Digital watermarks often fail when images undergo geometric transformations like rotation, scaling, or translation. These simple adjustments can desynchronize the watermark, making it undetectable. Here’s how each transformation disrupts watermarks and potential solutions:
- Rotation: Shifts watermark alignment. Fixes include Log-Polar Mapping (LPM) and template-based tracking.
- Scaling: Alters spatial frequency. Solutions involve multi-resolution frameworks and Fourier-Mellin Transform.
- Translation: Moves watermark coordinates. Embedding in the Fourier magnitude domain or using the Invariant Centroid method helps.
Blind detection systems, which lack access to the original image, are especially vulnerable to these attacks. Advanced techniques like transform domain methods, template-based resynchronization, and deep learning models offer ways to counteract these distortions. Each approach has trade-offs in terms of computational demands, resilience, and implementation complexity.
For a robust watermarking solution, combining frequency domain techniques with modern tools like AI can help ensure detection even after geometric transformations.
Digital Image Watermarking (DIW) in the wavelet transform domain robust to geometric transformation
sbb-itb-738ac1e
How Rotation, Scaling, and Translation Affect Watermarks
Geometric transformations can disrupt watermark detection by causing desynchronization. While the watermark signal stays embedded, spatial shifts make it impossible for detectors to locate. Transformations like rotation or scaling add another layer of complexity because they require interpolation, which can blur the watermark’s details and weaken the signal – even if the transformation is undone later [2][4]. Although frequency domain techniques like DFT, DCT, and DWT are strong against compression, they often falter when faced with geometric distortions.
"Even very small geometric distortions can prevent the detection of a watermark." – IEEE Transactions on Image Processing [1]
Geometric attacks are both simple and effective, making them a popular choice for bypassing watermark systems. Blind detection methods, in particular, face significant challenges since they cannot reference the original image for alignment. For example, aligning a 256×256 image in some registration algorithms can take as long as 16 minutes [4].
Below, we explore the unique challenges posed by rotation, scaling, and translation, along with potential solutions. These challenges are particularly relevant when protecting generative images from unauthorized manipulation.
Rotation: Problems and Fixes
When an image is rotated, the watermark’s embedding coordinates shift, throwing the watermark components out of their expected positions.
A proven method to counter this is Log-Polar Mapping (LPM), which simplifies rotation into a cyclic shift that can be detected more easily [1][2]. Another approach involves embedding a template alongside the watermark. This template acts as a guide, helping the detector identify the rotation angle and re-align the image before searching for the watermark.
Scaling: Problems and Fixes
Resizing an image affects the spatial frequency of the watermark. Since watermarks are embedded at specific resolutions, scaling can move the signal into a different frequency range, causing a mismatch during detection.
One effective countermeasure is a multi-resolution framework, which distributes the watermark across various resolution levels using techniques like wavelets or pyramid decompositions [2][3][4]. Another option is the Fourier-Mellin Transform, which creates invariant representations that remain stable even when scaling occurs [2][7]. A 2016 study demonstrated this by embedding a circular watermark vector in the Fourier magnitude domain, successfully addressing the subtle scaling variations seen in print-scan processes for ID images [8].
Translation: Problems and Fixes
Horizontal or vertical shifts displace the watermark from its original coordinates. Spatial-domain watermarks are particularly vulnerable, as even a single-pixel shift can disrupt detection. However, watermarks embedded in the Fourier Transform magnitude are naturally resistant to translation [1][3].
The Invariant Centroid (IC) technique provides a practical solution by using the grayscale image’s "gravity center" as a stable reference point for embedding [2]. Alternatively, embedding the watermark in the Fourier magnitude domain ensures that translation does not impact the detection process [1][8].
| Transformation | Primary Impact | Most Effective Solution |
|---|---|---|
| Rotation | Alters pixel orientation and distorts the grid | Log-Polar Mapping; template-based tracking |
| Scaling | Changes spatial frequency and resolution | Multi-resolution frameworks; Fourier-Mellin Transform |
| Translation | Displaces watermark from expected coordinates | Fourier magnitude domain; Invariant Centroid technique |
"Geometrical attacks easily desynchronize the watermark, degrading its robustness dramatically." – Journal on Advances in Signal Processing [3]
Methods for Building Watermarks That Resist Geometric Changes
Creating watermarks that can withstand rotation, scaling, and translation requires strategies that either establish invariant domains or use synchronization markers. Three primary approaches – transform domain methods, template-based resynchronization, and deep learning – offer distinct ways to tackle these challenges.
Transform Domain Methods
These methods embed watermarks in the frequency domain instead of directly in pixel data, making them more robust against geometric changes. A standout example is the Fourier-Mellin Transform (FMT), which combines the Discrete Fourier Transform (DFT) with Log-Polar Mapping (LPM). This combination shifts rotation into a cyclic pattern and scaling into a linear shift along the log-radius axis, simplifying the process of detecting and correcting geometric distortions [1][2].
