Invisible watermarking is a powerful way to protect digital content, especially as deepfake technology becomes harder to detect. Unlike visible watermarks, these hidden markers are embedded directly into media files and remain intact even after edits like cropping or compression, effectively resisting removal attacks. They help verify content authenticity, track misuse, and detect tampering.
Key points:
- How it works: Invisible watermarks embed hidden digital signatures into images, videos, or audio without affecting quality.
- Deepfake challenge: As deepfakes grow more realistic, they pose risks like spreading false information and financial fraud.
- Industry use: Media, healthcare, and legal sectors use invisible watermarking to protect assets and ensure content integrity.
- Advanced methods: Techniques like neural watermarking and blockchain integration enhance durability and security.
Invisible watermarking is essential for safeguarding digital assets in an era where fake content can easily deceive. By embedding hidden identifiers, it provides a reliable way to trace origins and detect manipulations.
Securing Videos with Invisible Watermarking
sbb-itb-738ac1e
How Invisible Watermarking Fights Deepfakes
With deepfakes becoming a growing concern, invisible watermarking offers a way to safeguard and validate digital content. By embedding unique, hidden identifiers into images and videos, this technique creates a digital safety net. These markers allow content creators to trace ownership and identify unauthorized changes – even after the content has been compressed, resized, or shared across various platforms [1][2].
Protecting Digital Content
Forensic watermarks embedded in digital assets , such as forensic audio watermarking for sound files, remain intact through common manipulations, enabling platforms like social media networks or video-on-demand services to verify content authenticity and track leaks back to their source [1][2]. For instance, some video-on-demand services use A/B forensic watermarking, which assigns a unique identifier to each viewer. If leaked content surfaces online, the watermark can reveal the account responsible. Similarly, some deepfake creation tools embed creator information during the generation process, maintaining a traceable chain from origin to distribution [1].
In addition, blockchain technology adds another layer of security. By recording a cryptographic checksum of the watermarked content (without storing the actual file), blockchain ensures tamper-proof records of ownership and modifications. This system provides concrete evidence of unauthorized use and supports automated takedown processes, which have achieved a success rate exceeding 96% [context].
These measures not only protect digital assets but also pave the way for detecting tampering more effectively.
Detecting Deepfake Changes
Beyond protection, invisible watermarking plays a crucial role in identifying deepfake manipulations. The effectiveness of detection relies on the durability of the embedded digital signatures. Semi-fragile watermarks, for example, can withstand minor, benign edits but break under malicious changes, signaling tampering [4][5]. Transform domain watermarking (TDW) embeds markers into frequency-transformed coefficients, offering resistance to geometric attacks while still exposing alterations [4].
However, no system is completely foolproof. Tools like UnMarker can remove watermarks by distorting pixel frequencies, achieving over a 50% success rate even without knowing the specifics of the watermarking method [3]. Despite these challenges, invisible watermarking remains a powerful tool for tracking content origins and detecting tampering, making it significantly harder to distribute deepfakes undetected.
Technologies and Methods in Invisible Watermarking
Modern invisible watermarking techniques have come a long way, striking a balance between being undetectable, durable, and efficient. These advancements are vital in combating tools designed to strip away embedded markers, especially in the age of deepfake manipulation [7].
Watermark Embedding Methods
One of the standout approaches today is AI watermarking. A prime example is InvisMark, unveiled at the IEEE/CVF Winter Conference on Applications of Computer Vision (WACV) in February 2025. This cutting-edge system uses neural networks to embed 256-bit watermarks into high-resolution, AI-generated images. The results are impressive: a Peak Signal-to-Noise Ratio (PSNR) of around 51 and a Structural Similarity Index (SSIM) of 0.998, ensuring the watermark remains invisible. Even after multiple manipulations, InvisMark retained over 97% bit accuracy [6].
"By combining high imperceptibility, extended payload capacity, and resilience to manipulations, InvisMark provides a robust foundation for ensuring media provenance in an era of increasingly sophisticated AI-generated content." – IEEE [6]
Another method, perceptual modulation, embeds watermark data in areas where human perception is less sensitive. For example, textured regions in images or masked frequencies in audio files are ideal spots. This technique ensures the watermark remains hidden while increasing its resistance to tampering.
