Piracy costs the entertainment industry billions annually, especially for live events like sports, where timing is critical. Real-time watermarking offers a powerful solution by embedding invisible identifiers – such as User IDs or timestamps – into video streams. This allows content owners to trace leaks quickly and take immediate action. Unlike traditional DRM, watermarking works even after content is captured, making it a key tool in combating piracy.
Key Takeaways:
- Global video piracy losses in 2023: $67 billion.
- Live sports piracy: 210 million households globally stream illegally.
- Real-time watermarking benefits:
- Embeds invisible, session-specific markers into streams.
- Tracks leaks back to specific users or devices.
- Enables detection and shutdown of pirated streams within seconds.
- Techniques include: A/B variant watermarking, edge-based injection, and client-side compositing.
- Future outlook: U.S. streaming providers may lose $113 billion by 2027 without stronger anti-piracy measures.
Watermarking is reshaping how content creators and distributors protect their assets, combining speed, precision, and traceability to tackle piracy effectively.
Forensic Watermarking for Video Protection | How It Works & Why It’s Essential
sbb-itb-738ac1e
How Real-Time Watermarking Works
Real-time watermarking embeds invisible identifiers into video streams as they are delivered, ensuring each viewer gets a uniquely marked version without compromising video quality. Unlike traditional watermarks that are added during production, these marks are inserted dynamically during distribution. This process involves embedding forensic metadata – such as User IDs, Device IDs, IP addresses, and timestamps – into the video signal. The result is a unique fingerprint that remains intact even after re-encoding, resizing, or screen recording.
Dynamic Watermarking for Live Content
When it comes to live streaming, watermarking must happen instantly to avoid frustrating delays for viewers. One popular method, A/B variant watermarking, divides the video into short segments (usually 2–5 seconds each) and creates two encoded versions – Variant A and Variant B – for each segment. As the content streams, the CDN delivers a unique sequence of segments to each viewer. For instance, one user might receive ABABA, while another gets ABBAA. With just 23 segments, it’s possible to create unique identifiers for 10 million users [7].
Another option is edge-based injection, where advanced Experience Delivery Networks (XDN) use intelligent edge nodes to insert watermarks directly into unicast streams at the delivery point. This method ensures ultra-low latencies of 200–400 ms while avoiding the need for dual A/B encoding, which can add up to 5 seconds of delay [5].
A third approach is client-side compositing, where the watermark is applied as a graphical overlay by the media player on the user’s device. This method is highly scalable since the computational load is distributed across devices rather than centralized servers. However, it can be more vulnerable to tampering if the user’s device lacks proper security.
These techniques enable watermarking to remain invisible while ensuring effective detection, even during attempts to obscure its presence.
Invisible and Non-Invasive Techniques
The algorithms used in real-time watermarking are designed to be undetectable to viewers but highly effective for piracy investigations. One method, bitstream modification, identifies specific parts of the video bitstream that can be subtly altered without affecting visual quality. The metadata sent to the CDN edge or client device includes instructions for embedding these modifications.
More advanced techniques use processes like Discrete Cosine Transform (DCT) and Singular Value Decomposition (SVD) to embed data directly into the video signal. This approach integrates the watermark into the content itself rather than as a separate overlay, maintaining the Peak Signal to Noise Ratio (PSNR) and overall bitrate. Additionally, the watermark’s dynamic updates every few seconds make it harder to remove through collusion attacks. Even if the video is rotated, cropped, or altered geometrically, detection remains possible thanks to techniques like Zernike moments.
Once embedded, these imperceptible watermarks serve as a crucial tool for tracing and addressing unauthorized usage.
Tracking and Identifying Unauthorized Usage
Watermarks become essential for enforcement once they are embedded. If pirated content appears online, anti-piracy teams can extract the watermark to identify the user, device, or session responsible for the leak. For live events, quick extraction is critical to protect the limited broadcast window. Modern forensic tools can trace pirate sources within 5 to 15 seconds [5], enabling swift takedown actions to minimize revenue loss.