"DFT is preferable to DCT when it comes to dealing with geometric manipulations such as cropping and translation." – ScienceDirect [2]
Another technique, the Discrete Wavelet Transform (DWT), provides multi-resolution analysis by capturing both spatial and frequency details. This makes it effective across different image scales, although it struggles with rotation and translation without additional resynchronization mechanisms [2][4].
For a more advanced solution, the Deformable Pyramid Transform (DPT) builds on the Steerable Pyramid Transform, offering shift-invariance, steerability, and scalability. Using Fourier magnitude as input, DPT separates translation effects from rotation and scaling, enhancing its robustness [3].
Additionally, improved Fourier-Mellin methods now achieve RST (rotation, scaling, translation) invariance with just one 2-D DFT, cutting down computational demands significantly [2].
Template-Based Resynchronization
Template-based approaches embed an auxiliary "pilot signal" alongside the watermark. This signal serves as a geometric anchor, helping to detect rotation angles, scaling factors, and translation offsets. These templates appear as local peaks in the DFT magnitude domain, guiding the watermark’s realignment [2][3].
"Template matching-based watermarking is a method that embeds additional information for correcting geometrical distortions, i.e., a template at 2-D DFT magnitude as the local peaks along with watermark. By finding the positions of the template, the geometrical distortion can be corrected and the watermark extracted." – Real-Time Imaging Journal [2]
Once the detector identifies the template peaks, it calculates the necessary inverse transformation to realign the image and extract the watermark. This method is especially useful in blind detection scenarios, where the original image is unavailable for comparison.
However, templates can be prone to damage from interpolation or blurring during attacks. Embedding templates in middle-frequency bands of the DFT domain can improve their resilience against common processes like JPEG compression [2][3].
Deep Learning Methods
Machine learning introduces a modern twist, with AI improving watermarking accuracy by training models to recognize identifiers even after complex geometric deformations. Convolutional Neural Networks (CNNs) excel at identifying watermarks subjected to random bending or combined RST transformations [2][9].
Another approach involves Support Vector Machines (SVMs), which analyze patterns like Zernike moments or embedded templates to predict geometric distortion parameters. By training on large datasets, these models can detect subtle patterns that traditional methods might overlook [3].
Feature-based strategies, such as those using Scale-Invariant Feature Transform (SIFT) keypoints, bind watermarks to prominent image features. These features are naturally resistant to RST changes, making them an effective alternative. Rather than fighting geometric transformations, this method leverages the image’s structure to maintain watermark integrity [6].
| Method | Primary Mechanism | Best Use Case | Main Limitation |
|---|---|---|---|
| Fourier-Mellin (FMT) | Converts RST to shifts in frequency domain | Global transformations on full images | High computational cost; interpolation errors [2] |
| Template-Based (TMW) | Embedded anchor points for realignment | Blind detection without original image | Templates can be destroyed by blurring [2] |
| Deep Learning (CNN/SVM) | Learned features resistant to deformation | Complex or combined geometric attacks | Requires extensive training data [3][9] |
| Feature-Based (SIFT) | Binds to natural image keypoints | Images with strong feature points | Fails on uniform or textureless regions [6] |
"Counteracting geometrical attacks remains one of the most challenging problems in robust watermarking." – EURASIP Journal on Advances in Signal Processing [3]
These approaches provide a range of tools for addressing geometric distortions, each with its strengths and weaknesses. Together, they offer a foundation for evaluating watermark resilience against such attacks.
