Audio watermarking embeds identifying data into audio tracks to protect intellectual property, track usage, and measure audience engagement. It’s widely used in industries like broadcasting, music production, and content creation.
Key Takeaways:
- Types of Watermarks:
- Audible: Adds recognizable sounds (e.g., "preview" voiceovers).
- Inaudible: Uses advanced techniques to embed hidden data undetectable to human ears.
- Robust: Survives file compression and format changes.
- Forensic: Tracks leaks and identifies sources.
- Dynamic: Customizes marks for real-time use.
- Core Technologies:
- Relies on psychoacoustic perceptual masking to embed data in frequencies the human ear can’t detect.
- Advanced methods ensure watermarks survive compression (e.g., MP3, AAC).
- Business Applications:
- Protects content from misuse.
- Enables audience measurement for ad revenue (e.g., Nielsen PPM).
- Tracks content leaks with unique identifiers.
- Implementation Tips:
- Test watermark resilience across codecs and workflows.
- Use tools like ScoreDetect for integration, monitoring, and automated enforcement.
Challenges:
- Compression and noise can weaken watermarks.
- Watermarking doesn’t prevent theft but aids in tracing misuse.
Audio watermarking is a critical tool for protecting digital audio assets and ensuring proper content usage. While it has limitations, pairing it with monitoring tools and robust workflows strengthens its effectiveness.
TWiRT Ep. 256 – Audio Watermarking Technology Explained 4-30-15
sbb-itb-738ac1e
How Commercial Audio Watermarking Works
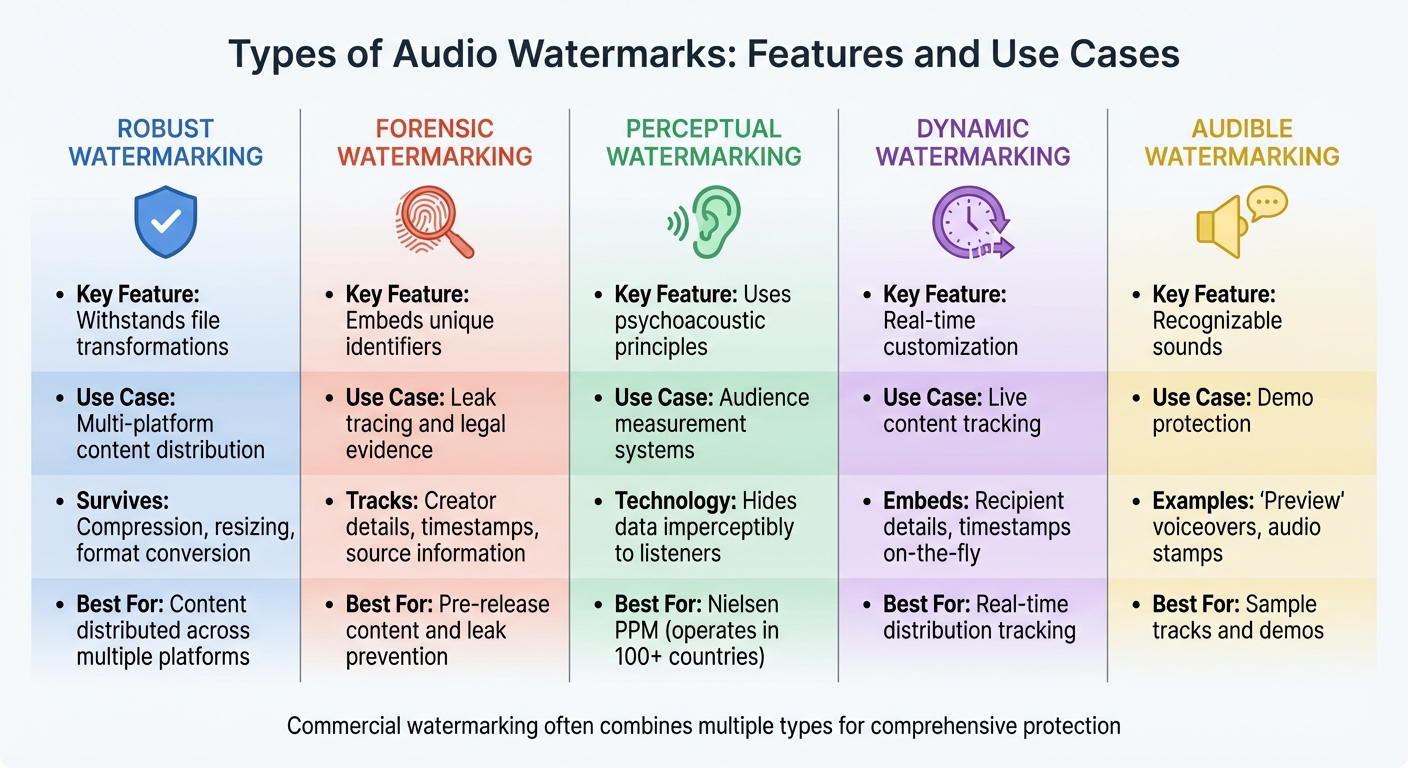
Types of Audio Watermarks: Features and Use Cases Comparison
Let’s dive into the advanced technologies and seamless integrations that make commercial audio watermarking so effective.
