Audio watermarking embeds hidden ownership data into audio files, allowing creators to track and protect their content. However, compression formats like MP3 and AAC often strip or distort watermarks, making them ineffective. This article outlines five methods to create watermarks that can resist compression while maintaining audio quality.
Key Methods:
- Frequency-Domain Watermarking: Embeds data in specific frequency bands that survive compression, using techniques like DCT or DWT. This often involves psychoacoustic audio watermarking to hide data within inaudible components. Balances durability with sound clarity.
- Spread Spectrum (SS): Distributes watermark data across a wide frequency range, making it resilient to compression and noise.
- Quantization Index Modulation (QIM): Integrates watermarks into the quantization process of audio, ensuring they endure compression while preserving sound quality.
- Phase Coding: Modifies the phase of audio signals, offering high audio fidelity but limited resistance to heavy compression.
- Neural Audio Watermarking: Uses AI to improve audio watermarking accuracy and adapt watermarks for compression resistance, excelling in modern distribution environments.
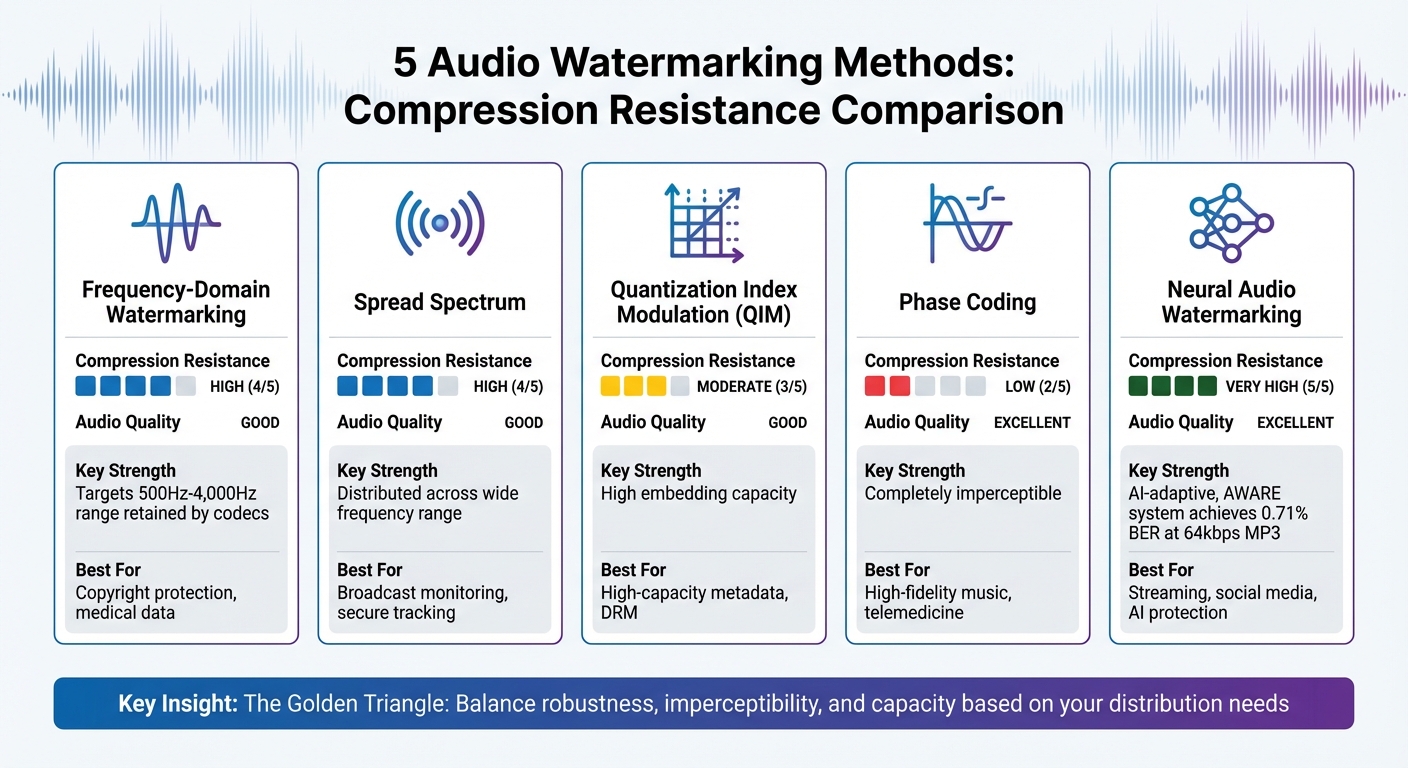
Quick Comparison
| Method | Compression Resistance | Audio Quality | Use Cases |
|---|---|---|---|
| Frequency-Domain | High | Good | Copyright protection, medical data |
| Spread Spectrum | High | Good | Broadcast monitoring, secure tracking |
| Quantization Index Modulation (QIM) | Moderate | Good | High-capacity metadata, DRM |
| Phase Coding | Low | Excellent | High-fidelity music, telemedicine |
| Neural Audio Watermarking | Very High | Excellent | Streaming, social media, AI protection |
Each method has strengths and limitations, so selecting the right one depends on your distribution needs and compression challenges.
