Audio watermarking embeds hidden signals into audio files to verify ownership and protect against piracy. However, filtering – like low-pass or high-pass adjustments – can erase these signals, making durability a challenge. For instance, studies show no watermarking system has fully resisted all distortions, including advanced AI-based attacks.
Key insights:
- Filtering alters the frequency components where watermarks are embedded.
- Low-pass filters are particularly damaging, often erasing watermarks in higher frequencies.
- Embedding in mid-frequency ranges (500 Hz–4,000 Hz) improves resistance.
- Advanced systems like AWARE maintain near-zero error rates under filtering attacks.
To strengthen watermark durability:
- Use transform-domain methods like DWT, DCT, or SVD.
- Embed watermarks in the mid-frequency range for better protection.
- Employ psychoacoustic models to ensure inaudibility while maintaining resilience.
For full protection, combine watermarking with tools like detection platforms, blockchain technology for timestamping, and automated takedown systems. This multi-layered approach ensures better content security in today’s digital landscape.
UOC’s Audio Watermarking System, High-fidelity recovery under extreme conditions
sbb-itb-738ac1e
How Filtering Damages Audio Watermarks
Filtering attacks are designed to weaken or completely remove the frequency bands where watermark signals are embedded. These signals are often subtle and spread across the audio spectrum, making them vulnerable to targeted filtering techniques. The problem is particularly severe for watermarks placed in higher frequencies, as many systems hide data there to keep it imperceptible. However, low-pass filters – commonly used in audio compression and streaming – strip away these upper frequencies, effectively erasing the watermark data entirely [4][2]. Even advanced AI-driven watermarking techniques struggle to maintain integrity when faced with aggressive filtering [4].
Common Types of Filtering Attacks
Different filtering methods exploit specific weaknesses in watermarking systems, each with its own destructive capabilities.
- Low-pass filters: These remove high-frequency components above a certain cutoff. Since many watermarking systems rely on higher frequencies to remain undetectable to the human ear, low-pass filtering can completely eliminate the watermark. For example, tests on the AudioSeal watermarking system showed a Bit Error Rate (BER) increase to 14.58% when subjected to low-pass filtering [2].
- High-pass filters: These strip away low-frequency components. While fewer watermarks are embedded in lower ranges, high-pass filters can disrupt synchronization markers essential for locating the watermark. AudioSeal’s BER rose to 7.08% when exposed to high-pass filtering at 500 Hz [2].
- Band-stop (notch) filters: These target specific narrow frequency ranges, allowing attackers to isolate and remove the exact frequency where the watermark resides. This method caused AudioSeal’s BER to spike to 33.81% [2]. By contrast, the AWARE system successfully avoided such attacks by embedding watermarks in a mid-frequency range (500 Hz to 4,000 Hz), maintaining a 0.00% BER under both low-pass and high-pass filtering [2].
How Filtering Reduces Watermark Detection
Filtering doesn’t just increase error rates; it also disrupts the entire detection process. By altering energy distributions and transform coefficients, filtering undermines the ability of detection systems to identify watermark signals [3]. Most systems rely on frequency-domain coefficients derived from methods like the Fast Fourier Transform (FFT), Discrete Wavelet Transform (DWT), or Discrete Cosine Transform (DCT). Filtering changes the magnitude and phase of these coefficients, leaving detectors without the necessary evidence to recover watermark bits [2].
Time-domain watermarking techniques, which modify signal amplitudes directly, are particularly vulnerable. Scientific Reports highlights that these methods often fail under common signal processing attacks [3]. While transform-domain methods are generally more resistant, their success still hinges on the stability of transform coefficients. Aggressive filtering can degrade these coefficients beyond the point of detection [1][3].
The consequences of filtering go beyond technical failures. By raising BER and erasing watermark signals, filtering also eliminates the crucial provenance evidence needed to combat digital piracy [2]. A 2025 study examining 22 watermarking schemes revealed that none could withstand all tested distortions, including both traditional signal manipulations and AI-based attacks [4].
Key Requirements for Filter-Resistant Watermarks
Creating filter-resistant watermarks requires a delicate balance between robustness, imperceptibility, and embedding capacity – often referred to as the "Magic Triangle" trade-off. Meeting all three demands simultaneously is one of the toughest hurdles in audio watermarking [1]. As highlighted in a study published in Multimedia Tools and Applications:
"Robustness, imperceptibility and embedding capacity are the preliminary requirements of any digital audio watermarking technique. However, research has concluded that these requirements are difficult to achieve at the same time." [1]
Below, we’ll explore how each of these critical factors can be addressed to improve watermark durability against filtering.