Core Technologies Behind Audio Watermarking
Commercial audio watermarking relies on perceptual masking techniques – a method that embeds shifted frequency tones into areas of audio where the human ear is less sensitive. This takes advantage of a phenomenon where, immediately before and after a loud sound, the ear becomes temporarily less perceptive to certain frequencies. These hidden tones can later be retrieved using specialized software[1].
Dr. Barry Blesser from Telos Alliance explains that watermarking and audio codecs, like MP3 or AAC, are closely related. While codecs aim to strip away imperceptible data to shrink file sizes, watermarking inserts data into those same imperceptible areas. To ensure watermarks survive compression and format changes, commercial systems often use advanced techniques like multi-channel, multi-level frequency-shifting keyed (FSK) encoding[1].
Telos Alliance showcased its Voltair system at NAB, highlighting its ability to detect watermarks even in challenging conditions. With over 300 units already in use, this system demonstrates the effectiveness of robust watermarking technologies[1].
These sophisticated encoding methods are tailored to fit different commercial needs, enabling a variety of watermark types.
Types of Audio Watermarks
Audio watermarks come in several forms, each serving a specific purpose:
- Robust Watermarking: Designed to withstand file transformations such as compression, resizing, or format conversion. This is critical for content that’s distributed across multiple platforms where technical modifications are unavoidable[4].
- Forensic Watermarking: Embeds unique identifiers like creator details or timestamps, making it possible to trace leaks back to their source and provide legal evidence if needed[4].
- Perceptual Watermarking: Leverages psychoacoustic principles to hide data in a way that’s imperceptible to listeners. This type is widely used in audience measurement systems like Nielsen’s PPM, which operates in over 100 countries and covers a vast majority of the global population[5].
- Dynamic Watermarking: Creates real-time, customizable marks – such as embedding recipient details or timestamps – to track content distribution effectively[4].
Integration with Digital Workflows
To protect content seamlessly, commercial watermarking systems integrate directly into digital workflows. Typically, watermarks are embedded into baseband audio tracks before final distribution or broadcast. This ensures the watermark remains intact regardless of the file format, whether it’s WAV, MPEG, or another type[5].
For large-scale operations, these systems support batch processing. Metadata such as Content ID, Distributor, and Duration can be pulled from a central CSV file and applied to multiple assets at once. In live broadcast scenarios, watermarking hardware is placed directly in the transmitter chain, enabling real-time monitoring and adjustments[1].
Once watermarking is complete, systems can generate signature files and upload them via FTP to central tracking servers. This ensures immediate synchronization with global monitoring networks. Tools like ScoreDetect take this a step further by integrating watermarking into automated workflows using Zapier, connecting with thousands of web apps to streamline protection without disrupting production processes.
Verification is the final step. Analysis tools are used to check files (like .WAV or MPEG) after encoding to confirm that watermarks are intact. As Dr. Blesser emphasizes:
"Knowledge is power. Knowledge requires tools. Knowledge requires science, and knowledge requires transparency"[1].