"Watermark extraction needs to take place in seconds." – Viaccess-Orca [6]
The process is efficient, too – a one-hour video fingerprint requires only about 115 KB of data [7]. This compact information provides a clear audit trail, including User IDs, IP addresses, and timestamps, giving rights holders the evidence needed for legal action. By deterring future piracy attempts, forensic watermarking has become a key part of anti-piracy strategies. This is especially vital as video piracy is expected to result in a staggering $113 billion in revenue losses for U.S. streaming providers by 2027 [6].
Key Benefits of Real-Time Watermarking in Anti-Piracy Strategies
Stronger Content Security
Real-time watermarking embeds a unique digital fingerprint into each stream, making every copy of your content traceable to its source – even if pirates attempt to alter it through re-encoding, screen recording, or format changes [3]. This means that even after content leaves the secure environment of your platform, it remains identifiable.
Unlike standard DRM, which focuses on preventing unauthorized downloads, forensic watermarking continues to work even after content is captured. Whether pirates use external cameras or screen recording tools, the watermark survives these efforts [3][6]. Server-side watermarking adds another layer of protection by embedding the watermark within the delivery network (CDN), keeping it concealed from hackers [5].
There’s also a psychological aspect. When pirates are aware they can be uniquely identified and traced, the risk of distributing content illegally becomes much higher [3]. This added deterrence not only discourages piracy but also helps protect your revenue.
Reduced Revenue Loss
The financial impact of piracy is staggering. U.S. streaming providers lose an estimated $20 billion annually due to content theft [6]. For pay-TV and video operators, piracy can account for losses of 10% to 25% of their yearly revenue [9]. Real-time watermarking helps combat these losses by enabling the swift identification and shutdown of unauthorized streams.
Speed is crucial for live broadcasts. Server-side watermarking solutions can pinpoint pirate sources in as little as 5–15 seconds [5]. This allows providers to take immediate action, cutting off illegal streams during the critical broadcast window. Anne-Sophie Cornet, Product Manager of Anti-Piracy Services at Viaccess-Orca, emphasizes this point: "Identify the source quickly enough and you can shut down the stream" [6].
"Piracy is our biggest competitor still, by far. Content piracy is hard because we can’t compete on price."
– Kjetil Rohde Jakobsen, Global Director Products and Partners, iflix [9]
This rapid response capability shifts the approach from merely detecting piracy to actively recovering revenue. By offering undeniable proof of unauthorized use, watermarking supports swift takedown requests and helps redirect revenue back to legitimate providers [8][9].
Better Legal Support and Enforcement
Beyond preventing piracy and recovering revenue, real-time watermarking strengthens legal enforcement efforts. Each watermark is tied to session timestamps, enabling a direct link between unauthorized distribution and the specific moment a user accessed your content [3]. This creates clear, court-admissible evidence that connects a leak to an individual account, device, and location.
Modern watermarking systems also generate tamper-proof logs and detailed audit trails [3]. These records document every step of the process – from detection to evidence extraction – providing solid support for legal proceedings and DMCA takedown requests.
When pirates understand that leaks can be traced to specific sources and backed by strong legal evidence, the risks of engaging in piracy increase significantly. Research highlights the challenge: while 90% of sports fans subscribe to legitimate services, 42% of those who watch pirated content do so daily [5]. Real-time watermarking makes piracy not just detectable but enforceable.
"Without effective forensic watermarking in place… content and revenue will be lost and there is no way of knowing where the leak came from."