Audio Watermarking Methods Comparison: Compression Resistance and Use Cases
Responsible AI for Offline Plugins – Tamper-Resistant Neural Audio Watermarking – Kanru Hua ADC 2024
sbb-itb-738ac1e
1. Frequency-Domain Watermarking
Frequency-domain watermarking works by embedding ownership information within an audio signal’s spectral components. This is achieved using transforms like the Discrete Cosine Transform (DCT), Discrete Wavelet Transform (DWT), or Fast Fourier Transform (FFT), which break the audio into frequency bands. The watermark is then placed in specific frequency ranges that are more likely to survive compression.
Compression Resistance
One of the key strengths of this method is its ability to withstand compression. It achieves this through midband embedding, usually targeting frequencies between 500 Hz and 4,000 Hz [2][4]. This range is crucial because it falls within the audible spectrum that compression formats like MP3 and AAC are designed to retain. In contrast, watermarking in ultrasonic frequencies – above 15 kHz – often fails, as many platforms remove these frequencies during processing [4].
In October 2025, researchers Kosta Pavlović and team introduced AWARE, a system designed to embed watermarks in the time-frequency domain. Tested on datasets like VCTK and LibriSpeech with a 16 bps payload, AWARE achieved a 0.00% Bit Error Rate (BER) under low-pass and high-pass filtering and a 0.71% BER under 64 kbps MP3 compression [2]. The system embeds data by altering Short-Time Fourier Transform (STFT) magnitudes, avoiding phase modifications, as phase-based watermarks are easily stripped out by compression without affecting audio quality [2].
Audio Quality Preservation
To ensure that the watermark remains inaudible, frequency-domain techniques rely on psychoacoustic masking models. These models calculate the "masking threshold" – the point at which sounds become imperceptible to the human ear. By embedding watermarks below this threshold, the data becomes undetectable to listeners but remains accessible to decoding systems [1].
"Oddly enough, watermarking and codecs are first cousins of each other… One says, ‘I’m going to throw it away,’ and the other says, ‘I’m going to put it in,’ and so it opens up a new class of things to think about. Who owns the under-the-blanket area?" – Dr. Barry Blesser, Director of Research at Telos Alliance [5]
This balance between robustness and transparency makes frequency-domain watermarking a powerful tool for protecting audio content.
Real-World Use Cases
Frequency-domain watermarking has found applications across various industries:
- Broadcast monitoring: Automated systems use watermarks to track when commercials or songs air on radio and TV, ensuring compliance with broadcasting agreements [1].
- Fingerprinting: Unique watermarks are embedded in digital files for each recipient, enabling content owners to trace the source of leaks [1].
- Telemedicine: Sensitive data like heartbeat sounds or ECG signals are protected during transmission and storage using watermarking techniques [1].
A 2023 study highlighted a hybrid algorithm that increased processing speed by 90% while maintaining resistance to compression attacks [3]. These advancements demonstrate the versatility and effectiveness of frequency-domain watermarking in addressing real-world challenges.
2. Spread Spectrum Watermarking
Spread Spectrum (SS) watermarking works by spreading watermark information across a wide range of frequencies rather than focusing it on specific bands. This method makes the watermark harder to remove since it’s embedded throughout the entire audio spectrum. This broad distribution contributes to its resilience against compression, as explained below.
