Invisible watermarking embeds hidden data into PDFs to protect content without altering its appearance. Unlike visible watermarks, this method is discreet and resilient against compression, format changes, and editing. It embeds a "hidden serial number" using techniques like spatial domain tweaks, frequency modifications, or transparent text layers. These watermarks allow content owners to trace leaks, deter misuse, and maintain document quality.
Key points:
- Purpose: Protect PDFs from piracy, leaks, and unauthorized sharing.
- Techniques: Adjust pixels, transform frequencies, or add transparent text.
- Durability: Survives format conversions and compression.
- Applications: Ownership proof, forensic tracking, and content monitoring.
Tools like ScoreDetect enhance this process with AI detection, blockchain-enhanced verification, and automated takedown notices, ensuring robust security for critical documents.
How Invisible Watermarking Works
How Invisible PDF Watermarking Works: 3 Embedding Methods
Methods for Embedding Watermarks
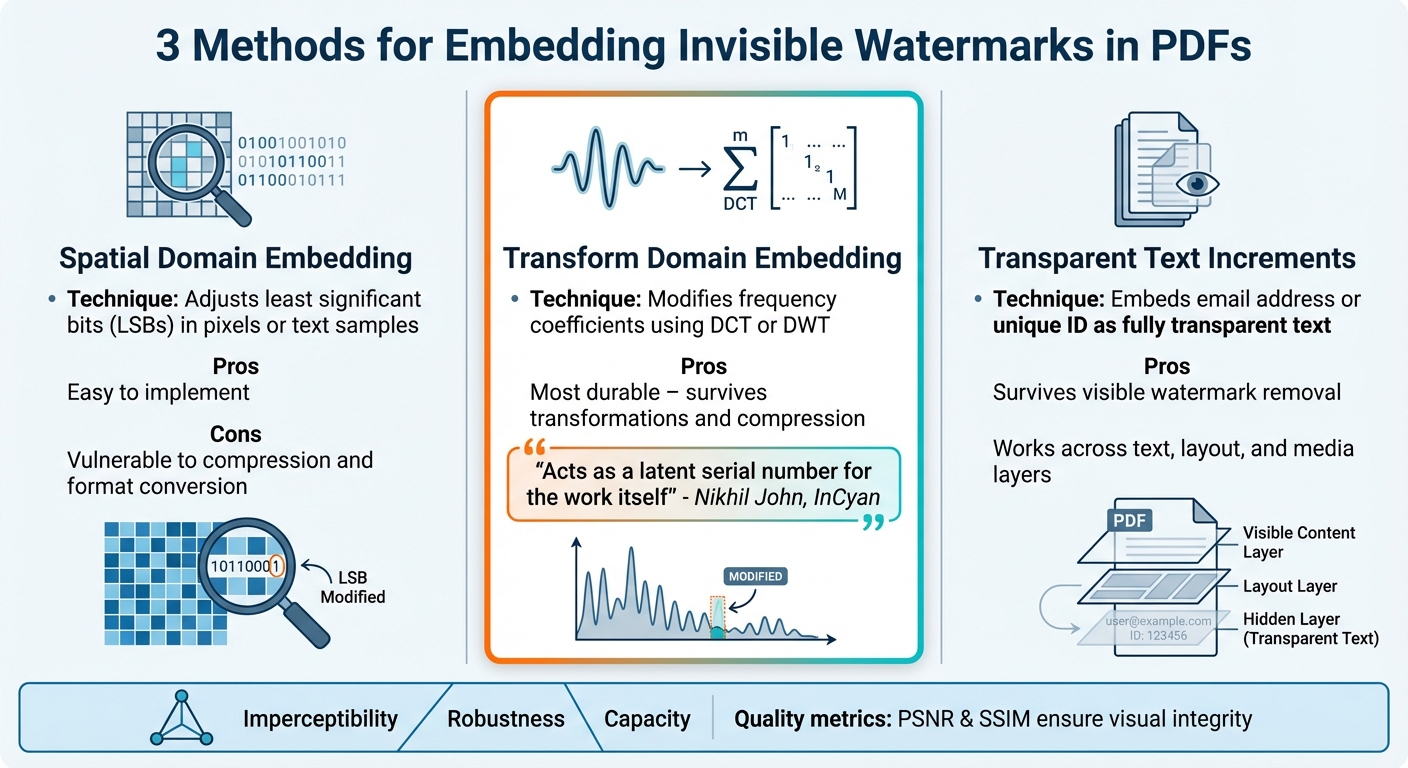
Invisible watermarking embeds data into PDFs by making subtle, undetectable changes, creating a persistent identifier that doesn’t interfere with the document’s appearance. Several techniques are used to achieve this:
- Spatial domain embedding tweaks pixel or text sample values by adjusting the least significant bits (LSBs). While this method is easy to implement, it’s vulnerable to compression. For example, converting a PDF to a lower-quality format might degrade or erase the watermark entirely.
