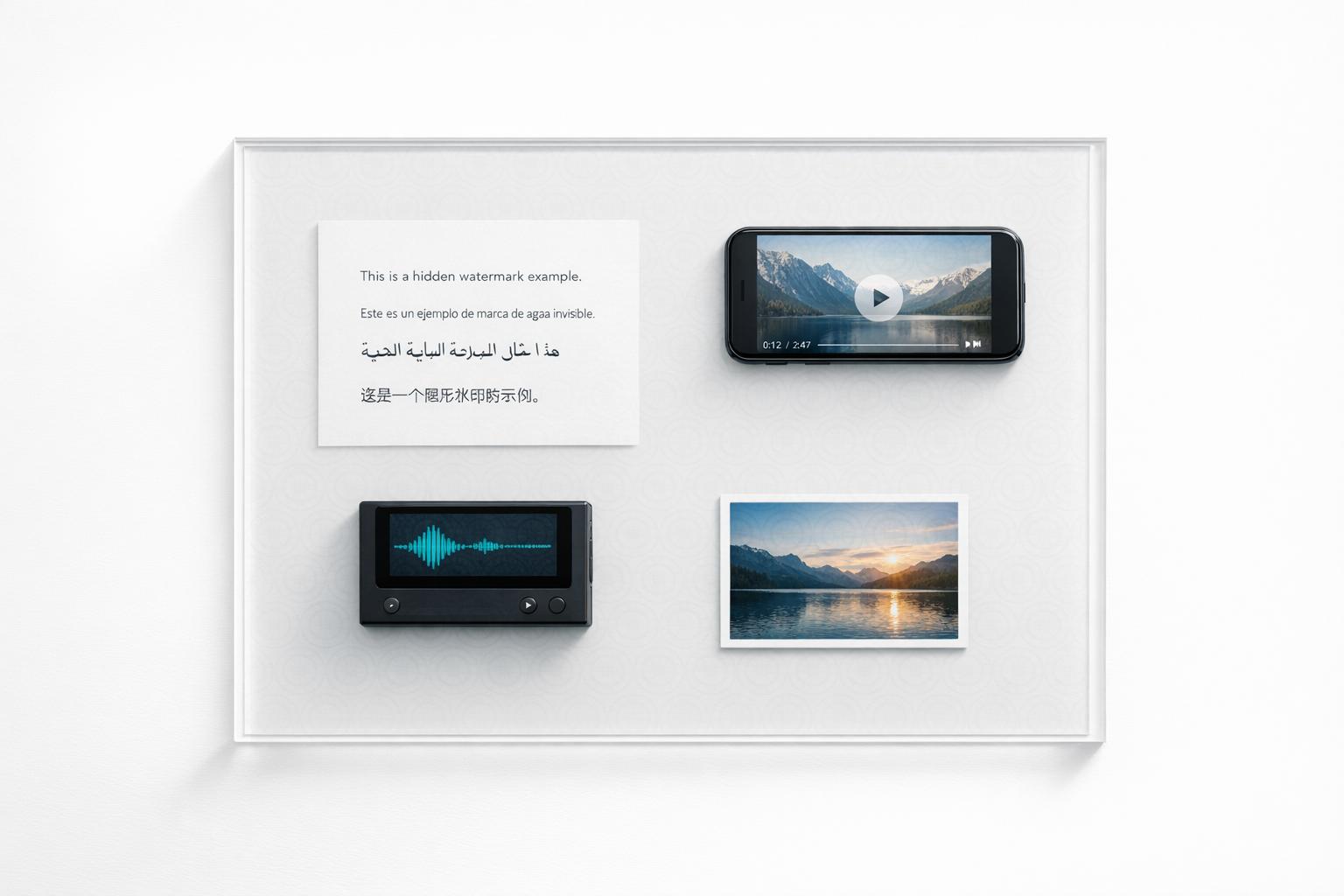
Invisible watermarking is a method to embed hidden, undetectable signals into digital content – like images, videos, or audio – without affecting their quality. Unlike visible logos or metadata, these signals can’t be easily removed and remain intact even after transformations, effectively resisting removal attacks like compression or cropping. Paired with multimodal AI, this technology offers a way to protect digital assets across various formats efficiently.