Choosing the Right Audio Watermarking Solution
Finding the right audio watermarking solution is about aligning technical features with your business needs. A poor choice can lead to wasted resources, workflow interruptions, or worse – leaving your content unprotected and your revenue at risk.
What to Consider When Choosing a Solution
The first step is ensuring compatibility with your current digital workflow. If you process thousands of files daily, batch processing becomes a must. Test the solution with a variety of audio files, from short jingles to lengthy podcasts, to confirm its flexibility and reliability [6].
For teams using Digital Audio Workstations (DAWs) like Adobe Audition, Pro Tools, or Audacity, seamless DAW integration is critical. Watermarking should fit naturally into the editing process, avoiding additional steps that could slow down production timelines [3].
Another key factor is how watermarks interact with audio codecs. Compression algorithms, like MP3 and AAC, often strip out data deemed unnecessary, which could include your watermark if it’s not designed to endure the encoding process. Dr. Barry Blesser, Director of Research at Telos Alliance, explains:
"Watermarking and codecs are first cousins of each other, and very often they will fight each other for this turf under the blanket. One says, ‘I’m going to throw it away,’ and the other says, ‘I’m going to put it in.’" [1]
This makes codec resilience a critical feature. Your watermark must survive compression to maintain its effectiveness [1].
For large-scale operations, command-line interface (CLI) support is essential. CLI functionality allows you to automate watermarking processes, saving time and reducing manual effort [6]. Additionally, tools with normalization features ensure that watermarks don’t cause audio clipping, especially in loud master tracks [6].
Broadcast environments add another layer of complexity. Geoff Steadman, President of 25-Seven Systems, highlights this challenge:
"The world of broadcast is the laboratory… in no way can this office approximate the complexity of the broadcast ecosystem, with all of the codecs, with all of the sound sources, with all of the formats, all the programming decisions, all the STLs, all the transmission." [1]
This underscores the need for broadcast ecosystem alignment, ensuring compatibility across the entire transmission chain, including Studio-to-Transmitter Links (STLs), processors, and hardware monitors [1].
Benefits of Using Advanced Tools Like ScoreDetect

Once you’ve identified your key requirements, tools like ScoreDetect offer a comprehensive approach to content protection.
Unlike traditional watermarking solutions that focus solely on embedding marks, ScoreDetect provides a full-spectrum protection workflow. Its invisible watermarking technology safeguards content without compromising audio quality or the listener’s experience.
What sets ScoreDetect apart is its AI-powered discovery engine, which scans the web for unauthorized usage with a 95% success rate, even bypassing common prevention measures. This means you’re not just protecting content – you’re actively monitoring for misuse. When infringement is detected, the platform provides detailed evidence and automates takedown notices, achieving a 96% success rate in removing unauthorized content.
Blockchain integration further strengthens protection. By creating a timestamped checksum of your content, ScoreDetect provides verifiable proof of ownership, a valuable tool in legal disputes.
For businesses with complex workflows, Zapier integration allows automation across thousands of apps, making it easy to incorporate ScoreDetect into existing systems. Whether you’re a podcast network, music label, or audiobook producer, the platform adapts to your needs without forcing disruptive changes.
ScoreDetect’s versatility makes it suitable for a wide range of industries, from media and entertainment to education and legal services. It scales effectively, whether you’re an independent creator or managing enterprise-level operations.
Cost and Return on Investment
The financial impact of audio watermarking goes beyond the cost of the software itself. For broadcasters, accurate audience measurement is directly tied to ad revenue. As Dr. Barry Blesser puts it:
"If you have a perfect watermarking system and no listeners, you’re off the air. If you have a zillion listeners but the advertisers think you have none, you’re off the air." [1]
Advertising revenue, often in the millions, depends on systems like Nielsen PPM detecting watermarks. If your watermarks fail to register, you risk losing revenue, even with a large audience [1].
Entry-level solutions are available at affordable prices, making professional-grade protection accessible to smaller operations. However, your budget should reflect the scale of your operations and the potential risks involved.
For creators like voice actors and producers, watermarking ensures intellectual property is protected, guaranteeing proper payment before delivering unprotected files [3].