- Transform domain embedding modifies frequency coefficients, using methods like the Discrete Cosine Transform (DCT) or the Discrete Wavelet Transform (DWT), instead of altering raw pixels. This approach is more durable. Nikhil John from InCyan explains, "Properly designed invisible watermarks can survive those transformations and act as a latent serial number for the work itself" [2]. Since this technique aligns with modern compression codecs, it offers stronger protection against data loss.
- Transparent text increments embed identifying information, such as an email address or unique ID, as a fully transparent text line. This hidden marker remains intact even when visible watermarks are removed [1]. Additionally, because PDFs are multi-layered files, advanced systems can synchronize watermark signals across text, layout, and media elements for heightened security [2].
These techniques are not only designed as digital piracy solutions with watermarking but also require precision to ensure the document’s visual integrity remains intact.
Preserving Document Quality
Maintaining a document’s visual quality while embedding trackable data is a key challenge in invisible watermarking. To ensure changes are imperceptible, engineers use perceptual modeling alongside quality metrics like Peak Signal-to-Noise Ratio (PSNR) and Structural Similarity Index (SSIM).
The human eye is particularly sensitive to alterations in flat gradients and sharp edges but is less perceptive to changes in textured or complex areas. By embedding watermark data in busy backgrounds or intricate graphics, systems can hide tens to hundreds of bits of information without compromising the document’s appearance. This delicate balance, often referred to as the watermarking triangle – imperceptibility, robustness, and capacity – ensures the document looks unchanged while embedding a hidden trail for source identification [2].
This careful calibration protects the document’s authenticity while reinforcing its forensic trail, providing a strong layer of digital protection. This technology forms a critical part of a comprehensive IP copyright protection solution.
sbb-itb-738ac1e
ScoreDetect‘s PDF Watermarking Solution

Undetectable Watermarking Technology
ScoreDetect uses steganographic techniques to embed invisible watermarks into PDFs. These techniques subtly modify pixel values in images and graphics, making the watermark completely undetectable to the human eye. By focusing on high-resolution images, the system inserts a persistent identifier without altering the document’s appearance or quality [3].
The precision lies in targeting specific pixels in intricate areas, such as textured backgrounds or detailed graphics. This ensures the watermark remains hidden while still being identifiable by specialized software [4]. Even through format conversions and compression, the watermark’s integrity is maintained. ScoreDetect combines this pixel-level accuracy with AI to actively monitor and protect your content.
AI-Powered Detection and Enforcement
After applying the watermark, ScoreDetect’s AI system takes over by scanning the web for your protected content. Its intelligent web scraping achieves a 95% success rate in bypassing common digital barriers, helping it locate unauthorized copies online. This continuous monitoring ensures robust protection.
When a match is found, the system verifies unauthorized use with concrete evidence and sends automated delisting notices. These notices boast an impressive 96% takedown rate [3]. This entire process – detection, verification, and removal – runs automatically, saving you time and reducing legal expenses. To further secure ownership, ScoreDetect backs its protection with blockchain technology.
Blockchain-Based Ownership Verification
To strengthen copyright protection, ScoreDetect records a unique checksum of your PDF on the blockchain. This creates a verifiable proof of authorship and creation date, without storing the actual file. Unlike metadata tags, which can be removed or altered during editing, blockchain entries provide a permanent and tamper-proof ownership trail [4].
This feature is especially useful for industries like legal services, R&D, and mergers and acquisitions, where proving the origin of confidential documents is essential. Additionally, ScoreDetect integrates with over 6,000 web apps through Zapier, enabling seamless workflows to protect PDFs as soon as they are created or updated.
