Invisible watermarking embeds undetectable, machine-readable signals into media files like images, videos, and audio. These signals help prove ownership, track usage, and protect intellectual property without affecting the quality of the content. Unlike visible watermarks or metadata, invisible watermarks remain intact even after compression, resizing, or re-encoding.
Key Benefits:
- Ownership Proof: Serves as reliable evidence in disputes.
- Durability: Survives edits, AI modifications, and social media compression.
- Quality Preservation: Protects content without visible or audible distortions.
How It Works:
- Embedding Methods: Uses transform or spatial domain techniques to hide data in textured areas or masked frequencies.
- Detection: Blind detection tools verify watermarks without needing the original file.
Invisible watermarking is increasingly vital as generative AI and synthetic media evolve, providing a safeguard when metadata is stripped or altered. Tools like InCyan’s Tectus and ScoreDetect offer scalable solutions for businesses to monitor and protect their media assets effectively.
Invisible Watermarking: Content Provenance for Videos at Scale | Wes Castro, Meta
sbb-itb-738ac1e
How Invisible Watermarking Works
How Invisible Watermarking Works: Embedding and Detection Process
Invisible watermarking tweaks the structure of media files in a way that’s invisible to the human eye but detectable by machines. It works by embedding data in areas of a file where small changes won’t be noticed. This clever approach ensures the quality of the media remains intact – a critical feature in an era of AI-generated and synthetic content.
Embedding Data into Media Files
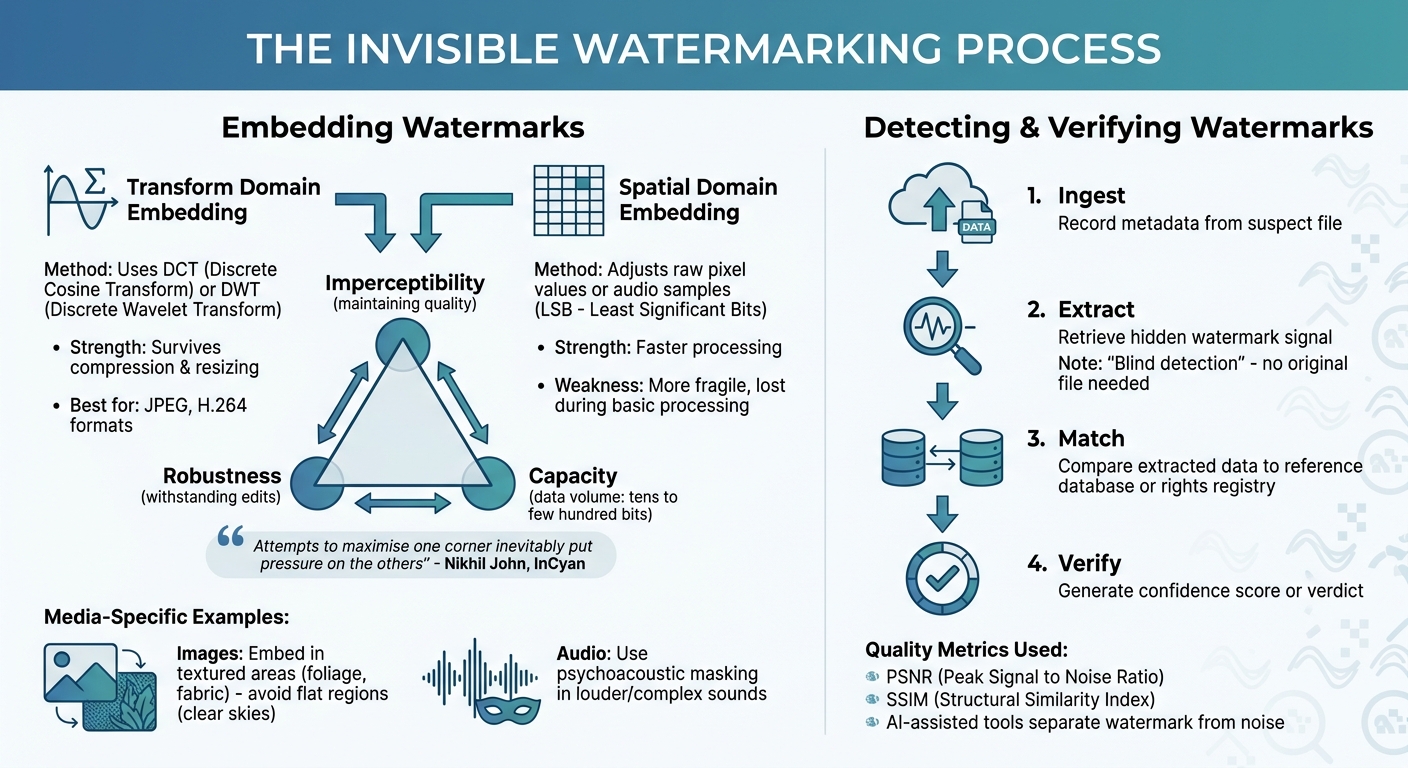
To embed watermarks, systems rely on perceptual models that identify the best places to hide data. For example:
- Images: Watermarks are inserted into textured areas like foliage or fabric, avoiding flat regions like clear skies where changes are more obvious.
- Audio: Psychoacoustic masking hides watermark signals within louder or more complex sounds, making them practically undetectable to listeners.
Two main methods are used for embedding:
- Transform domain embedding: This involves altering mathematical coefficients using techniques like the Discrete Cosine Transform (DCT) or Discrete Wavelet Transform (DWT). Because this method aligns with how formats like JPEG or H.264 compress data, it helps the watermark survive compression or resizing.