Compression Resistance
One of the major strengths of SS watermarking is its ability to withstand MP3 and AAC compression. This is achieved through the use of pseudo-noise (PN) sequences – random patterns that distribute the watermark uniformly across the audio. These sequences blend the watermark into the signal’s noise floor, making it nearly indistinguishable from the original audio.
Compression algorithms, which aim to eliminate "perceptually irrelevant" data, leave the watermark intact because it’s embedded in areas that are difficult to separate from the core audio. Even if parts of the frequency spectrum are removed during compression, the redundancy of the spread signal ensures that enough of the watermark survives to remain functional.
SS watermarking has its roots in research by Cox et al. in the mid-1990s, which established it as a reliable method for multimedia protection. Subsequent studies have shown that using multiple orthogonal PN sequences can further enhance both the capacity and durability of the embedded watermark [1].
Audio Quality Preservation
To ensure the watermark is undetectable, its energy is kept below the human auditory threshold. By spreading the signal widely, the watermark avoids introducing noticeable noise, maintaining the audio’s original quality.
However, there’s a balancing act involved. Strengthening the watermark to improve resistance against heavy compression can risk creating audible distortions if it exceeds psychoacoustic limits. The challenge lies in fine-tuning the embedding strength to keep the watermark both inaudible and recoverable.
Resistance to Attacks
SS watermarking also holds up against deliberate attacks aimed at removing the watermark. Since it’s embedded into critical components of the audio – the parts essential for sound quality – any attempt to remove the watermark risks degrading the audio to an unacceptable level. Essentially, attackers would have to destroy the audio quality to eliminate the watermark.
The use of PN sequences adds an extra layer of security. These sequences act as cryptographic keys, making it nearly impossible to detect or isolate the watermark without knowing the specific sequence used [1]. This level of protection sets SS watermarking apart from simpler techniques like Least Significant Bit (LSB) embedding, which are easily compromised by compression.
Real-World Use Cases
The redundancy of SS watermarking makes it particularly effective for digital rights management (DRM) and fingerprinting applications. Its ability to withstand severe compression allows unique identifiers to be embedded into media files, enabling the tracking of distribution and identifying the sources of leaks across different channels. This is particularly vital for protecting live sports streams where real-time redistribution is a constant threat.
3. Quantization Index Modulation (QIM)
Quantization Index Modulation (QIM) embeds data into a signal by modifying its quantization process. This technique uses specific reconstruction points to represent watermark bits and works especially well in transform domains like the Discrete Wavelet Transform (DWT) or Singular Value Decomposition (SVD).
Compression Resistance
QIM is naturally suited for compression-heavy environments because it integrates with the quantization steps used in lossy codecs like MP3 and AAC. These codecs reduce file size by quantizing audio data, and QIM embeds watermarks directly within this process. If the distortion caused by compression stays below half of the quantization step size, the watermark can still be recovered. This built-in resilience ensures that QIM can withstand the effects of lossy compression.
"Quantization index modulation: a class of provably good methods for digital watermarking and information embedding." – Chen and Wornell [2]
One of QIM’s standout features is its ability to reject host interference. Instead of treating the original audio as noise during watermark extraction, QIM integrates the watermark as part of the signal’s structure. Adaptive QIM takes this further by adjusting the strength of the watermark based on local audio characteristics, ensuring it remains inaudible while surviving high-bitrate compression. This results in a method that not only resists compression but also maintains audio clarity.
Audio Quality Preservation
By embedding data through varied quantizers rather than adding noise, QIM ensures that audio quality remains intact. A notable variant, Dither-Modulation, employs dithered quantizers to minimize the perceptibility of quantization noise, keeping the watermark almost invisible to listeners. The size of the quantization step plays a key role here: smaller steps maintain better audio quality but may reduce robustness, while larger steps improve durability at the risk of slight audibility. Additionally, using transform domains that align with human auditory sensitivity allows QIM to conceal data in frequency ranges that are less noticeable to the human ear.
Resistance to Attacks
QIM is resilient against additive white Gaussian noise because of its quantization-based embedding. However, it can be vulnerable to desynchronization attacks like time-stretching or audio cropping, which disrupt the alignment of the quantization grids. To counter this, synchronization-invariant QIM schemes have been developed. Another advantage of QIM is its support for blind detection, meaning the original unwatermarked audio is not needed to extract the embedded data. This makes it highly practical in scenarios where the original file might not be accessible.