Comparing Watermarking Methods Against Geometric Attacks
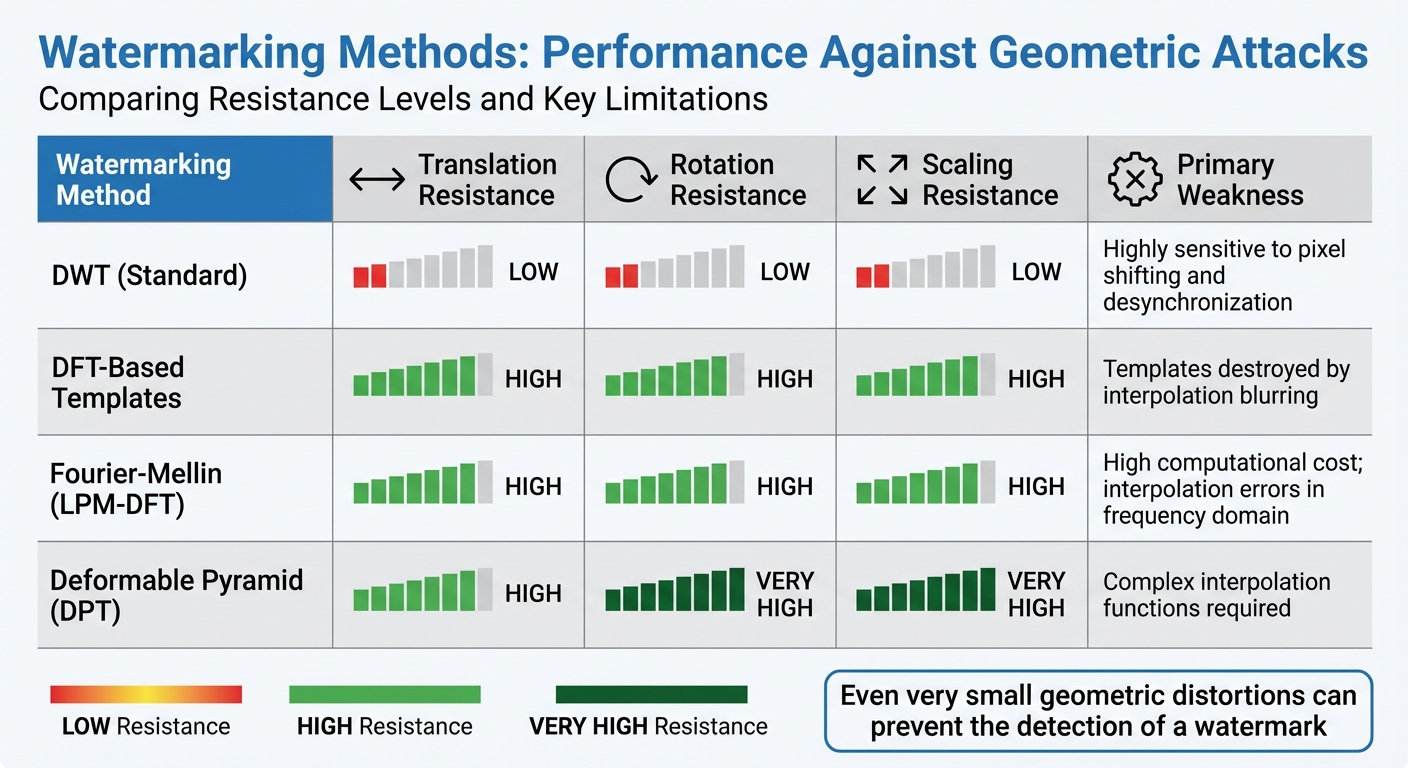
Watermarking Methods Comparison: Resistance to Geometric Attacks
When evaluating digital piracy solutions with watermarking, it’s essential to understand how well each method holds up against geometric attacks. Real-world challenges like rotation, scaling, and translation can significantly impact a watermark’s resilience. Let’s break down how different methods perform under these conditions.
Performance Data and Results
Performance in watermarking boils down to two key metrics: Normalized Correlation (NC) and Bit Error Rate (BER). A high NC paired with a low BER indicates a robust watermarking method. These metrics provide a clear snapshot of how effective a technique is in practice.
"Even very small geometric distortions can prevent the detection of a watermark… This problem is most pronounced when the original unwatermarked image is unavailable to the detector." – IEEE Transactions on Image Processing [1]
Among the tested methods, DFT-based templates consistently deliver strong results, maintaining high NC and low BER across rotation, scaling, and translation scenarios. However, these methods have a critical flaw: interpolation blurring can obliterate template anchor points, weakening the system [2]. On the other hand, standard DWT implementations struggle significantly, particularly with translation. This is due to their downsampling process, which makes them highly sensitive to even minor pixel shifts [4].
Computational demands also vary widely. For instance, traditional Fourier-Mellin methods are resource-heavy, requiring two separate 2-D DFT operations [2]. Meanwhile, registration algorithms designed to handle local geometric distortions can take up to 16 minutes to process a 256×256 image. Mesh-based models offer a faster alternative, cutting processing time to 100–200 seconds for larger 512×512 images [4]. One study tested RST-resilient watermarking methods using a database of 2,000 images, also running false-positive tests on 10,000 images to validate reliability [1].
Here’s a breakdown of how these methods perform:
| Watermarking Method | Translation Resistance | Rotation Resistance | Scaling Resistance | Primary Weakness |
|---|---|---|---|---|
| DWT (Standard) | Low | Low | Low | Highly sensitive to pixel shifting and desynchronization [4] |
| DFT-Based Templates | High | High | High | Templates destroyed by interpolation blurring [2] |
| Fourier-Mellin (LPM-DFT) | High | High | High | High computational cost; interpolation errors in frequency domain [2] |
| Deformable Pyramid (DPT) | High | Very High | Very High | Complex interpolation functions required [3] |
One more thing to keep in mind: amplitude modulation-based schemes naturally exhibit a baseline BER greater than zero, even without attacks. This happens due to prediction errors during the embedding process [4]. So, when setting detection thresholds, you’ll need to factor in this baseline error alongside any degradation caused by geometric transformations.