Maintaining Audio Quality While Staying Hidden
For a watermark to work effectively, it must remain inaudible to listeners while being strong enough to withstand processing. This is achieved by embedding the watermark in the magnitude domain rather than the phase domain. Since human hearing is not highly sensitive to phase changes, attackers can easily manipulate phase without affecting perceived audio quality, potentially erasing the watermark [2].
The best strategies use level-proportional perceptual budgeting, which adjusts modifications based on the loudness of the audio. Larger adjustments can be made in louder sections, while quieter regions require subtler changes. This ensures that the watermark remains invisible to listeners while blending into the natural loudness variations of the audio [2]. For example, the AWARE watermarking system strikes this balance effectively, achieving a Perceptual Evaluation of Speech Quality (PESQ) score of 4.08 and a speech intelligibility (STOI) score of 0.97, while resisting filtering attacks [2].
Surviving Common Audio Processing
Once inaudibility is ensured, the watermark must also survive typical audio processing, such as spectral edits. A proven method is embedding the watermark in the mid-frequency range – between 500 Hz and 4,000 Hz. This range, known as the "audible midband", is less affected by standard low-pass and high-pass filters, helping the watermark remain intact [2].
Additionally, detection systems should operate in the Mel-spectrogram domain rather than relying solely on Short-Time Fourier Transform (STFT) representations. Mel-bands group spectral energy into perceptually relevant categories, making the watermark more resistant to distortions in the frequency domain. For instance, a Mel-based detector achieved a bit error rate (BER) of just 1.61% under neural vocoder resynthesis, compared to 50.30% for an STFT-only detector [2]. This approach ensures watermarks are still detectable even when filtering alters the audio’s spectral features.
Embedding Sufficient Data Without Degradation
To balance data capacity and resilience, a target payload of 16 bits per second is ideal [2]. Achieving this without compromising audio quality involves temporal evidence aggregation using a Bitwise Readout Head (BRH). This method gathers evidence over time, ensuring reliable decoding even when filtering reduces the available signal context. For example, under sample deletion attacks, a BRH-equipped model maintained a BER of 3.74%, while a traditional Fully Connected (FC) layer-based model saw its BER spike to 30.91% [2].
Another key technique is push-loss optimization, which ensures precise detection without significantly increasing noise levels that could degrade audio quality [2]. Additionally, using minimal temporal context – such as 1×1 convolutional kernels rather than larger ones – keeps watermark activations stable, even when the audio’s length or continuity is altered by filtering or splicing [2]. These methods enable efficient data embedding, ensuring watermarks remain detectable despite signal modifications caused by filtering.
Methods to Strengthen Watermark Durability
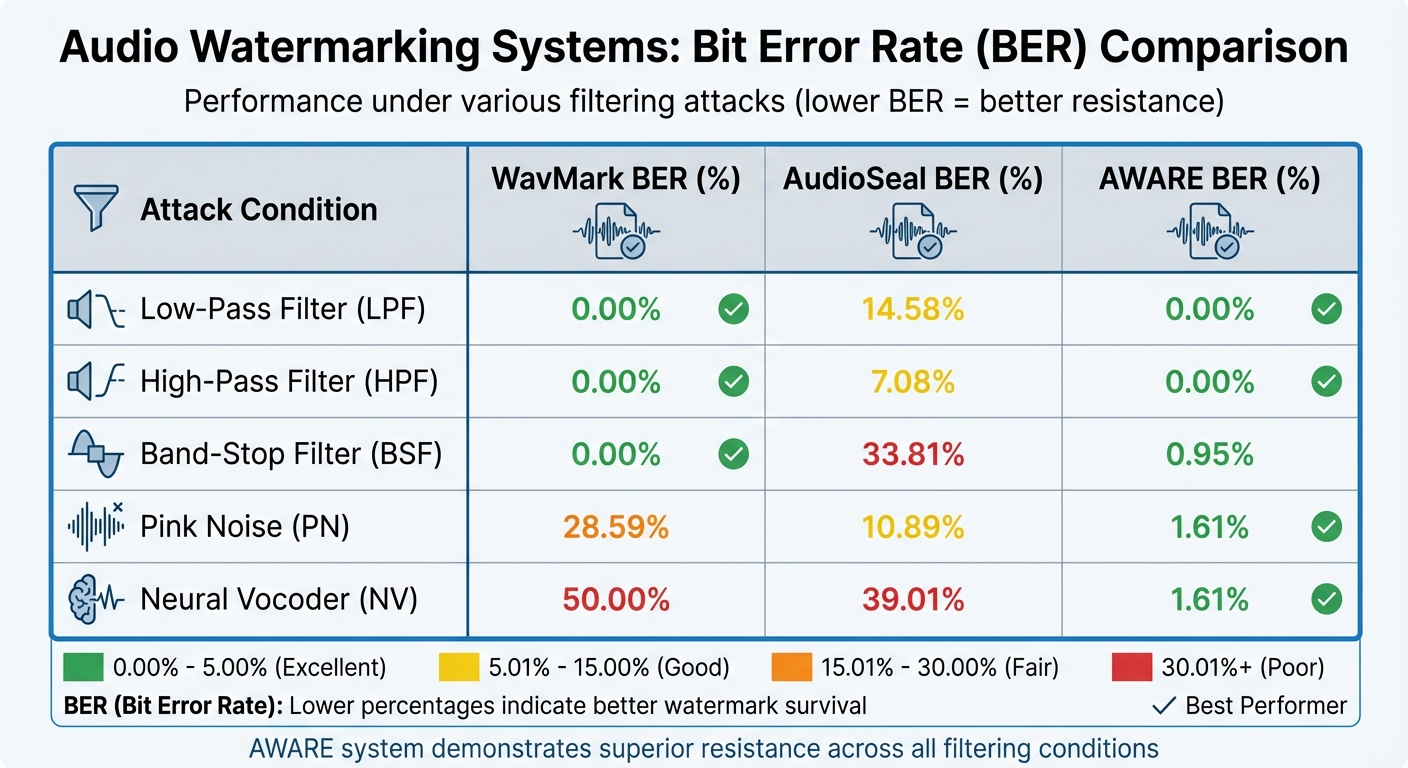
Audio Watermarking Systems Performance Comparison Under Filtering Attacks
Enhancing watermark durability against filtering requires a mix of advanced techniques, including transform methods, adaptive embedding, and the use of Singular Value Decomposition (SVD).
Frequency and Transform Domain Methods