Automation and efficiency also play a significant role in ROI. Automating watermarking for thousands of files can save significant labor costs, often recouping the investment in weeks rather than years [6].
The balance between audibility and quality is another important consideration. Over-watermarking can make audio samples less appealing to potential clients, while under-watermarking leaves content exposed. Testing your solution in real-world conditions – like noisy environments or low-quality playback devices – ensures watermarks remain effective where it matters most [1].
For larger organizations, comprehensive platforms that combine watermarking, monitoring, and enforcement can deliver measurable returns through reduced piracy, faster takedowns, and better protection of market value.
Implementation and Best Practices
Steps to Implement Audio Watermarking
To set up audio watermarking effectively, start by testing the entire broadcast chain. This means validating the watermark across every component it will interact with: codecs, Studio-to-Transmitter Links (STLs), processors, and transmission methods. As Geoff Steadman, President of 25-Seven Systems, puts it:
"In no way can this office approximate the complexity of the broadcast ecosystem, with all of the codecs, with all of the sound sources, with all of the formats… It’s a big, big ecosystem." [1]
Real-time monitoring tools are essential for verifying watermark transmission. Traditional broadcast systems often lack feedback on whether the watermark is successfully decoded. To address this, specialized hardware can analyze the watermark channel, ensuring it survives the entire transmission path [1]. Platforms like ScoreDetect take this a step further by actively monitoring for unauthorized use across the web, offering protection from encoding through enforcement.
For large-scale operations, distributing watermarking tasks across multiple processor cores can significantly improve efficiency. Studies show that using 4 cores boosts processing speed by about 70%, 8 cores achieve an 80% improvement, and 16 cores can reach a 90% improvement [7]. This is especially useful for businesses processing thousands of files daily.
By following these steps, you can ensure a smooth and efficient implementation of audio watermarking.
Best Practices for Audio Watermarking
The success of audio watermarking hinges on perceptual masking – embedding the watermark in areas where the human ear is less sensitive [1].
- Choose transform-domain algorithms: Techniques like the Discrete Wavelet Transform (DWT), Discrete Cosine Transform (DCT), or Dual-Tree Complex Wavelet Transform (DTCWT) are more resilient to processing manipulations compared to time-domain methods [7]. While these methods demand more computational resources, their durability makes them ideal for commercial use.
- Use synchronization codes: These help decoders locate watermarks even if the audio has been cropped or shifted [7].
- Focus on security: Encrypt watermark payloads using methods like chaotic maps (e.g., a modified Henon map) to prevent tampering or unauthorized access [7]. For proof of ownership, ScoreDetect’s blockchain integration creates timestamped checksums, providing legal-grade evidence without storing the audio files.
- Prioritize extraction speed: As highlighted in Scientific Reports:
"The user experience is significantly affected by the pace of watermark extraction… The imperative here is to minimize disruptions and latency issues, ensuring seamless content consumption" [7]
- Design for blind extraction: This approach eliminates the need for the original unwatermarked audio during recovery, simplifying enforcement workflows [7].
Common Challenges and Solutions
Even with careful planning, challenges are inevitable. One of the most persistent issues arises from codecs. Compression algorithms often strip away what they deem unnecessary, which can include critical watermark data [1].
Computational bottlenecks are another hurdle, especially for systems using transform-domain methods on long audio files. To address this, parallelize tasks like preprocessing, embedding, and reconstruction across multiple processor cores. For applications requiring portability, devices such as the Raspberry Pi 4B offer a compact yet powerful solution, weighing just 1.62 oz and measuring roughly 3.37 by 2.22 inches [7].
Robustness against manipulation is an ongoing challenge. Research from the University of Hawaii at Manoa identified 22 types of watermark removal attacks – including signal-level, physical-level, and AI-induced distortions – and concluded:
"None of the surveyed watermarking schemes is robust enough to withstand all tested distortions in practice" [8]
This highlights the importance of a strong initial implementation, as watermarks cannot be "patched" once deployed.
Physical-level attacks, such as re-recording audio through speakers and capturing it with a microphone, can also compromise watermark integrity. To prepare for such scenarios, test your system in real-world conditions, including noisy environments or on low-quality devices [8].