How ScoreDetect Handles Geometric Transformations

To tackle the challenges posed by geometric attacks like rotation, scaling, and translation, ScoreDetect takes a layered approach. By combining invisible watermarking with blockchain verification, it ensures digital ownership remains provable even when content undergoes these transformations.
Invisible Watermarking Technology
The Enterprise plan of ScoreDetect uses Fourier-Mellin domain transformation to embed watermarks that can withstand geometric distortions. Here’s how it works:
- Image data is transformed into the Fourier domain.
- Magnitudes are resampled into log-polar coordinates, converting rotation into a cyclical shift and scaling into a linear adjustment. This makes detection significantly easier [1].
- By embedding the watermark in the Fourier magnitude, the system achieves translation invariance, effectively separating translation from other distortions [1].
This approach is similar to traditional template-based methods, but with a key difference: the watermark remains invisible. For professionals in media, marketing, and e-commerce, this means their assets are protected without compromising visual quality or the user experience. Additionally, the system uses blind detection, meaning it can extract the watermark and correct distortions without needing access to the original, unwatermarked file.
This watermarking system is further reinforced by blockchain verification, adding another layer of security.
Blockchain Technology for Copyright Protection
ScoreDetect leverages the SKALE blockchain to store a unique checksum (hash) of digital content, creating a tamper-proof record of the original file. Any changes to the file alter its data, resulting in a checksum methods that no longer match the one stored on the blockchain. This provides undeniable proof of alteration.
"ScoreDetect does not store any digital assets or content. It only stores the checksum of the content on the blockchain." – ScoreDetect
The blockchain not only secures the checksum but also generates verification certificates within seconds. These certificates include transaction URLs and timestamps, offering quick and reliable proof of ownership. With zero gas fees and an eco-friendly cost model, the platform is both efficient and sustainable. For older intellectual property, the timestamping feature helps establish a "prior art" timeline, providing protection for historical content. As Kyrylo Silin, SaaS Founder & CEO, explains: "With ScoreDetect, I can take pictures for my travel blog and be confident that nobody will claim them as theirs. I can always prove that I am the author."
Automated Detection and Takedown
ScoreDetect goes beyond embedding and verification by automating enforcement. Its AI-powered system can quickly identify and analyze content that has been geometrically transformed, achieving a 95% detection rate. Once identified, it automates takedown notices with a success rate exceeding 96%.
This end-to-end solution – spanning prevention, detection, and enforcement – simplifies content protection across its entire lifecycle. For industries like healthcare, finance, and government, where managing large digital asset libraries is a challenge, this automation reduces the need for manual oversight and speeds up copyright enforcement. Additionally, users can link ScoreDetect with over 6,000 web apps through Zapier integration, enabling automatic timestamping of new content as it’s created.
Conclusion
Geometric transformations like rotation, scaling, and translation are some of the simplest yet highly effective methods for attacking watermarked content. These techniques disrupt the watermark’s alignment, altering pixel orientation to the point where the detector can no longer identify or retrieve the embedded signal [5].
This guide has explored several strategies to counter these challenges. Transform domain techniques, such as Fourier-Mellin and log-polar mapping, simplify the correction of rotation and scaling by converting them into manageable shifts. Template-based resynchronization embeds anchor points, allowing detectors to estimate and reverse geometric distortions. Meanwhile, deep learning methods use neural networks to identify patterns even when distortions are present. Each method comes with its own balance of computational demands, robustness, and capacity.
FAQs
Why do tiny rotations or shifts break watermark detection?
Tiny rotations or shifts can interfere with watermark detection by altering the spatial arrangement of pixels. Since many watermarking systems depend on exact pixel alignment to detect and synchronize the watermark, even slight geometric changes can make identification or extraction difficult.
What’s the best way to make a watermark survive resizing?
To make sure a watermark stays intact during resizing, you need techniques that can handle geometric changes like scaling, rotation, and translation. Strategies such as using Fourier-Mellin transform-based invariants or multiscale block matching are effective. These methods are designed to resist distortions, ensuring the watermark remains recognizable even after resizing or other geometric adjustments.
How can blind watermarking stay detectable after RST edits?
Blind watermarking can withstand edits like rotation, scaling, and translation (RST) by leveraging features or transforms that remain unchanged under these modifications. Popular approaches include embedding the watermark using Fourier-Mellin transform-based invariants or employing deformable pyramid transforms alongside multiscale block matching. These techniques provide strong resistance to geometric attacks, ensuring the watermark remains detectable even after challenges like cropping, compression, or other distortions.