Key Takeaways:
- What it is: Embedding hidden ownership signals directly into media.
- Why it matters: Protects content from unauthorized use, even after edits or re-exports.
- How it works: AI-powered tools detect these signals without needing the original file.
- Who benefits: Industries like media, e-commerce, and content creation.
Multimodal AI ensures these watermarks stay resilient against changes, making it easier to track and verify ownership across platforms. Companies like InCyan provide tools like Tectus (blind watermarking), Idem (content matching), and ScoreDetect (blockchain-based proof) to simplify copyright enforcement and protect digital assets effectively.
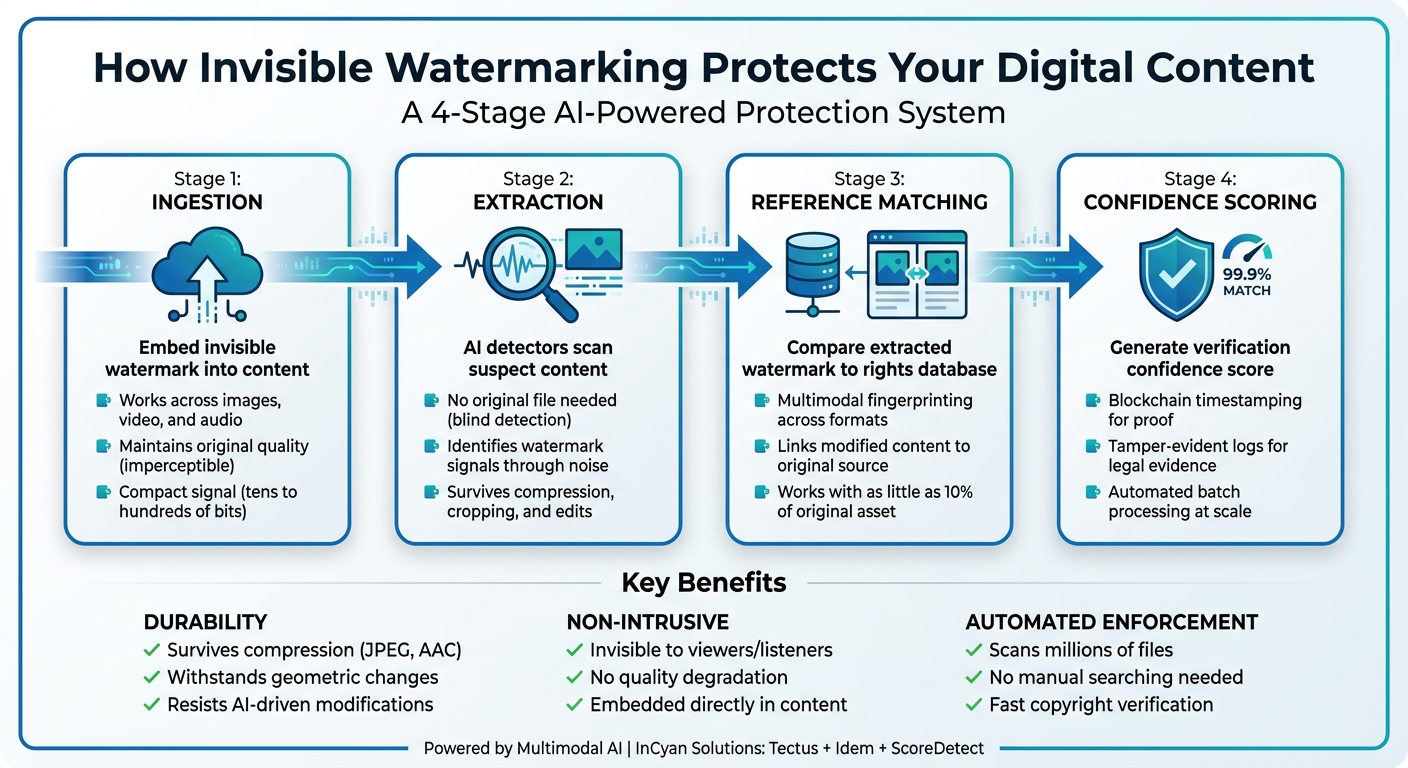
How Invisible Watermarking Works: 4-Stage Protection Pipeline
Invisible Watermarking: Content Provenance for Videos at Scale | Wes Castro, Meta
sbb-itb-738ac1e
Benefits of Invisible Watermarking with Multimodal AI
Invisible watermarking, powered by multimodal AI, offers a powerful way to protect digital content, combining durability, seamless integration, and faster enforcement. This technology addresses the challenges businesses face when their assets are altered or shared without permission. Here’s how it delivers on these critical needs.