Real-World Use Cases
Thanks to its durability and high embedding capacity, QIM is widely used in areas like digital rights management (DRM) and content authentication. It can store more data than methods like spread spectrum watermarking, making it ideal for applications that require detailed metadata or tracking. Research has also highlighted its use in securing medical audio files and authenticating speech. For example, combining DWT-based quantization with eigenvalue techniques has proven effective in protecting speech-specific content. With its balance of compression resistance and audio fidelity, QIM remains a key tool for modern DRM and secure audio applications.
4. Phase Coding
Phase coding embeds watermarks into audio by modifying the phase of an initial audio segment to encode data. This process typically happens in the frequency domain, using tools like the Fast Fourier Transform (FFT) or Discrete Fourier Transform (DFT) to adjust the phase spectrum of the audio signal.
Audio Quality Preservation
One of the standout features of phase coding is its ability to maintain the natural sound of the audio. This is possible because the Human Auditory System is not particularly sensitive to absolute phase changes, especially in higher frequencies. As long as the relative phase between frequencies is preserved, the changes remain imperceptible to listeners.
Unlike methods that add noise (such as spread spectrum techniques) or alter amplitude (like LSB techniques), phase coding keeps the audio clean and free of distortions. It also ensures phase continuity between segments, which prevents unwanted artifacts like "clicks" or "pops" that could disrupt the listening experience. This makes it a go-to choice for high-quality audio applications, such as professional broadcasting and high-fidelity music distribution, where sound clarity is critical.
Compression Resistance
While phase coding is excellent at hiding watermarks without affecting audio quality, its resilience to compression has some limitations. Since the watermark relies entirely on the phase component, heavy lossy compression can strip away this data. However, moderate compression often preserves the relative phase relationships, allowing the watermark to be recovered. This balance between imperceptibility and compression resistance makes phase coding ideal for use cases where sound quality is a top priority.
Real-World Use Cases
Phase coding shines in scenarios demanding flawless audio quality. It’s widely employed for forensic audio watermarking for copyright protection in high-fidelity music distribution, ensuring watermarks remain invisible to listeners but detectable by automated systems. Outside of entertainment, it has found applications in telemedicine, where it helps secure sensitive audio data like heartbeat recordings, safeguarding the integrity and authenticity of medical records.
5. Neural Audio Watermarking with Adversarial Training
Neural audio watermarking takes a modern approach by using machine learning to embed watermarks into audio files. Unlike older methods that rely on fixed rules, neural networks adapt dynamically by simulating various attacks during training. This process, known as adversarial training, helps the system identify "robust domains" in the audio signal – areas that remain intact even after compression or other modifications [1]. By addressing the complexities of current compression techniques, neural watermarking enhances traditional methods.
Compression Resistance
One of the standout features of neural watermarking is its ability to balance robustness with audio quality. These systems are designed to learn how different attacks impact watermarked audio, allowing them to optimize for both durability and clarity [1].
The AWARE system (Audio Watermarking via Adversarial Resistance to Edits) showcases impressive resistance to compression. For example, under MP3 compression at 64 kbps, AWARE achieves a Bit Error Rate (BER) of just 0.71%, far outperforming WavMark (24.12%) and coming close to AudioSeal (0.24%) [2]. This means the watermark remains highly detectable even after aggressive compression that significantly reduces file size.
Audio Quality Preservation
Neural watermarking is also designed to preserve audio quality. AWARE employs level-proportional perceptual budgeting, which allows for more significant changes in louder parts of the audio while keeping modifications minimal in quieter regions. This ensures the watermark remains imperceptible to human listeners [2]. By altering only the magnitude domain and preserving the original phase, AWARE achieves a STOI score of 0.97 and a PESQ score of 4.08, maintaining excellent clarity and naturalness suitable for professional use [2].
"Watermarking is essentially a signal perturbation optimized to steer the detector’s outputs." – Kosta Pavlović, Lead Researcher, DeepMark [2]
Resistance to Attacks
Neural watermarking builds on traditional techniques by using adversarial training to improve resilience against both accidental and deliberate attacks. This training enables the system to withstand a variety of threats without becoming overly tailored to specific attack patterns – a limitation often seen in traditional deep learning watermarking systems [2].
For example, AWARE maintains a low BER of 1.61% even after resynthesis through neural vocoders like BigVGAN, which simulate scenarios such as AI voice-cloning pipelines [2]. It also holds up well against challenging conditions, including pink noise and temporal cuts caused by heavy compression.