Transform domain embedding is another powerful approach. Instead of altering raw pixels, it modifies frequency coefficients using methods like Discrete Cosine Transform (DCT) or Discrete Wavelet Transform (DWT). Since these techniques align with how formats like JPEG and H.264 compress data, they make watermarks more resilient to compression and filtering.
Modern systems also utilize blind detection, which allows watermarks to be recovered using only the suspect file and a shared secret, eliminating the need for the original file [7]. Together, these methods form a robust framework for protecting digital content.
Blockchain Integration for Added Security
Invisible watermarking gets an extra layer of security when paired with blockchain technology. Blockchain ensures tamper-proof records by storing cryptographic checksums – essentially digital fingerprints of the content – rather than the files themselves. This approach verifies authenticity without requiring extensive storage.
For instance, ScoreDetect uses blockchain to log checksums of watermarked content, creating a time-stamped chain of custody. This system supports legal recourse and automates takedown workflows, boasting success rates exceeding 96%. The immutable nature of blockchain makes it nearly impossible for malicious actors to dispute ownership or misuse stolen content.
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." – Nikhil John, InCyan [7]
This combination of invisible watermarking and blockchain is particularly valuable for organizations managing sensitive digital assets. Whether it’s media companies protecting unreleased footage or healthcare providers safeguarding medical imagery, these technologies offer immediate detection capabilities and long-term legal security. Together, they form the backbone of enterprise-level digital asset management systems.
ScoreDetect: Enterprise Digital Content Protection

How Invisible Watermarking Works: 4-Stage Framework for Digital Content Protection
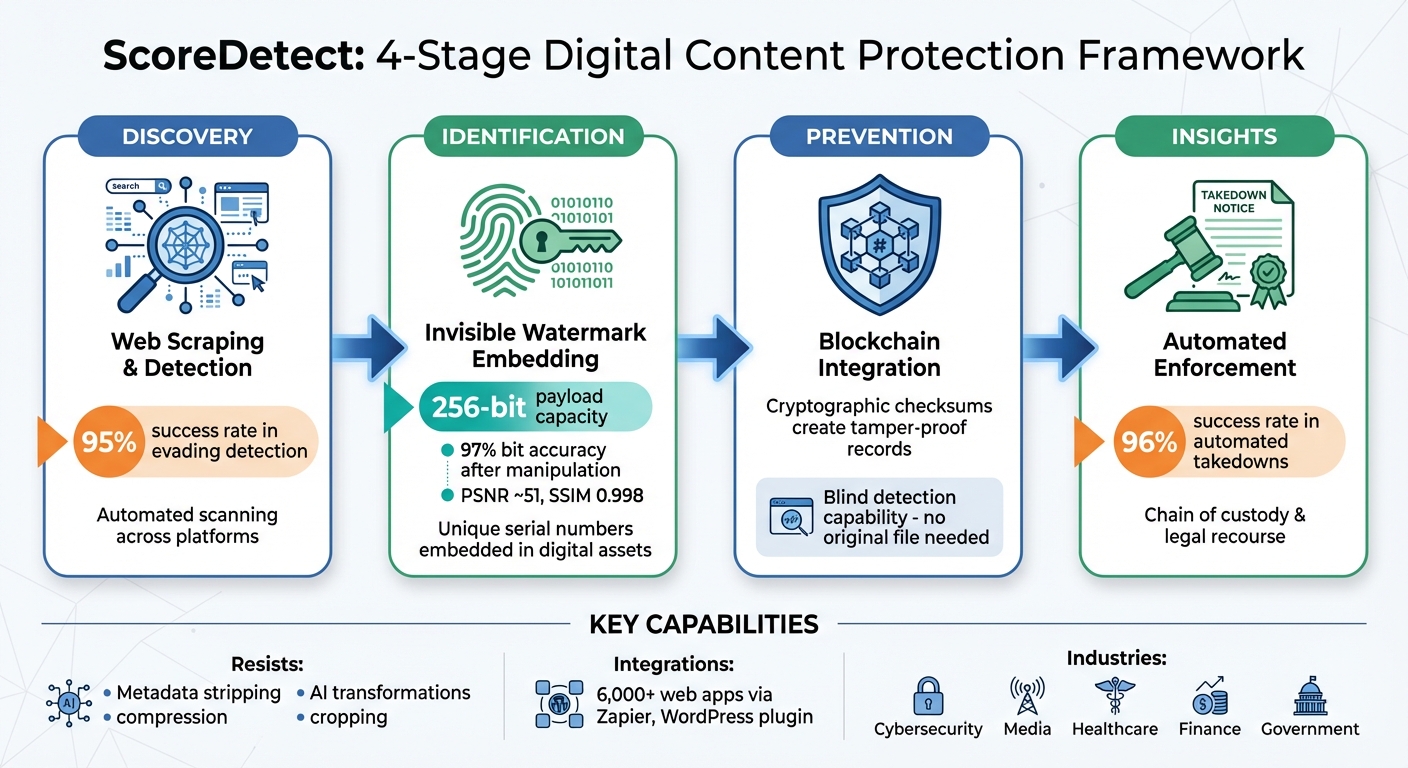
ScoreDetect takes invisible watermarking to the next level, offering a robust solution for enterprises looking to combat deepfake threats. Its approach is built on a four-part framework – Discovery, Identification, Prevention, and Insights – designed to provide ongoing protection for digital content [7].
Invisible Watermarking with ScoreDetect
At its core, ScoreDetect embeds an invisible, unique serial number into digital assets. This watermark resists common challenges like metadata stripping and advanced AI transformations, including inpainting, style transfer, and frame interpolation [7]. By using perceptual modeling, the system strategically places watermarks in areas that are less noticeable to the human eye, preserving content quality while ensuring durability.
One standout feature is its blind detection capability. This allows the system to recover and verify watermarks using only the suspect file and a shared secret – no need for the original unwatermarked version. This makes large-scale, automated scans not only possible but efficient [7].