Transform domain techniques, such as Discrete Wavelet Transform (DWT) and Discrete Cosine Transform (DCT), embed watermarks into the structural components of audio signals, making them harder to remove. By focusing on the audible midband range, typically between 500 Hz and 4,000 Hz, these methods help protect watermarks from basic low-pass or high-pass filtering. Embedding watermarks in the Short-Time Fourier Transform (STFT) magnitude spectrum is particularly effective, as listeners are less sensitive to phase changes [1].
Hybrid techniques, like DWT-SVD, strike a balance between being unobtrusive and resisting complex filtering. For instance, the AWARE system, which employs adversarial optimization in the time-frequency domain, has demonstrated impressive results. In benchmark tests, it achieved a 0.00% Bit Error Rate (BER) under both low-pass and high-pass filtering. In contrast, AudioSeal recorded a 14.58% BER under low-pass filtering and 33.81% BER under band-stop filtering [2].
| Attack Condition | WavMark BER (%) | AudioSeal BER (%) | AWARE BER (%) |
|---|---|---|---|
| Low-Pass Filter (LPF) | 0.00 | 14.58 | 0.00 |
| High-Pass Filter (HPF) | 0.00 | 7.08 | 0.00 |
| Band-Stop Filter (BSF) | 0.00 | 33.81 | 0.95 |
| Pink Noise (PN) | 28.59 | 10.89 | 1.61 |
| Neural Vocoder (NV) | 50.00 | 39.01 | 1.61 |
These results highlight the effectiveness of transform-based methods as a foundation for further advancements.
Adaptive Embedding with Perceptual Masking
Adaptive embedding takes watermarking a step further by tailoring the watermark’s strength to human perception. This method uses the Human Auditory System (HAS) to hide watermarks in regions where listeners are naturally less sensitive. By applying psychoacoustic models to calculate masking thresholds, strong watermark signals can be embedded without noticeable audio quality loss. The process adjusts watermark strength based on audio complexity, embedding stronger signals in more complex segments to withstand filtering and other attacks [1].
When combined with techniques like Singular Value Decomposition (SVD) or Quantization Index Modulation (QIM), adaptive embedding becomes even more effective, enhancing both durability and imperceptibility.
Singular Value Decomposition (SVD) and Other Advanced Methods
SVD-based methods add another layer of stability to watermarks, as singular values tend to remain consistent even when subjected to filtering or noise [1]. When integrated into hybrid approaches, such as DWT-SVD or DCT-SVD, these methods improve the balance between being unobtrusive and resistant to attacks.
Modern systems like AWARE push these advancements further through adversarial optimization. Developed by researchers from the University of Montenegro and DeepMark, AWARE was rigorously tested on datasets like VCTK and LibriSpeech at a 16 kHz sampling rate with a 16 bps payload. Using a Bitwise Readout Head to aggregate temporal evidence, AWARE consistently achieved lower error rates against filtering attacks, showcasing the potential of advanced techniques to boost watermark resilience [2].
Complete Content Protection Strategies
To address the weaknesses in filtering and other vulnerabilities, a multi-layered defense system is essential. While advanced watermark embedding is a key element, no single method can withstand all attacks, especially against neural compression and aggressive filtering [4]. The key lies in combining watermarking with detection platforms, blockchain verification, and automated enforcement tools to create a robust content protection framework.