Benefits of Invisible Watermarking for PDFs
Tracking and Leak Detection
Leaks often occur when authorized users share files through personal emails or with external partners. Invisible watermarking tackles this issue by embedding identity markers, metadata, and timestamps into each unique PDF version. This creates a clear trail of accountability. For example, if a licensed research report surfaces online, the embedded watermark can identify the specific copy and the recipient responsible for the leak [5].
"Forensic watermarking answers a different question: ‘If this gets shared, can we trace who it came from?’" – All About PDF [5]
Preventing Piracy
Invisible watermarking plays a dual role: it identifies unauthorized sharing and discourages it. Unlike visible watermarks, which can often be removed with basic editing tools, invisible watermarks are far more difficult to erase. This traceability fosters a sense of accountability among recipients, making them less likely to share documents inappropriately. This concept is often referred to as "deterrence through accountability" [5].
Adding a simple notice about embedded traceable identifiers can further discourage improper sharing. This approach not only deters piracy but also aligns easily with existing document management and authenticity verification practices [5][6].
Easy Workflow Integration
Modern tools have made it simple to integrate invisible watermarking into everyday workflows. For instance, automatic PDF protection can be applied as soon as documents are created or updated. Platforms like ScoreDetect’s WordPress plugin go a step further by generating verifiable proof of ownership on the blockchain for every published or updated article, which also boosts SEO.
Invisible watermarking is often part of a broader document security strategy. When combined with access controls, usage restrictions, and remote access revocation, it ensures the protection of critical documents like acquisition plans, partner discount sheets, or internal HR reports throughout their lifecycle [5].
Conclusion
Key Takeaways
Invisible watermarking plays a crucial role in safeguarding PDFs. Unlike visible watermarks or metadata, which can be easily removed or altered, invisible watermarks embed a hidden serial number directly into the document’s media signal. This makes them resistant to cropping, re-exporting, compression, and even edits powered by AI. The technology strikes a balance between being undetectable, durable, and capable – ensuring the watermark remains intact through format changes and flattening processes while maintaining the original quality of the file.
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." – Nikhil John from InCyan [2]
When paired with AI and blockchain verification, these tools provide businesses with a tamper-evident, time-stamped log that meets legal and regulatory standards [2]. Together, they form the backbone of protection solutions like ScoreDetect.
Getting Started with ScoreDetect
ScoreDetect builds on these principles to offer a complete protection suite. It combines invisible watermarking with AI-powered discovery, achieving a 95% success rate in content matching and 96% success in takedown notices. The platform also uses blockchain to record content checksums, providing verifiable proof of ownership without storing the actual digital files.
For businesses exploring an entry-level option, the Pro plan includes blockchain-based timestamps, unlimited content protection, and integration with over 6,000 web apps through Zapier. A dedicated WordPress plugin further simplifies the process by automatically capturing and timestamping every published or updated article, creating instant proof of ownership while also improving SEO. You can start with a 7-day free trial to see how invisible watermarking can protect your PDFs, or schedule a demo to discover enterprise solutions tailored to your needs.
FAQs
Can an invisible PDF watermark identify who leaked a document?
Invisible PDF watermarks can indeed help pinpoint the source of a document leak. These hidden markers embed unique, traceable details into each copy, functioning like a covert serial number. Even if the document undergoes changes such as printing or compression, the watermark remains intact, ensuring reliable identification. With specialized tools, the embedded watermark in a leaked document can be analyzed to trace it back to the specific user or source responsible for its unauthorized release.
Will invisible watermarks survive printing, scanning, or screenshots?
Invisible watermarks, when implemented correctly, are built to endure various transformations such as printing, scanning, or even taking screenshots. These watermarks embed data directly into the media in a way that resists these alterations, ensuring the watermark stays intact. This makes them a reliable tool for safeguarding content.
How does ScoreDetect’s blockchain checksum prove ownership?
ScoreDetect leverages a blockchain checksum to establish proof of ownership. It generates a cryptographic hash of your content, which is then securely recorded on the blockchain. This process provides verifiable evidence of control over your digital asset – without the need to store the actual file on the blockchain.