- Spatial domain embedding: Here, raw pixel values or audio samples are adjusted, often by tweaking the Least Significant Bits (LSBs). While this method is faster, it’s more fragile and can be lost during basic processing.
The challenge is finding the right balance between three factors: imperceptibility (maintaining quality), robustness (withstanding edits or attacks), and capacity (how much data can be embedded). As Nikhil John from InCyan points out:
"Attempts to maximise one corner [of the watermarking triangle] inevitably put pressure on the others" [1].
To avoid compromising the media experience, most systems embed small payloads – typically tens to a few hundred bits. This provides enough information to verify ownership while keeping the watermark invisible. Once embedded, specialized tools can extract this hidden data for verification purposes.
Detecting and Verifying Watermarks
Modern watermarking systems often use "blind" detection, meaning they don’t need the original file to identify and verify the watermark. Instead, the process works with just the suspect file and a shared secret or reference parameters, making it ideal for managing large libraries of content.
Detection typically follows four steps:
- Ingesting the suspect file: Metadata is recorded for analysis.
- Extracting the watermark: The hidden signal is retrieved from the media file.
- Matching the data: The extracted information is compared to a reference database or rights registry.
- Producing results: A confidence score or verdict is generated based on how clearly the watermark was detected.
AI-assisted tools are increasingly stepping in to separate watermark signals from background noise, especially in cases where the content has been heavily edited or altered by generative AI. Metrics like Peak Signal to Noise Ratio (PSNR) and Structural Similarity Index (SSIM) help measure how much the media’s structure has changed, reflecting how humans might perceive those changes.
This advanced detection ensures that even if content is modified, redistributed, or stripped of metadata, rights holders can still prove ownership and monitor unauthorized use across digital platforms.
Benefits of Invisible Watermarking
Invisible watermarking offers a discreet way to protect media without interfering with the user experience. While visible logos can be cropped out and metadata easily removed during re-export, invisible watermarks integrate directly into the media itself. These hidden identifiers stay intact through processes like format conversion, resizing, and even social media compression. This makes them a powerful tool for safeguarding content.