– Tim Pearson, Senior Director, Product Marketing, NAGRA [9]
Implementation Best Practices for Real-Time Watermarking
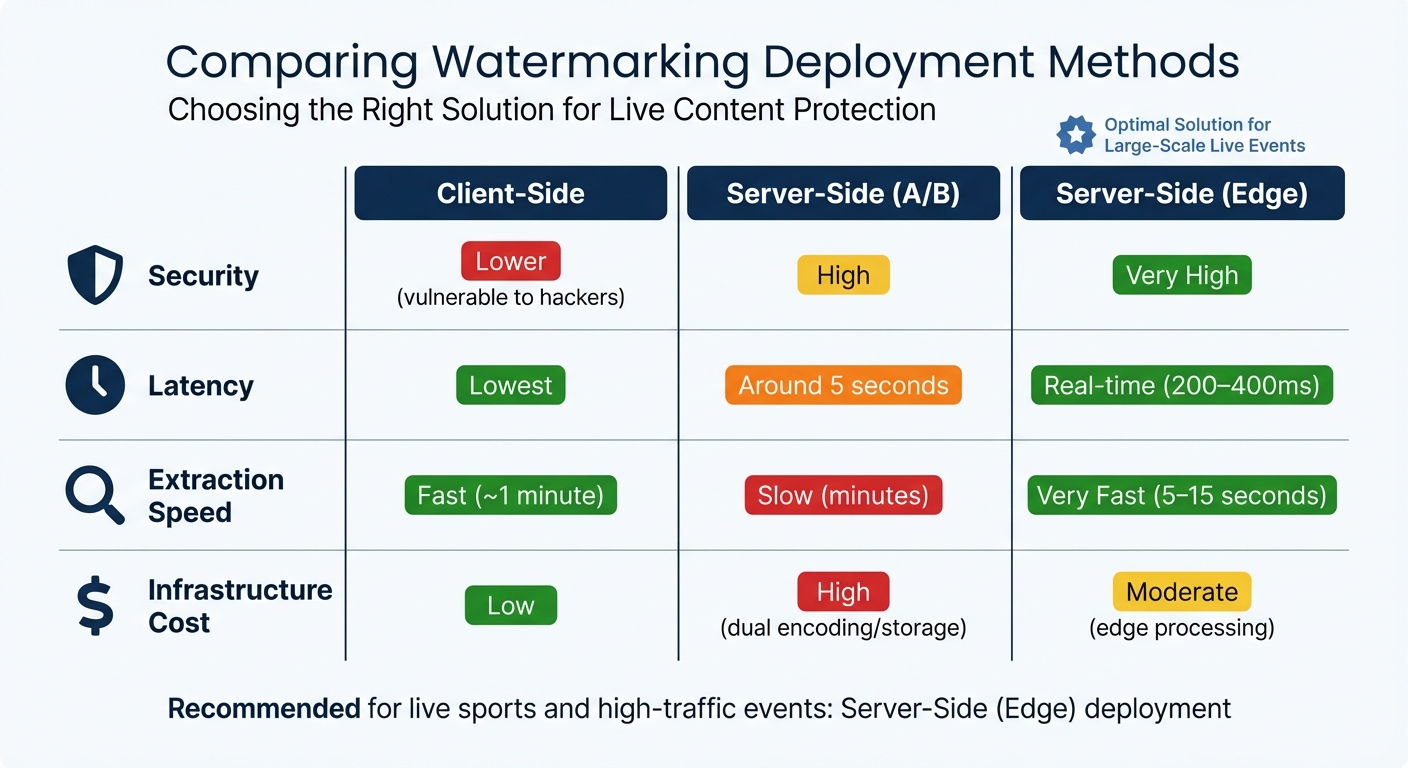
Real-Time Watermarking Methods Comparison: Client-Side vs Server-Side Solutions
Choosing the Right Watermarking Solution
When selecting a watermarking system, you need to weigh speed, security, and scalability carefully. For live content, low latency is non-negotiable – your solution should embed watermarks within 200–400 milliseconds and extract them in 5–15 seconds. This ensures you can act quickly during the critical 15-minute window to disrupt piracy [5].
A good watermarking system must also withstand common distortions like re-encoding, resizing, and compression while remaining invisible, even in high-quality formats like 4K HDR [3].