Complete Digital Asset Management
ScoreDetect provides a comprehensive digital content protection solution. It boasts a 95% success rate in evading detection during discovery and over 96% success in automated takedowns [7]. To further strengthen content security, it integrates blockchain technology to record cryptographic checksums, creating tamper-proof and immutable records without needing to store the full asset [7].
"Invisible watermarking becomes a strategic control point for authenticity, licensing, and provenance across images, video, audio, and documents."
– Nikhil John, InCyan [7]
Additionally, ScoreDetect connects seamlessly with over 6,000 web apps through Zapier and includes a WordPress plugin that automatically logs updates. This makes verifying digital assets directly on your platforms a smooth and efficient process.
These tools set the stage for a variety of industry-specific uses.
Industry Applications
ScoreDetect is tailored to industries where deepfake threats can have serious consequences:
- Cybersecurity and Legal: Digital forensics teams benefit from its defensible chain of custody and tamper-evident logs, ensuring evidence remains intact.
- Media and Entertainment: Protects premium video content across workflows involving multiple transcodes, resolutions, and bitrates, maintaining ownership even after heavy platform compression.
- Marketing and Advertising: Tracks broadcast usage and links derivative clips back to their original sources, helping measure campaign reach effectively.
- Healthcare: Safeguards medical imagery from manipulation, ensuring the accuracy of critical data.
- Finance and Banking: Secures sensitive documents against unauthorized sharing or tampering.
- Government Agencies: Maintains the integrity of official documents during processes like rasterization and format conversion.
Even on platforms like social media and user-generated content sites – where compression and overlays are common – ScoreDetect ensures that watermarks remain intact, providing reliable protection regardless of content modifications [7].
Best Practices for Using Invisible Watermarking
Selecting a Watermarking Solution
Picking the right invisible watermarking solution comes down to understanding the "watermarking triangle." This concept involves balancing three key factors: imperceptibility (ensuring the watermark doesn’t affect content quality), robustness (making sure the watermark survives edits and attacks), and capacity (the amount of data the watermark can carry) [7]. It’s impossible to maximize all three at once, so focus on what matters most for your specific needs.
To ensure your watermark remains invisible to users, conduct blind tests with representative audiences. This helps confirm that the watermark won’t degrade the content in ways that viewers or listeners would notice. Neural techniques are particularly effective for achieving near-perfect imperceptibility.
