Frequency domain watermarking embeds hidden data into an image’s frequency components, making it invisible to the human eye and resistant to tampering. Unlike methods that modify individual pixels, this technique uses transformations like DCT, DFT, or DWT to distribute the watermark across the image, ensuring durability against compression, noise, and other manipulations.
Key Takeaways:
- How it works: Converts images into frequency components, embeds watermarks in specific coefficients (like mid-frequency bands), and ensures they remain intact even after compression or cropping.
- Why it matters: Essential for copyright protection, identity verification, and tracking image usage, especially in the age of AI and digital piracy.
- Benefits: Resistant to removal without damaging the image, imperceptible to users, and effective even under attacks by AI models.
Example:
In 2024, researchers developed FreqMark, a system embedding 48-bit watermarks with over 90% accuracy, proving effective against compression, cropping, and even AI-driven regeneration attacks.
This technique is widely used in industries like media, e-commerce, and healthcare to protect digital assets and authenticate digital images.
DIP Lecture 21: Digital watermarking
sbb-itb-738ac1e
How Frequency Domain Watermarking Works
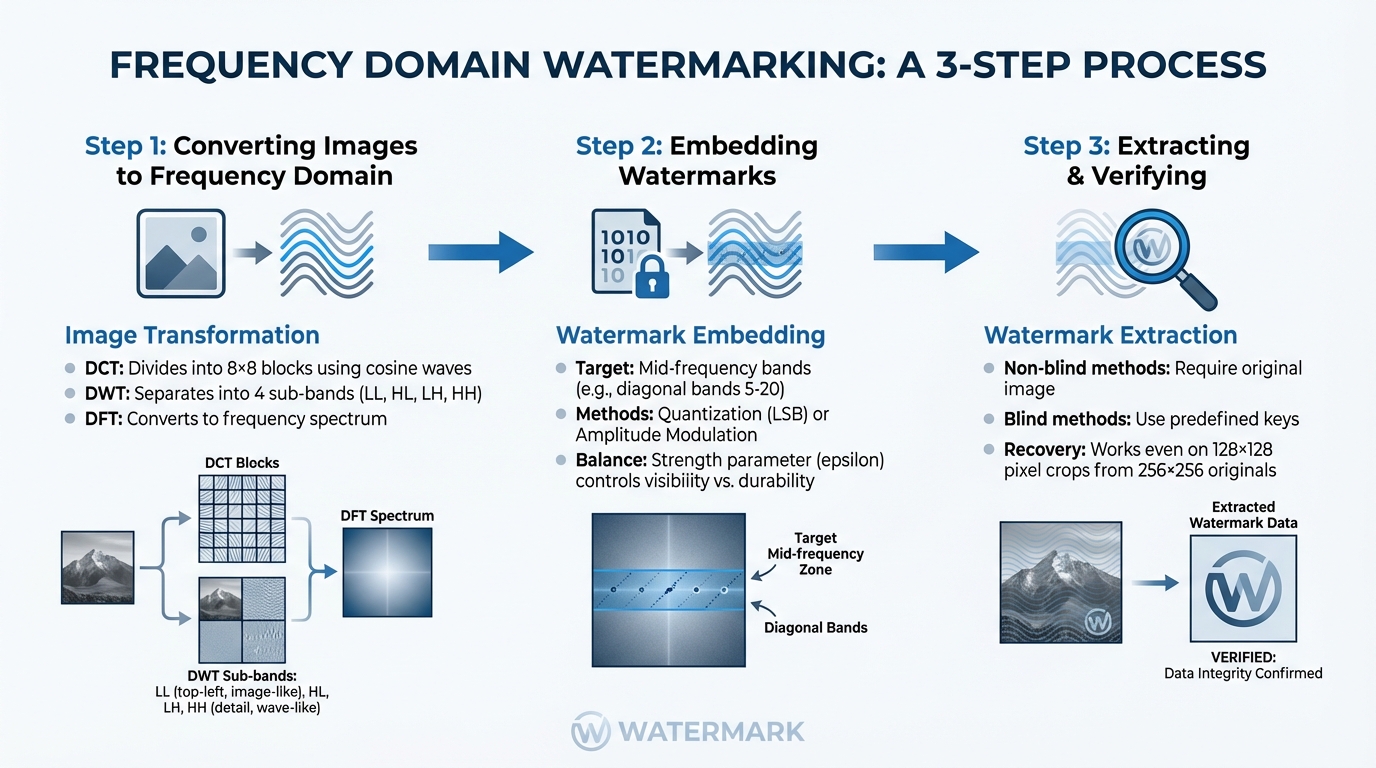
How Frequency Domain Watermarking Works: 3-Step Process
Converting Images to the Frequency Domain
The first step in frequency domain watermarking is converting an image from its spatial representation to the frequency domain. This is achieved using algorithms like Discrete Cosine Transform (DCT), Discrete Fourier Transform (DFT), or Discrete Wavelet Transform (DWT). These methods break an image into frequency components, providing a mathematical framework for embedding watermarks.