Deployment method plays a crucial role. Server-side watermarking keeps the code secure from tampering and can be integrated at edge nodes to reduce storage demands. On the other hand, client-side solutions are easier to deploy across a variety of devices [5]. Whichever you choose, ensure the system includes robust forensic identifiers for tracking leaks [3].
| Feature | Client-Side | Server-Side (A/B) | Server-Side (Edge) |
|---|---|---|---|
| Security | Lower (vulnerable to hackers) | High | Very High |
| Latency | Lowest | Around 5 seconds | Real-time (200–400ms) |
| Extraction Speed | Fast (~1 minute) | Slow (minutes) | Very Fast (5–15 seconds) |
| Infrastructure Cost | Low | High (dual encoding/storage) | Moderate (edge processing) |
For large-scale events, like major sports broadcasts with millions of viewers, a cloud-based approach with edge processing is essential to handle surges in traffic [2]. Additionally, test the watermarking system on poor-quality, heavily compressed pirate copies – not just on clean, high-resolution content – to understand the differences between digital watermarks and copyright protection [3].
Finally, check that your current infrastructure can support these advanced watermarking techniques without major overhauls.
Ensuring Compatibility with Existing Systems
To integrate watermarking effectively, your players, CDNs, and encoding systems must support the chosen method, such as A/B variant delivery [3].
Edge-based watermarking is a modern alternative that embeds watermarks at edge nodes, maintaining real-time latency while avoiding the typical 5-second delay of traditional server-side methods [5]. Ensure the system is compatible with key protocols like WebRTC for real-time streaming, as well as HLS, DASH, and SRT for broader distribution [5].
Watermarking works best as part of a layered security approach. Combine it with Digital Rights Management (DRM) and access controls for comprehensive protection [3]. While DRM blocks unauthorized downloads, watermarking provides traceability if someone records or leaks the content. Ensure the watermarking system integrates seamlessly with your existing DRM setup.
Multi-device functionality is a must. Your watermarking solution should work across connected TVs, smartphones, desktops, and older devices without requiring separate implementations for each platform [2]. Client-side options may need custom SDKs or player integration, while server-side methods often offer universal compatibility through manifest-based or stream-based delivery.
Monitoring and Regular Updates
After integration, continuous monitoring is essential to stay ahead of evolving piracy tactics. By actively tracking usage logs and access patterns, you can quickly identify unauthorized sharing or suspicious activity [11]. Set up automated alerts to detect and disrupt illegal streams in real time [5].
Regular audits are equally important. Pirates often use advanced editing tools or AI to remove watermarks, so periodic updates are necessary to keep your system effective [10]. Test extraction performance regularly – if watermarks can be removed or obscured, your deterrent loses its value.
"The opportunity window to discourage audiences from consuming illegal streams is as short as 15 minutes. Extraction, detection, and cessation all must follow each other smoothly and seamlessly for action to be taken."
– Mélanie Langlois & Fatima Peñaranda, Product and Sales Managers, Viaccess-Orca [2]
Keep detailed forensic records that document the "when", "who", and "how" of breaches using embedded metadata [11]. These reports not only provide evidence for legal action but also help identify recurring piracy patterns. As your audience and content library grow, ensure your watermarking system can scale without introducing unacceptable latency or performance issues.
ScoreDetect‘s Role in Real-Time Watermarking and Anti-Piracy

ScoreDetect takes anti-piracy to the next level by combining advanced watermarking with real-time monitoring and enforcement tools.
Invisible, Non-Invasive Watermarking
ScoreDetect embeds invisible forensic watermarks directly into digital content. These watermarks carry unique identifiers like User IDs, IP addresses, and session timestamps, making it possible to pinpoint the exact source of a leak – all without compromising the content’s quality [3].
Unlike visible watermarks that can disrupt the viewing experience, ScoreDetect’s method is entirely undetectable to the audience. Each piece of content is tagged with a unique digital fingerprint, making it ideal for live streaming and real-time content distribution.