Preventing Unauthorized Use
Invisible watermarking provides a durable layer of protection against misuse. Unlike visible marks that disappear once downloaded, invisible watermarks remain embedded in the media – even after AI-based editing or other modifications. This resilience acts as a strong deterrent to unauthorized use.
Rights holders can leverage blind detection methods to scan third-party platforms and social media for their content, without needing access to the unmarked original file. If unauthorized copies surface, the embedded watermark serves as a clear link to the source, making it much harder for infringers to deny responsibility or ownership.
Legal Proof of Ownership
In cases of disputes, invisible watermarks serve as compelling evidence of ownership. Many international copyright frameworks now recognize watermarking as an effective technological safeguard for rights protection. These watermarks create an unalterable, time-stamped trail that can be used to verify content origin.
As InCyan highlights, when metadata is stripped away, an invisible watermark remains the last reliable connection to the original creator. This is particularly critical in today’s landscape, where generative AI can produce synthetic media and platforms frequently remove metadata. In such scenarios, the watermark becomes the definitive proof of ownership.
Maintaining Quality and User Experience
One of the most appealing aspects of invisible watermarking is its ability to protect media without compromising quality. Using perceptual models, advanced systems embed watermark data in areas that are less noticeable to human senses – such as textured parts of an image or masked audio frequencies. Metrics like Peak Signal-to-Noise Ratio (PSNR) and Structural Similarity Index (SSIM) ensure that the watermarking process does not create visible or audible distortions.
"The goal is not to hide a watermark completely from dedicated forensic analysis, but to ensure that the audience experiences the content as intended." – Nikhil John, InCyan [1]
This approach ensures that your creative work remains untouched by distracting logos or quality degradation. Viewers and listeners can enjoy the content exactly as it was meant to be experienced, without any interruptions or compromises.
How to Implement Invisible Watermarking
Adding invisible watermarks to your media isn’t as complex as it might sound, but it does require thoughtful planning. The key steps involve picking the right tools, preparing your files, and ensuring the watermarks can withstand challenges like social media compression or format changes.
Step 1: Select Your Watermarking Tools
When choosing a watermarking tool, focus on three things: how hard the watermark is to detect, how well it holds up under stress (like compression), and how much information it can carry. Tools with blind detection – the ability to verify a watermark without needing the original file – are particularly useful, especially if you’re managing a massive media library across multiple platforms [1]. For instance, InCyan’s Tectus supports blind detection and works with a variety of content types, including images, videos, audio, and documents, making it a solid option for businesses handling diverse media.
If your content will be shared on social media, look for tools that use transform domain techniques, as they embed watermarks in ways that are more likely to survive compression and re-encoding.
Step 2: Prepare Your Media Files
After selecting a tool, the next step is to get your files ready. Start with high-resolution master files or high-quality mezzanine videos. These provide enough detail to embed watermarks without introducing visible distortions [1][3]. Group your files by type since each type requires a different embedding approach.
Before embedding, establish quality benchmarks using metrics like Peak Signal to Noise Ratio (PSNR) and Structural Similarity Index (SSIM). These help confirm that the watermarking process doesn’t compromise the quality of your content [1]. It’s also important to map your distribution pathways. Will your videos be compressed by Facebook? Will your images be cropped for Instagram Stories? Knowing these details helps you adjust the watermark strength to ensure it survives these changes.
For better concealment, identify areas in images or audio where the watermark signal can be hidden effectively, such as masking regions in images or complex frequencies in audio [1]. Keep in mind that simple files, like plain ASCII text documents, don’t have enough "extra space" to hide watermarks invisibly [3].
Step 3: Apply and Verify Watermarks
When embedding the watermark, use perceptual modeling techniques to hide it in areas where human senses are least likely to notice. The watermark itself is typically small – just tens to a few hundred bits – enough to encode a unique identifier but not large amounts of information like full contracts [1].