- DCT: Divides the image into 8×8 blocks and represents each block as a summation of cosine waves at varying frequencies.
- DWT: Separates the image into low- and high-frequency components through horizontal and vertical operations. This results in four sub-bands: LL, HL, LH, and HH, with the LL sub-band holding the most critical visual information.
- DFT: Converts the entire image into its frequency spectrum, emphasizing amplitudes and phases.
"Frequency Domain Techniques are operated on frequency of an image… where $f_i$ is the original image, $I_i$ is the modified image after applying frequency transformation $f_p$, $g_i$ is the final modified image after implementing inverse transformation $-f_p$." – Tanmoy Sarkar and Sugata Sanyal [4]
Once the image is represented in frequencies, specific coefficients are targeted for embedding the watermark.
Embedding Watermarks in Frequency Coefficients
With the image transformed, the watermark is embedded into chosen frequency coefficients. Mid-frequency bands are ideal for this process (e.g., diagonal bands 5–20 in DCT). Low-frequency components are too visually sensitive, while high-frequency ones are often lost during JPEG compression.
Watermarking techniques include:
- Quantization: Coefficients are divided by a strength parameter, rounded, and the watermark bit is embedded in the Least Significant Bit (LSB) of the quantized value [5].
- Amplitude Modulation: Adjusts the amplitudes of the frequency spectrum using a symmetrical watermark function. For DFT-based watermarking, Hermite symmetry ($f(x,y)=f^*(-x,-y)$) is required to avoid unwanted imaginary components [2].
The strength parameter (epsilon) plays a critical role. A higher strength improves resistance to attacks like cropping or rotation but increases the risk of visible artifacts. To balance invisibility and durability, the optimal strength is determined by testing the point where artifacts are minimized, and the watermark remains intact [2].
Extracting and Verifying Watermarks
The embedding process is designed to allow robust extraction, providing effective digital piracy solutions with watermarking even after an image has been altered. Extraction reverses the embedding steps, transforming the watermarked image back into the frequency domain with the same technique (DCT, DFT, or DWT). The frequency coefficients are then analyzed to retrieve the hidden watermark.
Two main extraction methods are used:
- Non-blind methods: Require access to the original image.
- Blind methods: Depend on predefined keys [2] [3]. For example, the FreqMark system uses blind extraction by calculating the signs of dot products between image features and predefined direction vectors [1].
Verification ensures the watermark is authentic and intact. If the image has undergone geometric changes, such as rotation or scaling, these transformations must be reversed before extraction. Impressively, watermarks can remain detectable even in cropped subregions. For instance, a watermark embedded in a 256×256 pixel image can still be recovered from a 128×128 pixel subregion [2].
Benefits of Frequency Domain Watermarking
Resistance to Compression and Noise
One of the standout features of frequency domain watermarking is its ability to resist compression and noise. By embedding watermarks in mid-frequency coefficients, this method ensures that the watermark survives compression processes like JPEG, which typically discard high-frequency data but retain mid-frequency components.
For instance, FreqMark demonstrates over 90% bit accuracy for a 48-bit watermark, even when subjected to compression, rotation, and cropping attacks [1]. It also holds up against advanced regeneration attacks, where AI models attempt to denoise or recreate images to strip watermarks. With a decoding threshold of 39 bits, the False Positive Rate for a 48-bit watermark drops to around 1.65 × 10⁻⁶ [1].