Durability Against Alterations
One of the standout features of AI-driven watermarking is its ability to endure the numerous transformations digital content undergoes online. From cropped images to compressed videos or re-encoded audio files, invisible watermarks remain intact where traditional methods might fail. Advanced AI detectors are specifically trained to identify watermark signals even when mixed with natural or synthetic noise. They can handle changes like geometric alterations (cropping, rotation, scaling) and signal processing (JPEG compression, AAC encoding, or format changes).
For instance, AI ensures image watermarks are embedded in regions less prone to visual changes. In audio, psychoacoustic masking places signals in frequency ranges that are less noticeable to listeners. These watermarks, typically compact (ranging from tens to a few hundred bits), are spread across the content, maximizing their resilience to alterations. [1]
Non-Intrusive Content Protection
Invisible watermarking secures media without compromising its visual or auditory quality. Unlike visible logos that can disrupt the user experience or be easily removed, this technique embeds a protective signature directly into the content. This is especially important when platforms strip metadata during sharing or re-export, as the watermark remains embedded and effective.
The technology balances three key factors – imperceptibility (maintaining quality), robustness (ensuring durability), and capacity (embedding sufficient data) – to provide reliable protection while preserving the original look and feel of the media. [1]
Faster Copyright Enforcement
When unauthorized content surfaces online, speed is essential. AI-powered watermarking simplifies copyright enforcement by automating the detection and verification process across massive libraries of digital assets. Instead of manually searching for infringements, AI systems can scan millions of files on platforms like social media and peer-to-peer networks.
The process is streamlined through an automated pipeline that includes watermark extraction, matching against rights databases, and generating confidence scores for quick decisions. Integration with cryptographically verifiable ledgers adds another layer of security, creating tamper-proof logs with time stamps that support legal actions. As Nikhil John explains:
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin." – Nikhil John, InCyan
For organizations managing large content libraries, this automation reduces the need to store original files for comparison and ensures ongoing monitoring of the digital space. [1]
Use Cases for Invisible Watermarking with Multimodal AI
Invisible watermarking powered by multimodal AI is transforming how digital assets are protected across industries. By embedding ownership signals that remain intact through various transformations, this technology tackles challenges in maintaining content integrity as it circulates through platforms and workflows. These capabilities open the door to practical applications in several key sectors.
Media and Entertainment
In the fight against piracy, the media industry employs invisible watermarking to safeguard movies, TV shows, and live-streamed events. These watermarks act as a digital fingerprint embedded directly into the media itself. They endure throughout the content’s lifecycle – from initial broadcast formats to final edits, color grading, and even multi-bitrate packaging for streaming in formats like H.264 or H.265.
For video, watermarks are designed to withstand compression and structural alterations. In audio, psychoacoustic masking cleverly hides watermark signals within frequencies already obscured by louder or more complex sounds. This ensures the marks are inaudible to listeners but detectable by AI systems. The technology enables blind detection, allowing rights holders to confirm ownership of suspicious content found online without needing access to the original, unmarked master files. Multimodal fingerprinting further enhances this process by linking video highlights, audio clips, and still images back to the original source, providing robust protection across different media formats.
Digital Content Creation
Photographers, videographers, musicians, and podcasters often struggle with unauthorized use of their work. Invisible watermarking offers a solution by enabling automated copyright enforcement and ownership verification without affecting the quality of their content. These watermarks remain intact even after AI-driven transformations like inpainting, style transfer, or generative synthesis – methods that typically bypass traditional protections.
The process involves an automated four-step pipeline: ingestion, watermark extraction, payload matching, and confidence scoring. This eliminates the need for original master files and allows for batch scanning of external platforms. Additionally, integration with cryptographically verifiable ledgers creates tamper-proof logs of detection events, offering solid evidence for legal actions. This system empowers creators to retain control over their work, even in a rapidly evolving digital environment.
