Capacity | Maximize embedded data | Conflicts – larger payloads are harder to protect |
| Security | Prevent unauthorized access or tampering | Complements robustness – addresses malicious attacks |
Types of Attacks That Test Watermark Robustness
For watermarking to be effective, it must endure a variety of deliberate and incidental attacks. These attacks can come from those trying to remove watermarks intentionally or from routine image processing. Broadly, these threats fall into three main categories.
Signal Processing Attacks
Signal processing attacks directly alter the image’s pixel or sample data to weaken or remove the watermark. As noted in the Journal of Applied Research and Technology:
"Signal processing operators are applied to watermarked images for removing the watermark or decreasing its energy so that the extracted watermark is unrecognizable or insufficient as the validate evidence" [1].
Some common methods include:
- Lossy compression (e.g., JPEG, JPEG2000): These formats discard data, often targeting areas where watermarks are embedded.
- Filtering operations: Techniques like sharpening, low-pass filtering, and noise reduction smooth out the pixel-level changes that encode the watermark.
- Noise addition: Random noise, such as Gaussian or salt-and-pepper, can obscure the watermark signal, making it harder to detect.
Other threats include brightness or contrast adjustments, histogram equalization, and format conversions, all of which can degrade or distort the watermark. Compression, resampling, and filtering are particularly effective at erasing subtle changes embedded in the sample data.
Interestingly, embedding watermarks in the transform domain (e.g., using DCT or DWT methods) offers better resistance. These techniques align with how compression algorithms handle frequency coefficients. For instance, research indicates that visual attention-based watermarking can improve resilience to JPEG2000 compression by 25% and filtering attacks by 40% [2].
Next, let’s look at attacks that disrupt the spatial organization of the image, challenging the watermark’s positional stability.
Geometric Attacks
Geometric attacks don’t destroy the watermark but instead alter its location within the image. Operations like cropping, scaling, rotation, or aspect ratio changes disrupt the alignment between the embedded watermark and its detection mechanism [4]. As Hai Tao and colleagues explain:
"Geometric attacks induce synchronization errors between the original and the extracted watermark during the detection process. In other words, the watermark still exists in the watermarked image, but its positions have been changed" [1].
To counter these challenges, advanced algorithms employ transform domain methods like DWT, which breaks down signals into scales and orientations, making recovery easier after transformations [4]. Another approach relies on embedding watermarks in "geometric invariant regions" – areas of the image that remain stable even after resizing or rotation [3]. Additionally, deep learning models are being trained to locate embedding zones that naturally resist geometric distortions [5].
These strategies aim to ensure watermarks remain detectable, even when the image undergoes significant spatial changes.
Content Modification and Camera-Based Attacks
Beyond pixel and geometric manipulations, watermarking also faces threats from content edits and analog capture processes. Content modification attacks involve techniques like inpainting, style transfer, or overlaying stickers and other elements [4]. Camera-based attacks, on the other hand, occur when someone photographs a watermarked image on a screen or prints and rescans it [4].
AI-powered modifications present a unique challenge, as they often replicate the image’s structure while erasing the specific pixel-level watermark data. As InCyan notes:
"In many cases, the output is a new work that borrows structure from the input but does not preserve pixel or sample identity" [4].
Camera-based attacks introduce a mix of distortions, including noise, perspective changes, color adjustments, and even halftoning in printed images. Some attackers might even use generative AI models to replace watermarked content with synthetic data [4]. To combat these evolving threats, the industry is increasingly adopting blind detection methods. These techniques can identify watermarks without needing the original unmarked file using AI tools for piracy detection, making them vital for verifying content shared on platforms like social media [4].
Below is a summary of how different attack types impact watermark integrity:
| Attack Category | Specific Examples | Impact on Watermark |
|---|---|---|
| Compression | JPEG, JPEG2000 | Removes high-frequency data and quantizes coefficients |
| Filtering | Sharpening, Low-pass filtering | Alters edges and textures where watermarks are embedded |
| Noise | Gaussian, Salt-and-pepper | Masks the watermark signal with random data |
| Enhancement | Contrast adjustment, Histogram equalization | Alters pixel intensity and color values |
Technical Methods for Building Robust Watermarks
Creating a watermark that can survive various attacks – like compression, cropping, or AI-based alterations – requires more than just embedding data into an image. The technical approach plays a critical role in ensuring the watermark remains intact. Here, we’ll dive into three key strategies that have proven effective.