Lastly, there’s always a trade-off between fidelity and robustness. A stronger watermark may degrade audio quality, so use metrics like PESQ (Perceptual Evaluation of Speech Quality) to strike the right balance. For better detection accuracy, monitor the decision threshold. If it hovers near 0.5 – indicating random guesses – adjust the embedding strategy to improve reliability [8].
Benefits and Limitations of Commercial Audio Watermarking
Main Benefits of Audio Watermarking
Audio watermarking offers a way to embed invisible identifiers into audio content, allowing it to survive through compression, streaming, and distribution. This technology serves as a safeguard, providing legal proof of ownership. If unauthorized use occurs, these watermarks act as verifiable evidence, which is crucial for legal actions or takedown requests.
Another key benefit is revenue protection. Watermarking helps businesses identify the sources of content leaks, enabling them to take action against unauthorized distribution. This is especially important for pre-release material, exclusive recordings, or subscription-based services. For instance, in January 2024, Arup, a global engineering firm, faced a $25.6 million loss due to a deepfake attack. Watermarking can deter such fraud by signaling constant monitoring [10]. With deepfake incidents on the rise – 62% of organizations reported at least one attack in 2024–2025, and 43% faced audio-specific attacks [10] – traceable watermarks act as a deterrent for bad actors.
For organizations under regulatory scrutiny, watermarking ensures compliance with laws like California’s AI Transparency Act and the EU AI Act, which impose penalties for non-compliance [10]. Nik Kale, a principal engineer at Cisco CX Engineering, highlights its importance:
"The strongest argument for adopting watermarking is strategic readiness, building operational experience and governance muscle memory ahead of future regulatory and policy requirements" [10].
Platforms such as ScoreDetect enhance these benefits by combining invisible watermarking with active monitoring, blockchain-based proof of ownership, and automated takedown tools. These methods have achieved over 96% success rates in takedowns, effectively reducing manual enforcement efforts.
While the advantages are clear, it’s important to weigh these against the technical and practical challenges of watermarking.
Limitations to Consider
Despite its strengths, audio watermarking has its share of challenges. Its reliance on perceptual masking – embedding signals in frequencies less likely to be noticed – makes it vulnerable when audio lacks sufficient frequency energy [1]. Dr. Barry Blesser, Director of Research at Telos Alliance, describes this conflict:
"Watermarking and codecs are first cousins of each other, and very often they will fight each other for this turf under the blanket" [1].
Compression codecs like MP3 and AAC can strip away the data where watermarks are embedded, reducing their effectiveness. Environmental factors, such as background noise or poor playback conditions, can also corrupt watermark signals, making them harder to detect [1].
Spread Spectrum Audio Watermarking (SSW) is known for its durability but comes with high detection costs, making real-time recovery difficult without optimization [9]. Transform-domain methods like DWT or DCT offer better resilience but demand significant processing power, which can be a hurdle for large-scale applications.
It’s also important to note that watermarking doesn’t prevent theft – it only aids in identifying sources after the fact [9]. As Digital Cinema Initiatives puts it:
"Watermarking does not stop unauthorized recordings or their distribution, though it may deter unauthorized copying by those aware of the watermarking process" [9].
Research from the University of Hawaii at Manoa identified 22 types of watermark removal attacks, concluding that no current watermarking scheme could withstand all tested distortions [8]. Even advanced watermarks can sometimes be removed with minimal impact on audio quality, without prior knowledge of the watermarking method [11].
Jean-Claude Renaud, CEO of Winston AI, offers a balanced view:
"Watermarking makes sense as part of a broader trust and governance stack, not as a silver bullet. Implemented early, it helps businesses prepare for regulation, partner requirements and future provenance standards without scrambling later" [10].
To maximize its effectiveness, businesses should integrate watermarking into a broader protection strategy. This could include metadata standards like C2PA, post-detection tools, and clear organizational protocols.