E-Commerce and Branding
For e-commerce brands, invisible watermarking is a powerful tool to protect product images from misuse by competitors or unauthorized sellers. These watermarks are strategically embedded in textured areas, such as fabric patterns or foliage, rather than sensitive elements like brand colors or faces, ensuring the visual appeal of the imagery remains intact. The watermarks are resilient enough to survive heavy compression and normalization processes.
Nikhil John from InCyan highlights the importance of this technology:
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." [1]
Using multimodal AI tools, brands can scan web platforms, social media, and peer-to-peer networks to detect unauthorized use of their content. By linking this back to the original works through fingerprinting and watermark detection, companies can safeguard their brand reputation while maintaining the polished, professional visuals that drive customer trust and sales.
InCyan‘s Solutions for Invisible Watermarking
InCyan offers a range of tools designed to safeguard digital assets through invisible watermarking and multimodal AI. These solutions cover every stage of content protection, from embedding ownership signals to detecting unauthorized use and providing verifiable proof of ownership. Together, they create a strong and interconnected defense system.
Tectus: Blind Watermarking Solution
Tectus is InCyan’s blind watermarking solution, which embeds invisible ownership signals directly into images, videos, and audio. Using advanced perceptual modeling, the watermarks are seamlessly incorporated, ensuring they remain invisible to viewers while still detectable by specialized systems.
The "blind" aspect is key: detectors can verify ownership using only the suspect asset and a shared secret, eliminating the need for the original unmarked file. This makes Tectus especially useful for large-scale monitoring of third-party platforms, where storing original files for all content would be unrealistic.
Tectus strikes a balance between imperceptibility, robustness, and capacity, ensuring the watermarks endure through various content modifications. It relies on quality metrics like Peak Signal to Noise Ratio (PSNR) and Structural Similarity Index (SSIM) to maintain content quality. The watermarks are designed to withstand challenges such as lossy compression (e.g., JPEG, AAC), geometric alterations (cropping, rotation, scaling), and even the heavy transcoding often seen on social media platforms.
Idem: Evasion-Proof Matching
Working alongside Tectus, Idem enhances content identification by ensuring resilience against extensive modifications. This multimodal fingerprinting platform is built to handle transformations that would typically bypass traditional methods, including AI-based inpainting, style transfers, frame interpolation, and synthetic edits that retain only fragments of the original content.
Idem’s capabilities are remarkable – it can verify ownership even when as little as 10% of the original asset remains intact. It also bridges media types, connecting ownership claims across images, videos, and audio, regardless of how they are distributed.
The platform automates the verification process, enabling large-scale detection without manual intervention. This allows for efficient batch scanning of external platforms to identify unauthorized usage quickly and accurately.
ScoreDetect: Blockchain Timestamping for Enhanced Security
ScoreDetect introduces a cryptographic layer to InCyan’s protection suite by using blockchain timestamping. Instead of storing media files, the system captures checksums and creates tamper-evident, time-stamped logs that document how evidence was collected, who accessed it, and for what purpose.
This method allows rights holders to independently prove ownership and licensing status without exposing proprietary algorithms or the media itself. ScoreDetect generates verifiable certificates that can be shared with partners, regulators, or legal authorities, ensuring a clear and defensible chain of custody. As InCyan explains:
The result is a time stamped, tamper evident log that can be shared with partners and regulators while keeping underlying media and proprietary algorithms under strict control. [1]
ScoreDetect also integrates seamlessly with over 6,000 web apps via Zapier and includes a WordPress plugin. This plugin automatically timestamps every published or updated article, embedding proof of ownership into the blockchain. This feature highlights its role as a key component of InCyan’s comprehensive protection system.
Challenges Addressed by Multimodal AI in Watermarking
Traditional watermarking systems face hurdles when content undergoes modifications, when managing massive libraries, or when detection systems mistakenly flag legitimate files. Multimodal AI steps in to tackle these issues by understanding how watermarks behave in real-world scenarios and adapting to various transformations. Let’s break down how it addresses these challenges.
Durability Against Modifications
One of the toughest challenges for watermarking is ensuring that watermarks remain intact after content is altered. Whether it’s cropping, compression, style changes, or even AI-driven edits like inpainting or background replacement, maintaining watermark integrity is critical. Multimodal AI trains detectors to identify watermark signals even after heavy processing, isolating them from both natural and synthetic noise.