Transform Domain Methods
Instead of embedding watermarks directly into pixel values, transform domain methods work with an image’s mathematical representation. This approach often provides better resilience against common modifications.
- Discrete Cosine Transform (DCT): This method breaks an image into frequency components – low, mid, and high frequencies. By embedding watermarks into the preserved frequency coefficients, DCT is particularly effective against JPEG compression.
- Discrete Wavelet Transform (DWT): DWT decomposes images into multiple scales and orientations, making it robust against scaling, cropping, and JPEG2000 compression. Even when an image is resized or cropped, the wavelet coefficients adjust proportionally, keeping the watermark intact.
- Singular Value Decomposition (SVD): SVD leverages the stability of singular values, which remain relatively unchanged when small distortions are applied. This makes it effective against geometric attacks.
Modern systems often combine these techniques, like DWT-SVD or DFT-DCT, to maximize their strengths. For example, wavelets offer multi-resolution benefits, while SVD provides mathematical stability. The table below highlights how these methods perform:
| Technique | Primary Domain | Best Resistance Against | Main Weakness |
|---|---|---|---|
| DCT | Frequency | JPEG Compression, Noise | Geometric Distortions (Rotation) |
| DWT | Multi-resolution | Scaling, Cropping, JPEG2000 | Shift Sensitivity |
| SVD | Mathematical | Geometric Attacks, Perturbations | Computational Complexity |
| LSB | Spatial | None (High Capacity only) | Extremely fragile to any change |
Perceptual Modeling Techniques
Perceptual modeling takes advantage of how the human visual system works, embedding watermarks in ways that are less noticeable to viewers.
- Just Noticeable Difference (JND): This model identifies areas of an image that can tolerate slight modifications without becoming visually apparent. Textured regions, like foliage or fabric, can hide more watermark data compared to smooth areas like skies.
- Visual Saliency: This method maps where viewers naturally focus their attention. In 2016, researchers from the University of Sheffield demonstrated a visual attention-based watermarking approach. By embedding weaker watermarks in visually prominent regions and stronger ones in less noticeable areas, they achieved a 25% improvement in robustness against JPEG2000 compression and a 40% improvement against filtering attacks [2]. As they explained:
"If distortion due to high strength watermarking can avoid visually attentive regions, such distortions are unlikely to be noticeable to any viewer" [2].
- Gradient-Based Adaptation: This technique measures local pixel complexity. High-gradient areas, which contain more detail, can accommodate more watermark data without degrading the image’s appearance.
Deep Learning Approaches
Modern neural networks have revolutionized watermarking by identifying robust embedding spaces that resist distortions more effectively than traditional methods.
- Convolutional Neural Networks (CNNs): These networks extract high-level features and local textures, making them highly resistant to distortions. Encoder-decoder models often include noise layers during training, simulating real-world transformations.
- Hybrid Systems: In February 2026, researchers introduced a hybrid zero-watermarking system that combined features from the CONV5-4 layer of the VGG19 neural network with Local Binary Patterns (LBP). By integrating chaotic encryption methods, this system achieved near-perfect robustness, with a Normalized Cross-Correlation (NCC) of 1.0 and a Bit Error Rate (BER) of 0 under various attacks [9].
- Generative Adversarial Networks (GANs): GANs, along with UNet architectures, enable invisible watermarks that can be extracted even after the content has been used to train AI models. For instance, Pang et al. developed a GAN-based method for embedding invisible watermarks into open-source datasets, allowing content owners to verify if their data was improperly used [9].
As noted by Nature Scientific Reports:
"Deep learning… enhances watermarking by extracting visual attributes and adaptively embedding them" [9].
These AI-driven techniques are becoming indispensable in protecting content in an era dominated by generative AI, as they can separate watermark signals from both natural and synthetic noise – even under aggressive transformations [4]. Up next, we’ll look at how to measure the robustness of these techniques.
How to Measure Watermark Robustness
Evaluating robustness ensures that a watermark can withstand various forms of tampering. This involves using specific metrics and conducting thorough testing.
Common Evaluation Metrics
Several key metrics are used to assess watermark robustness:
- Peak Signal-to-Noise Ratio (PSNR): This metric evaluates the distortion caused by embedding the watermark compared to the original image. Higher PSNR values mean less noticeable changes to the image [4].
- Structural Similarity Index (SSIM): Unlike PSNR, SSIM focuses on how changes affect the perceived quality of the image, making it a more accurate measure of visual impact [4].