"Introducing perturbations to watermark images in the latent and frequency domains offers distinct advantages… achieving a synergistic effect where the whole is greater than the sum of its parts." – Yiyang Guo et al. [1]
This ability to resist such attacks goes hand in hand with maintaining an imperceptible watermark, which is explored further below.
Invisible Watermarks That Preserve Image Quality
Another key benefit is the ability to embed watermarks without compromising the visual quality of the image. Unlike spatial domain techniques that alter specific pixels and may create visible distortions, frequency domain methods distribute changes across the entire image using mathematical transformations. This even distribution ensures that alterations remain hidden to the naked eye.
To achieve this, frequency domain watermarking relies on perceptual optimization metrics like PSNR (Peak Signal-to-Noise Ratio) and LPIPS (Learned Perceptual Image Patch Similarity), ensuring modifications are imperceptible [1]. By modulating amplitudes instead of phases, the technique allows for significant watermark embedding without introducing noticeable artifacts [2].
"Perturbations in the frequency domain are more concealed than those in the pixel space, making them harder to eliminate and thus offering superior robustness against regeneration attacks while minimizing the impact on image quality." – Yiyang Guo et al. [1]
Difficult to Remove Without Damaging the Image
Perhaps one of the most compelling aspects of frequency domain watermarking is how difficult it is to remove a watermark without degrading the image. Since the watermark is embedded within the essential frequency coefficients that define the image’s structure, any attempt to remove it will likely harm the overall image quality.
"The use of the frequency domain-based techniques can not only keep the imperceptibility but also ensure good robustness and non-removability." – Kaixuan Zhang [3]
While spatial domain methods may offer a high degree of invisibility, they often lack durability. Frequency domain techniques, on the other hand, strike a balance by providing both invisibility and robustness, making them a reliable choice for safeguarding digital images against unauthorized use. These combined strengths position frequency domain watermarking as a powerful tool for digital content protection.
Where Frequency Domain Watermarking is Used
Protecting Content for Businesses and Creators
Frequency domain watermarking is a go-to method for businesses and creators to secure their digital assets and establish ownership. By embedding invisible watermarks into images, creators can track their work online and provide mathematical proof of ownership if someone uses their content without permission.
"By adding invisible watermarks within images, the concealed message can be tracked and used for purposes such as copyright verification, identity authentication, copy control, etc., thereby safeguarding against the misuse of image content." – Yiyang Guo et al., Researchers, University of Science and Technology of China / Tencent [1]
This technique has gained importance in distinguishing original images from AI-generated ones, addressing concerns like deepfakes and copyright violations linked to generative models. For instance, tools like Stable Diffusion rely on frequency domain methods (such as DwtDctSvd) to verify image authenticity [1].
These protections set the stage for advanced platforms that merge watermarking with AI-powered content management systems.
Using Advanced Tools Like ScoreDetect

Expanding on these capabilities, advanced tools integrate frequency domain watermarking with cutting-edge AI solutions. One standout example is ScoreDetect, which offers a comprehensive content protection system built around four steps: Prevent, Discover, Analyze, and Take Down.
ScoreDetect’s invisible watermarking technology ensures images remain protected without compromising quality. Paired with its intelligent web scraping – boasting a 95% success rate in bypassing prevention measures – and automated takedown notices with a 96% success rate, the platform provides full-spectrum protection. Additionally, it incorporates blockchain technology to create a checksum for each image, offering verifiable proof of ownership without needing to store the actual files.
For enterprise-level needs, InCyan, the parent company of ScoreDetect, offers tools like Tectus, a blind watermarking solution designed to provide invisible proof of ownership. This is especially effective against AI-driven piracy, where generative models attempt to strip watermarks through regeneration attacks.
Industry Examples
Frequency domain watermarking plays a critical role in industries where tracking ownership and ensuring authenticity are non-negotiable.
- Media and entertainment companies use it to protect copyrighted photos and videos from unauthorized distribution.