As Nikhil John of InCyan explains:
AI assisted detectors learn to separate watermark signals from natural and synthetic noise under ever more aggressive transformations. [1]
Techniques like transform domain embedding further enhance durability by enabling watermarks to survive lossy compression and format changes, ensuring the signals can still be recovered even after extensive modifications [1].
Handling Large Content Libraries
For platforms managing billions of assets, storing every unmarked version of uploaded content is simply not feasible. Blind watermarking offers a solution by allowing detection with just the suspect file and a shared secret, removing the need to retain unwatermarked originals.
As Nikhil John points out:
Blind watermarking removes that dependency [on the original file]. In a blind scheme, the detector only needs the suspect asset and a shared secret… For platforms, this is essential. They cannot store every unwatermarked version of every upload for comparison. [1]
AI-powered batch processing also speeds up detection, enabling platforms to handle massive libraries efficiently by running verification processes in parallel and integrating with existing encoding systems.
Reducing False Positives
Accuracy is as important as scalability. Multimodal AI reduces false positives by using confidence scoring and reference matching to verify watermark signals. A four-stage pipeline – covering ingestion, extraction, reference matching, and confidence scoring – ensures that artifacts from compression or natural noise aren’t mistaken for watermarks. Additionally, multimodal fingerprinting links modified content back to its original forms across various media types, providing an extra layer of validation.
Nikhil John highlights the need for rigorous verification:
Without [an end-to-end verification pipeline and a defensible chain of custody], even technically excellent watermarking risks being dismissed in operational or legal settings. [1]
To further ensure reliability, organizations are advised to audit detection thresholds, maintain cryptographic hashes, and log detection events immutably. This approach helps ensure results stand up to scrutiny in both operational and legal contexts.
Conclusion
Invisible watermarking powered by multimodal AI offers a durable, non-intrusive, and efficient way to enforce copyright in a world where digital content is constantly transformed and automated metadata stripping is the norm. Unlike older systems that rely on labels easily removed or altered, invisible watermarks act as a hidden identifier, embedded directly into the media itself. These watermarks can withstand re-exports, compression, and even AI-driven modifications, making them a reliable tool for protecting digital assets.
As Nikhil John of InCyan puts it:
Invisible digital watermarking is not a silver bullet, but it is a powerful control point in a world of frictionless copying and synthetic media. [1]
This approach provides a multi-layered defense against digital piracy. InCyan’s suite of tools supports the entire protection process. Tectus uses blind watermarking to enable large-scale detection without requiring access to the original files. Idem ensures evasion-proof matching across various media formats, even when only fragments of the content remain. Finally, ScoreDetect secures the process with tamper-evident blockchain logs, offering legally defensible proof of ownership and detection events.
The real strength lies in how these tools work together. By embedding ownership, linking modified content to its source, and creating an immutable record, this four-stage system – ingestion, extraction, reference matching, and confidence scoring – provides comprehensive protection. It ensures businesses can safeguard their assets across all channels, from social media to professional broadcasting.
For industries like media, entertainment, e-commerce, and marketing, where managing large content libraries is a daily challenge, the pressing question isn’t whether to adopt this technology but how quickly it can be implemented.
FAQs
Can invisible watermarks survive cropping and compression?
Properly designed invisible watermarks are capable of withstanding challenges like cropping and compression. Advanced techniques, such as frequency domain embedding, help ensure the watermark stays intact even after these types of modifications.
How does blind watermark detection work without the original file?
Blind watermark detection involves embedding a hidden, durable signal into media that remains invisible but can be identified and verified later using specific tools. This method is effective even if the media undergoes changes, and it doesn’t rely on having the original file for comparison.
What proof can I use to enforce my copyright?
Embedding invisible digital watermarks into your media files – whether they’re images, videos, audio, or documents – can help protect your copyright. These watermarks are hidden, machine-readable signals that viewers can’t see but can still be detected later, even if the file has been compressed or edited.
Pairing invisible watermarking with blockchain technology takes it a step further. Blockchain creates a secure, unchangeable record of ownership, providing solid evidence to back up your copyright claims during disputes or enforcement actions.