Look for solutions that support blind detection across multiple formats, including images, videos, audio, and documents. Additionally, test the solution against advanced AI-based edits like inpainting, style transfer, or background replacement, as these can strip away traditional metadata. Advanced watermarking techniques can maintain over 97% bit accuracy even after such manipulations. Modern methods can also encode payloads of up to 256 bits, which is enough to embed UUIDs with error correction codes [6].
"When platforms strip or ignore provenance metadata, robust invisible watermarking becomes a critical safety net that can help link assets back to their origin and licensing state." – Nikhil John, InCyan [7]
Once you’ve selected a robust solution, ensure it integrates smoothly into your existing workflows.
Adding Watermarking to Existing Systems
Begin by hosting a cross-functional workshop to map out your content flows and identify high-value assets. This collaborative step ensures that all stakeholders are aligned on which content types – such as premium video or distinctive brand elements – are most sensitive and require protection [7].
Next, identify common transformations your content undergoes, such as compression for social media or AI-based edits. Validate the watermarking solution against these scenarios, including those used by your distribution partners, to ensure it holds up [7]. Additionally, make sure the watermarking process integrates efficiently with your current encoding or transcoding systems.
Set up a verification pipeline with clear stages: ingest, extraction, reference matching, and confidence scoring. This structured approach creates a defensible chain of custody using immutable logs and cryptographic hashes [7]. This step strengthens the overall security framework of your content management process.
For partner ecosystems, consider offering an API-based verification service. This allows third parties to confirm licensing status without exposing your proprietary algorithms. Tools like ScoreDetect can simplify this process by providing integrations, such as a Zapier connection with over 6,000 web apps and a WordPress plugin that logs updates directly onto the blockchain.
Conclusion
Invisible watermarking has emerged as a powerful tool in the fight against deepfake threats. Unlike metadata, which can be easily removed or altered, invisible watermarks act as a resilient digital signature embedded directly into the media itself. These watermarks can withstand challenges like compression, cropping, and even advanced AI manipulations such as inpainting or style transfer[7].
Today’s watermarking techniques achieve impressive results, maintaining over 97% bit accuracy and encoding up to 256 bits. They strike a careful balance between being undetectable to the human eye, remaining robust under various transformations, and offering enough capacity to support blind detection across different media formats[6][7].
These technical strengths bring clear business benefits. ScoreDetect, for example, leverages these advanced watermarking methods to deliver a comprehensive digital protection solution. It combines invisible watermarking with intelligent web scraping – achieving a 95% success rate in bypassing prevention measures – along with content matching and automated takedown notices, which boast a 96% success rate. The addition of blockchain integration ensures a tamper-proof chain of custody, while Zapier connections and a WordPress plugin simplify integration into existing workflows.
As deepfake technology becomes more sophisticated, organizations that embrace invisible watermarking will be better equipped to safeguard their digital assets, uphold their brand reputation, and enforce intellectual property rights. By combining robust watermarking with automated detection and forensic tools, businesses can create a reliable framework for content authentication, ensuring trust and integrity in an era dominated by synthetic media.
FAQs
Can invisible watermarks survive AI edits like inpainting and style transfer?
Invisible watermarks aim to safeguard digital content, even when modifications are made. However, advanced AI techniques, such as inpainting and style transfer, can compromise their resilience. Studies reveal that methods like diffusion-based image editing can erode or completely eliminate these watermarks, particularly during targeted attacks. While they remain a useful tool for content protection, the rise of AI-driven editing poses challenges to their long-term reliability.
How is invisible watermarking different from metadata for proving ownership?
Invisible watermarking works by embedding hidden data directly into media files like images or videos. This method ensures the embedded information stays intact even after tampering, compression, or edits. On the other hand, metadata stores ownership details in file fields, but these can be easily removed or altered. Unlike metadata, invisible watermarks offer a more dependable way to verify ownership and maintain content authenticity, even when the media undergoes changes.
How does ScoreDetect verify content and trigger takedowns without the original file?
ScoreDetect leverages blockchain technology to create a checksum for the content, serving as a verifiable proof of ownership. This approach allows the platform to identify unauthorized usage and initiate takedown actions without needing access to the original digital file.