Once the watermark is embedded, it’s vital to test it. Follow a four-step process: ingest the watermarked file, extract the watermark using blind detection, match it against a database, and score its confidence level [1]. Make sure to test the watermark’s resilience by subjecting it to common transformations like social media compression [1][3].
"A watermark that disappears after a single round of social media transcoding or minor colour correction does not help rights holders." – Nikhil John, InCyan [1]
In addition to automated tests, conduct manual inspections to catch artifacts that automated tools might miss [2]. For legal purposes, maintain a chain of custody by logging timestamps, cryptographic hashes, and detection results. This documentation can be crucial if you need to establish ownership of digital media in court [1].
Once applied and verified, solutions like InCyan’s Tectus can further strengthen your media protection efforts.
Using InCyan Solutions for Media Protection
InCyan brings together media protection under four key pillars – Discovery, Identification, Prevention, and Insights – to create a defense system that detects, verifies, and acts against unauthorized use across the web. Here’s how each solution leverages invisible watermarking to safeguard your digital assets.
How ScoreDetect Protects Your Content

ScoreDetect takes InCyan’s invisible watermarking a step further by incorporating blockchain timestamping and AI-driven content management. When you upload content, ScoreDetect generates a cryptographic checksum of your file and records it on the blockchain. This creates a tamper-proof timestamp that strengthens legal ownership claims without storing the actual media files.
The platform’s AI simplifies protection by combining multiple layers of defense:
- Invisible watermarking prevents unauthorized use.
- Web scraping identifies infringing content with a 95% success rate.
- Quantitative verification confirms violations.
- Automated delisting achieves a 96% takedown rate.
These features work together to safeguard ownership, even when media undergoes alterations. Additionally, ScoreDetect integrates with over 6,000 web apps through Zapier, allowing you to design automated workflows that align with your existing content management systems.
"Many organizations now complement traditional evidence management systems with cryptographically verifiable ledgers inspired by blockchain designs." – Nikhil John, InCyan [1]
Enterprise Features for Business Protection
InCyan also offers advanced tools tailored for enterprise-level protection. Tectus embeds invisible, machine-readable watermarks into all types of media. These watermarks are resistant to transformations such as cropping, rotation, compression, noise reduction, and even AI-driven edits like inpainting and style transfer. Using blind detection, Tectus can retrieve watermarks without needing the original unmarked file, making it ideal for monitoring large volumes of assets across third-party platforms.
For more complex scenarios, Idem uses multimodal matching to identify ownership, even when only 10% of the original content remains visible. This solution excels at detecting assets altered by mobile edits, memes, cropping, or compression – situations where traditional metadata fails. To enforce protection quickly, Indago combines high-speed search capabilities with forensic precision, de-indexing infringing links in under an hour. By targeting piracy at its source, Indago ensures swift action.
Together, these tools maintain media quality while preserving legal proof of ownership, even after significant transformations. They offer businesses a robust system for large-scale protection.
Common Challenges and How to Solve Them
Even with advanced techniques, watermarking faces hurdles when media undergoes transformations. Building on earlier discussions about embedding methods, these challenges underscore the difficulty of preserving watermark integrity across diverse scenarios.
Keeping Watermarks Intact
One of the toughest tasks is ensuring that watermarks survive common media transformations like cropping, compression, format changes, or platform-specific adjustments. Each of these processes can weaken or even erase the embedded watermark.
The challenge lies in striking a balance. As Nikhil John from InCyan puts it:
"A watermark that tries to carry too much data becomes fragile and easier to detect visually or audibly." [1]
Using transform domains like the Discrete Cosine Transform (DCT) or Discrete Wavelet Transform (DWT) can make watermarks more resistant to transcoding. For images, embedding in textured areas keeps them less noticeable, while in audio, psychoacoustic masking hides signals in frequencies already dominated by louder sounds.