Detection and Takedown System
Once the watermark is embedded, ScoreDetect’s AI-driven scanning tools actively search the internet for pirated content. With a 95% match rate, the system can identify stolen streams – even if pirates try to alter the content by cropping, transcoding, or adding overlays [4][7].
When unauthorized use is detected, ScoreDetect automatically issues delisting notices, achieving a 96% takedown rate. This automated process eliminates the need for manual intervention, saving time and resources. Additionally, the system can trigger immediate responses, such as suspending user accounts or blocking devices linked to the leak [4]. All of these actions integrate seamlessly into ScoreDetect’s broader anti-piracy framework.
Blockchain Technology for Copyright Protection
ScoreDetect also leverages blockchain technology to enhance digital watermarking and copyright protection. By creating a checksum of the content and recording it on the blockchain, the system establishes a timestamped, unchangeable record of ownership – without storing the actual digital files [1].
This blockchain record acts as a tamper-proof audit trail that holds up in legal proceedings [3]. Using perceptual hashes derived from the structural details of video frames, ScoreDetect can verify ownership without requiring access to the original content [1]. This immutable record serves as compelling legal evidence of authenticity.
"The preservation of the blockchain and the impossibility of tampering or forging any of the data stored within may give irrefutable proof of the authenticity of digital works and strengthen the case for their integrity." – Darwish et al., PLOS One [1]
For media companies and creators grappling with piracy costs that reach $50 billion annually [3], ScoreDetect’s blend of invisible watermarking, automated detection, and blockchain verification offers a robust solution to combat unauthorized content distribution.
Conclusion
Digital piracy is a massive financial drain, with U.S. streaming providers projected to lose $113 billion by 2027 [6]. Real-time watermarking has become a key tool in combating this issue because it tackles a critical gap in traditional security: tracking leaks after decryption.
By embedding invisible, session-specific markers, watermarking enables content owners to pinpoint the source of leaks [3][6]. This is especially vital for live events like sports broadcasts, where the value of the content diminishes within minutes. In such cases, identifying and shutting down unauthorized streams within 5 to 15 seconds is essential to preserving revenue [5].
The shift toward a control-based approach is redefining content protection:
"The near future of content protection looks less like a wall and more like a control system." – Promwad [4]
A robust strategy incorporates watermarking into a multi-layered security framework. This not only creates a technical barrier but also serves as a psychological deterrent. When subscribers know their sessions are uniquely traceable, they’re less inclined to redistribute content [3]. With anti-piracy technology spending expected to hit $229 million by 2024 [5], companies that adopt these tools can better safeguard their revenue streams and maintain subscriber trust.
ScoreDetect stands out as an example of this comprehensive approach. Combining real-time watermarking with advanced detection systems, it provides a full-spectrum solution. From invisible watermarking and AI-powered detection to automated takedowns and blockchain-verified ownership, ScoreDetect equips digital asset managers with tools to stay ahead of evolving piracy tactics. In today’s landscape, the question isn’t whether to invest in protection technologies – it’s how quickly you can implement them before the next leak costs you thousands.
FAQs
Does real-time watermarking still work after screen recording?
Yes, real-time watermarking can still work effectively even after screen recording, depending on the technology in place. Advanced methods, like forensic watermarking or cross-attention techniques, are specifically built to withstand screen recording while preserving the watermark’s integrity. Although no system can offer absolute protection, these technologies greatly improve the chances of identifying and tracing pirated content, even when it has been captured through screen recording.
What is the best watermarking method for low-latency live streams?
Real-time, on-the-fly watermarking is the best approach for low-latency live streams. This method embeds watermarks dynamically as the content is streamed, ensuring minimal delays while offering instant protection against misuse.
What data is embedded in a forensic watermark, and is it privacy-safe?
A forensic watermark embeds information like user IDs, device details, timestamps, or metadata directly into digital content. This allows content owners to trace misuse and confirm ownership. These watermarks are invisible and non-intrusive, ensuring they do not reveal personally identifiable information. Only authorized parties can access the embedded data, making it a secure and privacy-conscious way to combat piracy.