- Legal firms and military organizations rely on it to verify data integrity and detect tampering during transmission using watermark detection techniques [4].
"Some organizations like medicine, military are sharing data with are highly secretive and important… an approach of digital watermarking is used where authenticate multimedia data is embedded into original message." – Tanmoy Sarkar and Sugata Sanyal [4]
Other industries benefit as well:
- E-commerce platforms use it to safeguard product images, especially during JPEG compression, where frequency domain techniques excel [4].
- Marketing and advertising agencies apply it to manage brand assets and monitor ad placements across various channels.
- Healthcare providers depend on it to maintain the integrity of medical imaging.
- Real estate firms utilize it to protect property photos from unauthorized use.
In October 2024, researchers from the University of Science and Technology of China and Tencent’s IEG introduced FreqMark, a self-supervised watermarking method. This innovation achieved over 90% bit accuracy for 48-bit messages and resisted regeneration attacks by generative models. Led by Yiyang Guo and Ruizhe Li, the project highlighted how frequency domain techniques continue to adapt to new challenges in the digital world [1].
Conclusion
Frequency domain watermarking stands out as one of the most effective methods for safeguarding digital images against unauthorized use and combating digital piracy. By embedding data into spectral coefficients instead of individual pixels, this technique ensures that watermarks are nearly impossible to remove without visibly damaging the image. It strikes a balance between being unobtrusive and highly secure [3].
"The use of the frequency domain-based techniques can not only keep the imperceptibility but also ensure good robustness and non-removability." – Kaixuan Zhang [3]
This approach offers strong resistance to common image manipulations like JPEG compression, Gaussian noise, cropping, and rotation. Advanced implementations boast over 90% bit accuracy for 48-bit messages, with false positive rates as low as 5.04 × 10⁻⁸ [1]. This makes it possible to prove ownership without needing the original, unwatermarked image – perfect for copyright enforcement in practical scenarios.
The technical advantages of frequency domain watermarking translate into real-world solutions for protecting digital content. Tools like ScoreDetect simplify the complex algorithms behind frequency domain techniques, making them accessible to businesses across various industries. For more advanced protection, InCyan’s Tectus offers blind watermarking solutions powered by AI, ensuring digital assets remain secure.
Whether you’re securing e-commerce product images, protecting sensitive medical imaging, or safeguarding marketing visuals, frequency domain watermarking provides the durability and security needed to combat digital piracy. Emerging tools like FreqMark further enhance protection by combining frequency techniques with latent space optimization, addressing new challenges in content security [1].
FAQs
Which transform should I use – DCT, DWT, or DFT?
The article highlights the Discrete Fourier Transform (DFT) as the preferred method for frequency domain watermarking. Although other techniques like Discrete Cosine Transform (DCT) and Discrete Wavelet Transform (DWT) are mentioned in the broader discussion of digital watermarking, the emphasis remains on DFT. This is due to its effectiveness in embedding watermarks within the frequency domain. Among the approaches detailed, DFT emerges as the most widely used transformation.
How do I choose watermark strength without visible artifacts?
Balancing watermark robustness with visual quality is key to avoiding visible artifacts in images. Techniques like Discrete Wavelet Transform (DWT), Discrete Cosine Transform (DCT), or Singular Value Decomposition (SVD) are often used in the transform domain to achieve this. The trick lies in adjusting the coefficients with precision.
To ensure the watermarked image maintains high quality, evaluate it using metrics like Peak Signal-to-Noise Ratio (PSNR) – aim for values above 40 dB for minimal distortion – and Structural Similarity Index (SSIM). These metrics help quantify how closely the watermarked image resembles the original.
Robustness is another critical factor. Test the watermark’s durability by simulating real-world manipulations like compression or resizing. This helps you find the ideal balance where the watermark remains invisible yet resistant to potential attacks.
Can the watermark survive AI regeneration or heavy edits?
The strength of a frequency domain watermark against AI-driven regeneration or extensive edits hinges on the technique employed. Sophisticated methods, such as embedding within the image’s latent frequency space, aim to endure manipulations like cropping, compression, and added noise. While these advanced approaches improve durability, no method can fully withstand highly advanced attacks that drastically modify the frequency components.