However, modern AI-driven edits – such as inpainting, style transfer, or background replacement – pose new threats by potentially erasing traditional watermarks. To address this, adaptive embedding strategies tailor the watermark to the content, ensuring it remains intact even after significant modifications.
Balancing Protection and Usability
Another critical challenge is maintaining media quality while embedding watermarks. If the watermark introduces visible artifacts, audio distortion, or bloats file sizes, it can degrade the viewing or listening experience.
Perceptual modeling helps by embedding watermarks in less noticeable areas. For video, this means avoiding flat gradients and placing signals in motion-heavy or textured regions. In audio, embedding data in masked frequencies ensures clarity. As Nikhil John explains:
"The goal is not to hide a watermark completely from dedicated forensic analysis, but to ensure that the audience experiences the content as intended." [1]
Blind listening or viewing tests with test audiences help confirm that watermarks remain imperceptible during normal use.
For large-scale applications, blind detection is essential. It enables watermark verification without needing the original file, which simplifies operations and reduces the need to store master copies. InCyan’s tools, like Tectus and Idem, leverage blind detection to monitor content across third-party platforms, recovering watermarks using shared secrets or reference parameters.
A hybrid approach offers another solution. By combining a low-rate, highly durable watermark embedded in a transform domain with a higher-capacity but more fragile watermark in the spatial domain, this method balances resilience against aggressive processing with the ability to embed enough data for effective tracking and enforcement.
Conclusion
Invisible watermarking stands out as a powerful tool for protecting digital media, offering a layer of security that goes beyond traditional methods like visible logos or metadata. While visible logos can be cropped and metadata is often stripped during re-export, invisible watermarks are embedded directly into the media’s signal. This ensures they remain intact even after transformations like social media uploads, format changes, or AI-driven edits.
As generative AI and synthetic media grow more advanced, the need for this kind of protection becomes even more pressing. When platforms disregard or remove provenance metadata, invisible watermarks provide a dependable way to trace content back to its origins and verify licensing. Beyond just safeguarding assets, this technology offers businesses additional advantages: it maintains the quality of media through perceptual modeling, serves as legally admissible proof of ownership, and enables large-scale verification across billions of assets without requiring access to the original files.
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." – Nikhil John, InCyan [1]
InCyan enhances digital media protection through a comprehensive strategy built on four pillars: Discovery (tracking usage), Identification (connecting usage to original assets using tools like Idem), Prevention (embedding watermarks with Tectus), and Insights (converting watermark data into actionable intelligence). For those interested in combining blockchain timestamping with watermarking, ScoreDetect provides an easy-to-use solution with developer-friendly APIs and WordPress integration. Meanwhile, Tectus offers enterprise-grade watermarking for images, videos, and audio, ensuring robust protection across various formats.
"Invisible digital watermarking is not a silver bullet, but it is a powerful control point in a world of frictionless copying and increasingly sophisticated synthetic media." – Nikhil John, InCyan [1]
FAQs
Can an invisible watermark survive AI edits and social media compression?
Yes, an invisible watermark can endure AI edits and the compression applied by social media platforms when it’s embedded within the media’s frequency components. This approach ensures the watermark stays intact, even after processes like compression or other alterations.
What should I embed in a watermark – an ID, owner info, or a license link?
When adding a watermark, it’s important to include details that can clearly identify and verify the content without interfering with the viewer’s experience. Commonly, this involves embedding owner identification or ownership details, as these help establish clear rights and trace the content’s origin. Although embedding a license link is possible, it’s less frequently done. Invisible watermarks are more about embedding tamper-resistant data for later verification rather than offering direct access to licensing terms.
How can I verify a watermark without the original file?
You can confirm a watermark’s presence without needing the original file by examining the hidden data embedded in the media. Invisible watermarking involves placing concealed information within files like images, videos, or audio. Specialized tools can then extract and verify this data directly from the media. This process ensures the file’s authenticity and ownership, even if it has undergone changes like compression or resizing.