Combining Watermarking with Detection Platforms
Embedding a watermark is just the first step. Detection platforms actively search for protected content across the internet using sophisticated web scraping tools. These systems boast a 95% success rate in bypassing anti-scraping measures, enabling them to scan streaming sites, file-sharing platforms, and social media for unauthorized uploads of audio content [4][5].
When a match is identified, the platform employs checksums or perceptual hashing to confirm unauthorized use. This method complements watermarking by identifying infringements that persist even after filtering or compression. For media and entertainment companies dealing with pirated content that has been re-encoded or altered, such active monitoring bridges the gaps that watermarking alone cannot address. Additionally, proving ownership through reliable methods strengthens the overall protection strategy.
Blockchain Timestamping for Copyright Proof
Blockchain technology provides a way to establish indisputable ownership by registering an unchangeable cryptographic checksum of your watermarked content on a public ledger [4][5]. This creates tamper-proof evidence of ownership at a specific point in time, even if embedded watermarks are degraded by filtering.
ScoreDetect offers blockchain timestamping, recording cryptographic hashes of audio files to create verifiable proof of ownership. The platform also features a WordPress plugin that automatically timestamps published media. This is particularly useful for content creators, podcasters, and music producers who need to establish prior claims in infringement disputes. Unlike watermarks, blockchain timestamping operates as an independent layer of protection, serving as forensic evidence when needed.
Automated Takedown Systems
Once unauthorized content is identified and ownership is confirmed through detection and blockchain evidence, enforcement is the next critical step. Automated systems generate DMCA-style notices and send them directly to hosting providers, achieving takedown rates of over 96% [4][5]. This automation eliminates the need for manual intervention and ensures rapid response, which is crucial for combating fast-spreading piracy.
ScoreDetect integrates with over 6,000 web apps via Zapier, enabling workflows that automatically issue takedown notices as soon as matches are detected. For industries like media and entertainment – where neural codecs and filtering attacks challenge watermark durability – this swift enforcement ensures infringing copies are removed promptly, regardless of the processing they’ve undergone. The platform offers free basic protection, with premium upgrades available for advanced features, making comprehensive content protection an option for a range of budgets.
Conclusion
Filtering attacks remain a persistent challenge for audio watermarks, but their impact can be minimized by focusing on durability during the design process. By embedding watermarks within the 500 Hz to 4,000 Hz midband range, applying adversarial optimization in the time–frequency domain, and utilizing time-order–agnostic detectors with bitwise readout heads, watermarking systems can effectively resist low-pass, high-pass, and band-stop filtering. Advanced systems have demonstrated near-zero error rates under various filtering conditions, proving that robust designs can stand up to these threats [2]. This technical strength highlights the importance of embedding watermarking into a broader content protection strategy.
However, durability alone isn’t enough. Effective watermarking must be reinforced with active detection, blockchain timestamping, and automated enforcement to ensure comprehensive protection. Platforms like ScoreDetect exemplify this integration, offering a 95% success rate in web scraping, blockchain-backed proof of ownership, and a 96% takedown rate through automated DMCA notices. Such tools ensure that even if a watermark is compromised by neural vocoders or aggressive filtering, ownership verification and swift removal of infringing content remain possible.
For podcasters, music producers, content creators, and media companies facing piracy, a strong watermark is essential, but it’s only part of the solution. A complete strategy – combining durable embedding techniques with intelligent monitoring and enforcement – provides the best defense against unauthorized use. Whether you’re protecting a single piece of content or an entire digital library, leveraging advanced watermarking alongside platforms offering end-to-end protection is the most reliable way to secure your creations in an increasingly complex digital world.
FAQs
Why does equalization sometimes remove an audio watermark?
Equalization can weaken or even remove an audio watermark by altering the frequency components of the audio signal. Since watermarks rely on particular spectral characteristics to remain intact, equalization disrupts these features, making the watermark less resilient to filtering or similar processing methods.
Where should an audio watermark be embedded to survive filtering?
To ensure an audio watermark can endure filtering, it should be integrated directly into the waveform or frequency components of the audio signal. Using methods like waveform or spectrogram models can help maintain the watermark’s integrity, even when exposed to distortions like low-pass filtering or compression. This approach ensures the watermark stays intact and functional.
How can I prove ownership if the watermark gets damaged?
Proving ownership when a watermark is damaged can be tricky, but there are advanced techniques that can make it manageable. For example, neural network-based watermarks are built to resist distortions such as filtering or equalization, allowing them to remain detectable even after some damage. On top of that, blockchain technology can store a checksum of the content, essentially creating a digital fingerprint that verifies authenticity. By using both methods together, it’s possible to prove ownership even if the original watermark has been compromised.