- Bit Error Rate (BER): BER measures how accurately the watermark can be extracted after an attack by calculating the percentage of bits recovered incorrectly. A BER of 0 indicates perfect accuracy [4].
Other important metrics include extraction success rates and confidence scores, which confirm how reliably the system identifies watermarked content. Additionally, false positive and false negative rates help ensure the system avoids unnecessary alerts or misses genuine watermarks. Researchers from the University of Maryland highlight that in scenarios where false alarms are costly, measuring the True Positive Rate at a strict 0.1% False Positive Rate gives a more realistic picture of performance [10].
These metrics lay the groundwork for the testing methods described below.
Testing Methods
Robustness testing involves simulating attacks that watermarked images might encounter. These attacks are typically grouped into four categories:
- Geometric changes: Includes transformations like cropping or rotation.
- Signal processing: Covers techniques such as JPEG compression or sharpening.
- Format conversion: Involves transcoding between different file formats or codecs.
- AI-based edits: Includes advanced manipulations like inpainting or style transfer [4].
Testing scenarios often vary by industry. For example, social media platforms introduce challenges like heavy compression and aspect ratio changes, while broadcast environments deal with repeated transcoding and rescaling [4]. Modern benchmarks, such as WAVES, test watermarks against up to 26 different attack types to ensure durability [10]. As Nikhil John from InCyan explains:
"A watermark that disappears after a single round of social media transcoding or minor colour correction does not help rights holders."[4]
To verify robustness, the process typically involves applying an attack, extracting the watermark from the altered asset, matching it against a database, and generating a confidence score [4]. However, achieving the right balance is critical. The "watermarking triangle" – comprising imperceptibility, robustness, and payload capacity – requires careful tuning. Increasing the watermark’s energy might improve its survival rate but could also degrade the image quality, so striking the right balance is key.
Conclusion
Main Points About Robustness
Robustness is all about whether a watermark can withstand the challenges of the digital content lifecycle. This includes everything from compression and resizing to deliberate tampering and AI-driven edits. The watermarking triangle highlights that robustness is always in a balancing act with imperceptibility and capacity [4].
A truly robust watermark can survive unintentional processes like JPEG compression, creative modifications such as color adjustments, and even deliberate attacks like cropping, aggressive filtering, or AI-generated edits [4]. As Nikhil John from InCyan puts it:
"Properly designed invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state" [4].
To evaluate robustness, technical metrics like PSNR, SSIM, and BER are used alongside practical tests, such as how the watermark holds up after social media compression or broadcast scaling [4]. These principles are the backbone of modern digital watermarking solutions.
How ScoreDetect Provides Robust Watermarking

ScoreDetect takes these robustness principles and turns them into a powerful digital content protection tool. Its Enterprise plan introduces invisible, AI-powered watermarking that embeds machine-readable signals into images, videos, and audio. These signals function as a hidden serial number that remains intact through processes like metadata removal and file re-exporting [4]. By using AI to separate watermark signals from both natural and synthetic noise, ScoreDetect ensures detection even after intense transformations like inpainting or style transfer.
On top of that, ScoreDetect employs blockchain technology to create a tamper-proof chain of custody. By capturing cryptographic checksums without storing the actual files, it provides legally sound proof of ownership. With features like automated workflows via Zapier and a WordPress plugin, ScoreDetect delivers a full-scale solution for industries ranging from media and entertainment to legal services and e-commerce, ensuring robust and scalable content protection.
FAQs
How do I choose the right robustness vs. invisibility tradeoff?
Choosing the right balance means recognizing the tradeoff: stronger embedding boosts resilience but can lead to noticeable distortions, while weaker embedding maintains image quality but sacrifices durability. Adaptive techniques offer a solution by tailoring the embedding strength to the image’s content and potential threats. In the end, your decision should align with your goals – whether you value visual appeal or prioritize security and copyright protection for your particular use case.
What edits break most watermarks in real-world sharing?
Watermarks can easily be disrupted by common edits such as compression (e.g., saving an image as a JPEG), cropping, resizing, adding noise, or applying filters. These alterations often degrade or completely erase the embedded watermark while still preserving the overall visual appearance of the image. This makes it difficult for watermarks to survive the various transformations images undergo during everyday sharing.
How is watermark robustness proven in testing?
Watermark robustness is evaluated by testing how well it holds up against different modifications like adding noise, applying compression, or using filters. After these deliberate or accidental changes, the watermark’s ability to be detected and its integrity are checked to confirm it stays intact and usable.