Feature Comparison Table
The table below highlights the strengths and limitations of various watermarking technologies:
| Technology | Primary Use Case | Key Strength | Main Limitation |
|---|---|---|---|
| Spread Spectrum (SSW) | Copyright identification | Requires high-amplitude noise across all frequency bands to destroy [9] | High computational cost for detection [9] |
| PPM (Nielsen) | Audience measurement | Accurate audience measurement | Vulnerable to environmental noise and codec interference [1] |
| Cinavia | Film/Blu-ray copy protection | Robust protection on compliant systems | Requires compliant playback hardware to function [9] |
| Forensic Marking | Digital Cinema (DCP) | Enables source tracing | Does not prevent recording; only aids in tracing [9] |
| Metadata-based (C2PA) | Verifying origin and edit history | Cryptographically embedded provenance | Often stripped by re-encoding or screenshots [10] |
| Pattern-based (SynthID) | Identifying AI-generated material | More resilient to light compression | Fails with heavy editing or format changes [10] |
Conclusion
Key Takeaways
Commercial audio watermarking acts as a crucial security layer, supporting both revenue tracking and copyright protection. Using perceptual masking, it embeds inaudible watermarks that can only be detected by specialized decoders[1].
In broadcasting, watermarking plays a key role in audience measurement tools like Nielsen PPM, helping advertisers gather insights on listener demographics and engagement[1]. For creators and content owners, watermarking offers a robust defense against re-encoding, file modifications, and even recordings from streaming platforms[2].
That said, watermarking works best as part of a larger security strategy. To strengthen protection, pair watermarking with other measures like streaming-only settings, link expiration dates, and password protection[2]. When sharing sensitive audio, use unique identifiers for each recipient since public share URLs typically don’t include individual watermarks for tracking[2].
While there are technical challenges with compression codecs, the value of watermarking remains undeniable. Success depends on using the right tools, thorough testing, and clear implementation to ensure reliable protection.
Next Steps for Protecting Digital Assets
To build on these insights, the next step is adopting a comprehensive protection strategy. Audio watermarking is just one piece of the puzzle. For businesses managing digital content – whether it’s audio, video, images, or text – platforms like ScoreDetect offer advanced solutions. These include invisible watermarking, active monitoring, blockchain-based proof of ownership, and automated takedown services. With a 96% success rate in takedowns and a 95% success rate in preventing unauthorized web scraping, these tools significantly reduce the effort required for enforcement.
Identify gaps in your current security measures and regularly test watermark detectability, especially with lossy codecs or in challenging audio environments[1]. For voice-over demos, consider placing watermarks at strategic points – beginning, middle, and end. These should be audible enough to deter misuse but subtle enough to maintain audio quality[3]. As Joe Davis from VoiceActor.com wisely notes:
"Your voice is not just your art; it’s your business, and it deserves protection"[3].
Whether you’re protecting pre-release content, exclusive recordings, or subscription-based materials, don’t wait for a leak to act. Implement watermarking early, choose solutions that fit your workflow, and test their resilience across distribution channels. This preparation not only safeguards your content but also positions you to meet future regulatory demands effectively.
FAQs
Will my watermark survive MP3/AAC compression and re-encoding?
Advanced neural network methods are designed to ensure that watermarks stay intact even after MP3 or AAC compression and re-encoding. These models are trained using real-world distortions, such as compression, to produce watermarks that are both durable and virtually impossible to detect.
How can I test watermark detection across my entire workflow (DAW to distribution)?
To evaluate watermark detection effectively, it’s important to simulate real-world scenarios by introducing audio distortions. These can include compression, added noise, reverberation, polarity inversion, and time stretching. Start by embedding watermarks into your audio using your Digital Audio Workstation (DAW). Then, apply these distortions one by one and test how accurately the watermark can still be detected.
The key here is to analyze the results carefully. This allows you to fine-tune your watermarking process to make it both durable and hard to notice during playback. By repeatedly testing and refining, you can ensure the watermark remains detectable even under challenging distribution conditions.
What should I embed in a forensic watermark to trace leaks to a specific recipient?
A forensic watermark embeds a distinctive signal, like a digital fingerprint or a recipient-specific code, into the content. This makes it possible to pinpoint the source of unauthorized leaks with accuracy and dependability, linking them directly to the intended recipient.