Real-World Use Cases
Neural audio watermarking has practical applications across various industries. It plays a key role in securing audio content and identifying signs of piracy for 5G distribution, telemedicine, and IoT systems [1].
Comparison Table
Each watermarking method brings its own mix of strengths and weaknesses, balancing factors like robustness, audio quality, and data capacity. Here’s how the five methods stack up on key attributes:
| Method | Strength | Weakness | Compression Resistance | Ideal For |
|---|---|---|---|---|
| Frequency-Domain (DCT/DWT) | High robustness; works well with compression | Higher computational demands | High: Targets components retained by codecs | Copyright protection and medical data security |
| Spread Spectrum | Resistant to noise and filtering | Limited data payload | High: Hard to remove without damaging the signal | Broadcast monitoring and secure military communications |
| Quantization Index Modulation (QIM) | High embedding capacity; minimal distortion | Sensitive to gain changes and re-quantization | Moderate: Needs adaptive techniques to persist | High-capacity data hiding and stereo audio metadata |
| Phase Coding | Excellent inaudibility (completely imperceptible) | Poor robustness to signal alterations | Low: Phase changes in codecs often erase the watermark | High-fidelity audio archiving where sound quality is key |
| Neural Audio Watermarking | Extremely flexible; trainable for specific scenarios | Requires extensive training data and computational resources | Very High: Performs well when trained for adversarial compression | Compression-resistant watermarking for social media and streaming platforms |
Conclusion
Choose a watermarking method that aligns with your distribution requirements. For platforms like YouTube or social media, avoid ultrasound-based techniques since these platforms remove frequencies above 15 kHz, which can erase your watermark. Instead, opt for methods like spread spectrum or neural watermarking, as they offer strong resilience to compression, with neural approaches excelling in handling even aggressive compression methods [2].
When considering the "Golden Triangle" of watermarking – robustness, imperceptibility, and capacity – you’ll need to prioritize based on your needs [1]. For instance, frequency-domain and spread spectrum techniques provide excellent robustness, while neural watermarking is particularly effective against AI-generated deepfakes and extensive content modifications. This highlights the importance of adopting integrated protection strategies.
Your distribution environment also plays a key role. For broadcast monitoring, spread spectrum methods are highly effective due to their ability to resist noise and maintain signal integrity.
Beyond choosing the right watermarking technique, effective content protection also requires reliable management tools. ScoreDetect incorporates these advanced methods into its digital asset management system, offering invisible watermarking paired with automated monitoring and enforcement. With a 95% success rate in detecting unauthorized use through web scraping and over 96% effectiveness in takedowns, ScoreDetect empowers creators, media companies, and businesses to safeguard their digital assets. It also provides blockchain-verified proof of ownership for added security.
Tailor your watermarking strategy to address specific threats – whether casual piracy, compression on distribution platforms, or advanced AI-driven manipulation – and pair it with robust monitoring tools to ensure effective enforcement.
FAQs
Which watermarking method survives heavy MP3/AAC compression best?
The autocorrelation modulation-based audio watermarking method stands out for its ability to withstand intense MP3 and AAC compression. This approach embeds watermarks by modulating the normalized correlation between the original audio signal and a delayed version of itself. Research has shown that it performs well even under low-bit-rate compression, such as HE-AAC, while ensuring the watermark remains undetectable and supports a reasonable data payload. Additionally, transform-domain techniques, like those based on discrete wavelet and frequency-domain methods, also demonstrate considerable resilience to compression effects.
How do you keep an audio watermark inaudible but still detectable?
To make an audio watermark both undetectable to the human ear and still identifiable, psychoacoustic models are used. These models help ensure that any modifications remain below the level that humans can perceive. Methods like frequency-domain transformations, such as the Discrete Wavelet Transform, embed the watermark into less noticeable parts of the audio. The embedding strength is carefully adjusted to strike a balance – keeping the watermark resilient to compression formats like MP3 or AAC, while maintaining the overall sound quality.
What bitrate or edits usually break an audio watermark?
Audio watermarks can sometimes fail when exposed to high bitrates or particular modifications. Edits like filtering, adding noise, or using compression formats such as MP3 or AAC can weaken or completely remove the watermark, especially if the watermarking method wasn’t built to endure such alterations.